Question: = In the Diffie-Hellman Key Exchange, let the public keys be p 79, g = 48, and the secret keys be a = 36
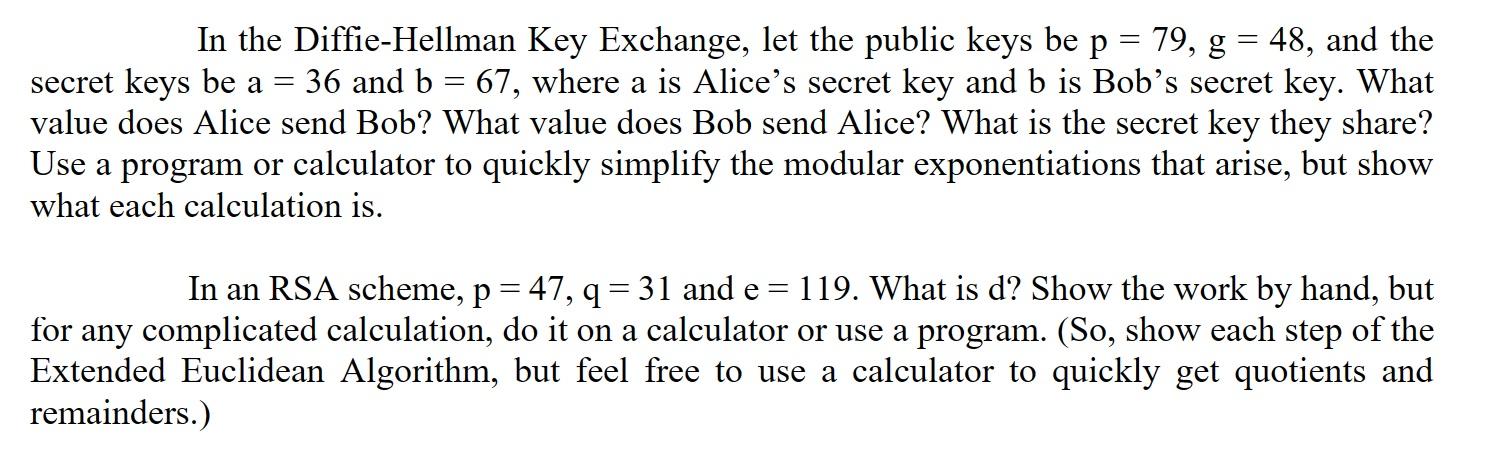
= In the Diffie-Hellman Key Exchange, let the public keys be p 79, g = 48, and the secret keys be a = 36 and b = 67, where a is Alice's secret key and b is Bob's secret key. What value does Alice send Bob? What value does Bob send Alice? What is the secret key they share? Use a program or calculator to quickly simplify the modular exponentiations that arise, but show what each calculation is. = In an RSA scheme, p = 47, q = 31 and e 119. What is d? Show the work by hand, but for any complicated calculation, do it on a calculator or use a program. (So, show each step of the Extended Euclidean Algorithm, but feel free to use a calculator to quickly get quotients and remainders.)
Step by Step Solution
There are 3 Steps involved in it
In the DiffieHellman Key Exchange the values given are Public keys p 79 g 48 Secret keys a 36 Alice ... View full answer

Get step-by-step solutions from verified subject matter experts


