Question: In order to send text using RSA, it is necessary to perform some type of text-to-number encoding first. For this question, we'll use a
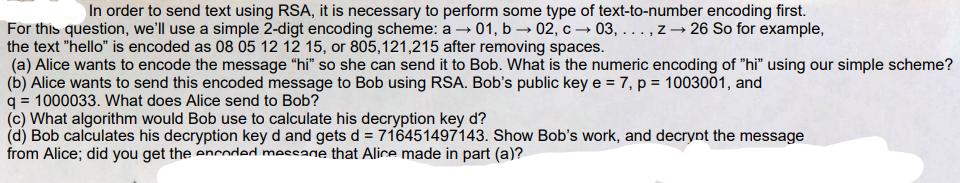
In order to send text using RSA, it is necessary to perform some type of text-to-number encoding first. For this question, we'll use a simple 2-digt encoding scheme: a 01, b 02, c 03,..., z 26 So for example, the text "hello" is encoded as 08 05 12 12 15, or 805,121,215 after removing spaces. (a) Alice wants to encode the message "hi" so she can send it to Bob. What is the numeric encoding of "hi" using our simple scheme? (b) Alice wants to send this encoded message to Bob using RSA. Bob's public key e = 7, p = 1003001, and q=1000033. What does Alice send to Bob? (c) What algorithm would Bob use to calculate his decryption key d? (d) Bob calculates his decryption key d and gets d = 716451497143. Show Bob's work, and decrypt the message from Alice; did you get the encoded message that Alice made in part (a)?
Step by Step Solution
3.37 Rating (156 Votes )
There are 3 Steps involved in it
The detailed ... View full answer

Get step-by-step solutions from verified subject matter experts


