Question: If the input layer 'X' denote the one hot encoding of the vocabulary, e is the embedding layer, h1,2 are hidden layers with sigmoid
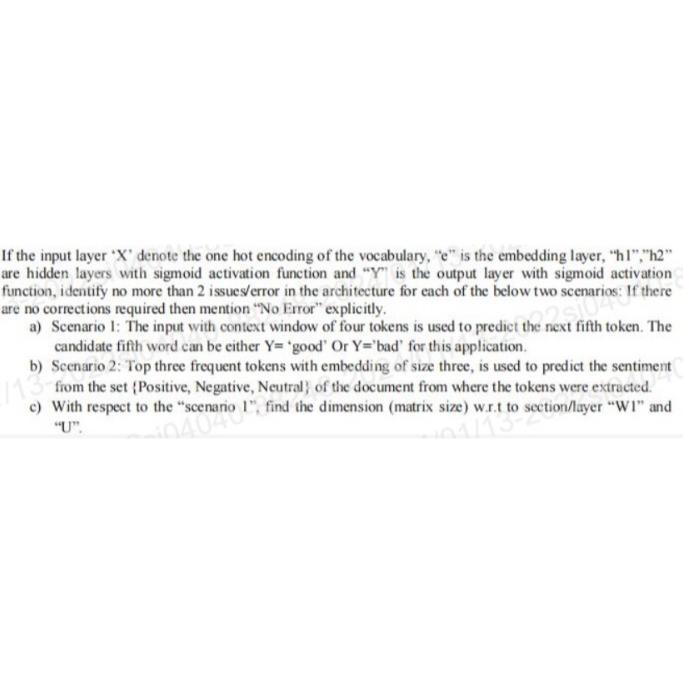
If the input layer 'X' denote the one hot encoding of the vocabulary, "e" is the embedding layer, "h1","2" are hidden layers with sigmoid activation function and "Y" is the output layer with sigmoid activation function, identify no more than 2 issues/error in the architecture for each of the below two scenarios: If there are no corrections required then mention "No Error" a) Scenario 1: The input with context window of four tokens is used to predict the next fifth token. The candidate fifth word can be either Y= 'good' Or Y='bad' for this application. b) Scenario 2: Top three frequent tokens with embedding of size three, is used to predict the sentiment 13 from the set (Positive, Negative, Neutral of the document from where the tokens were extracted. c) With respect to the "scenario 1", find the dimension (matrix size) w.r.t to section/layer "WI" and
Step by Step Solution
There are 3 Steps involved in it
The image presents a task which is likely related to a deep learning or neural network based assignment It refers to an architecture involving input layers embedding layers hidden layers with sigmoid ... View full answer

Get step-by-step solutions from verified subject matter experts


