Question: In your trace, you should be able to see the series of ICMP Echo Request (in the case of Windows machine) or the UDP
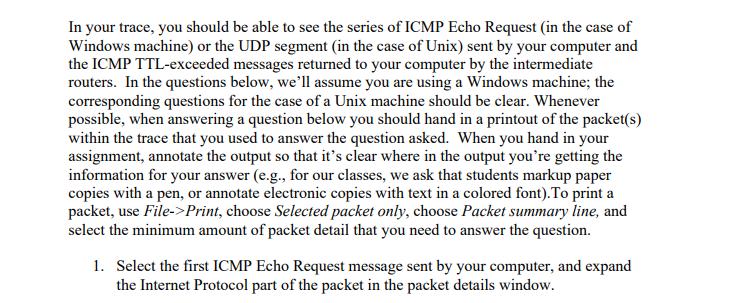



In your trace, you should be able to see the series of ICMP Echo Request (in the case of Windows machine) or the UDP segment (in the case of Unix) sent by your computer and the ICMP TTL-exceeded messages returned to your computer by the intermediate routers. In the questions below, we'll assume you are using a Windows machine; the corresponding questions for the case of a Unix machine should be clear. Whenever possible, when answering a question below you should hand in a printout of the packet(s) within the trace that you used to answer the question asked. When you hand in your assignment, annotate the output so that it's clear where in the output you're getting the information for your answer (e.g., for our classes, we ask that students markup paper copies with a pen, or annotate electronic copies with text in a colored font). To print a packet, use File->Print, choose Selected packet only, choose Packet summary line, and select the minimum amount of packet detail that you need to answer the question. 1. Select the first ICMP Echo Request message sent by your computer, and expand the Internet Protocol part of the packet in the packet details window. 000 Eile Edit View Go Capture Analyze Statistics Telephony Iools Internals Help Filter: No. Time 1 0.000000 2 4.866867 3 4.868147 4 5.363536 55.364799 65.864428 7 5.865461 8 6.163045 96.176826 10 6.188629 11 6.202957 12 6.208597 13 6.234505 Source Telebit 73:8d:ce 192.168.1.100 192.168.1.100 192.168.1.100 192.168.1.100 192.168.1.100 192.168.1.100 192.168.1.102 10.216.228.1 192.168.1.102 24.218.0.153 192.168.1.102 24.128.190.197 Fragment offset: 0 0000 00 06 25 da af 73 00 20 0010 30 54 32 do 00 00 01 01 0020 17 64 08 00 17 ca 03 00 0030 aa aa aa aa aa aa aa aa 3040 3050 an na an an na an an 88 0060 aa Frame (frame), 98 bytes TT 71 . Xip-ethereal-trace-1 [Wireshark 1.6.7 (SVN Rev 41973 from /trunk-1.6)] Frame 8: 98 bytes on wir (784 bits), 98 bytes captured (784 bits) Ethernet II, Src: Actionte_8a:70:la (00:20:e0:8a:70:la), Dst: LinksysG_da:af:73 (00:06:25:da:af:73) Internet Protocol Version 4, Sre: 192.168.1.102 (192.168.1.102), Dst: 128.59.23.100 (128.59.23.100) Version: 4 Header Length: 20 bytes Differentiated Services Field: 0x00 (DSCP 0x00: Default; ECN: 0x00: Not-ECT (Not ECN-Capable Transport)). Total Length: 84 Identification: 0x32d0 (13008) Flags: 0x00 80 Ba 70 la 08 00 45.00 2d 2c c0 a8 01 66 80 3b 50 03 37 32 20 aa aa aa 1 Destination. Broadcast 192.168.1.1 192.168.1.1 192.168.1.1 192.168.1.1 192.168.1.1 192.168.1.1 128.59.23.100 192.168.1.102 128.59.23.100 192.168.1.102 128.59.23.100 192.168.1.102 aa aa aa aa aa aa aa aa aa aa aa aa aa aa aa a tu ao mi ao da da lo Expression... Clear Apply 11 Protocol Length Info ARP UDP UDP UDP UDP UDP UDP ICMP ICMP ICMP ICMP ICMP ICMP 2 ALLERKE QQ F 7 Y ******* Packets: 380 Displayed: 380 Marked: 0 Load time: 0:00.006 In 60 who has 192.168.1.117? Tell 192.168.1.104 174 Source port: 30955 Destination port: ssdp 175 Source port: 30955 Destination port: ssdp 174 Source port: 30955 Destination port: ssdp 175 Source port: 30955 Destination port: ssdp 174 Source port: 30955 Destination port: ssdp 175 Source port: 30955 Destination port: ssdp 98 Echo (ping) request id=0x0300, seq=20483/848, ttl=1 70 Time-to-live exceeded (Time to live exceeded in transit) 98 Echo (ping) request id=0x0300, seq=20739/849, ttl=2 70 Time-to-live exceeded (Time to live exceeded in transit) 98 Echo (ping) request id=0x0300, seq=20995/850, ttl=3 70 Time-to-live exceeded (Time to live exceeded in transit) 25 101 Profile: Default 3050 3060 Frame (frame), 98 bytes Packets: 380 Displayed: 380 Marked: 0 Load time: 0:00.006 What is the IP address of your computer? Profile: Default 2. Within the IP packet header, what is the value in the upper layer protocol field? 3. How many bytes are in the IP header? How many bytes are in the payload of the IP datagram? Explain how you determined the number of payload bytes. 4. Has this IP datagram been fragmented? Explain how you determined whether or not the datagram has been fragmented. T+CE Next, sort the traced packets according to IP source address by clicking on the Source column header; a small downward pointing arrow should appear next to the word Source. If the arrow points up, click on the Source column header again. Select the first ICMP Echo Request message sent by your computer, and expand the Internet Protocol portion in the "details of selected packet header" window. In the "listing of captured packets" window, you should see all of the subsequent ICMP messages (perhaps with additional interspersed packets sent by other protocols running on your computer) below this first ICMP. Use the down arrow to move through the ICMP messages sent by your computer. 5. Which fields in the IP datagram always change from one datagram to the next within this series of ICMP messages sent by your computer? 6. Which fields stay constant? Which of the fields must stay constant? Which fields must change? Why? 7. Describe the pattern you see in the values in the Identification field of the IP datagram Next (with the packets still sorted by source address) find the series of ICMP TTL- exceeded replies sent to your computer by the nearest (first hop) router. 8. What is the value in the Identification field and the TTL field? 9. Do these values remain unchanged for all of the ICMP TTL-exceeded replies sent to your computer by the nearest (first hop) router? Why? Fragmentation Sort the packet listing according to time again by clicking on the Time column. 10. Find the first ICMP Echo Request message that was sent by your computer after you changed the Packet Size in pingplotter to be 2000. Has that message been fragmented across more than one IP datagram? [Note: if you find your packet has not been fragmented, you should download the zip file http://gaia.cs.umass.edu/wireshark-labs/wireshark-traces.zip and extract the ip- ethereal-trace-/packet trace. If your computer has an Ethernet interface, a packet size of 2000 should cause fragmentation.] 11. Print out the first fragment of the fragmented IP datagram. What information in the IP header indicates that the datagram been fragmented? What information in the IP header indicates whether this is the first fragment versus a latter fragment? How long is this IP datagram? The packets in the ip-ethereal-trace-/ trace file in http://gaia.cs.umass.edu/wireshark-labs/wireshark- traces.zip are all less that 1500 bytes. This is because the computer on which the trace was gathered has an Ethernet card that limits the length of the maximum IP packet to 1500 bytes (40 bytes of TCP/IP header data and 1460 bytes of upper-layer protocol payload). This 1500 byte value is the standard maximum length allowed by Ethernet. If your trace indicates a datagram longer 1500 bytes, and your computer is using an Ethernet connection, then Wireshark is reporting the wrong IP datagram length; it will likely also show only one large IP datagram rather than multiple smaller datagrams.. This inconsistency in reported lengths is due to the interaction between the Ethernet driver and the Wireshark software. We recommend that if you have this inconsistency, that you perform this lab using the ip-ethereal-trace-1 trace file. 12. Print out the second fragment of the fragmented IP datagram. What information in the IP header indicates that this is not the first datagram fragment? Are the more fragments? How can you tell? 13. What fields change in the IP header between the first and second fragment? Now find the first ICMP Echo Request message that was sent by your computer after you changed the Packet Size in pingplotter to be 3500. 14. How many fragments were created from the original datagram? 15. What fields change in the IP header among the fragments?
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


