Question: information Security . Based on Cryptography and Network Security book chapter 4. Question 4.11: Answer the following and explain your answer clearly at each step.
information Security .
Based on Cryptography and Network Security book chapter 4.
Question 4.11:
Answer the following and explain your answer clearly at each step. Especially b,e.
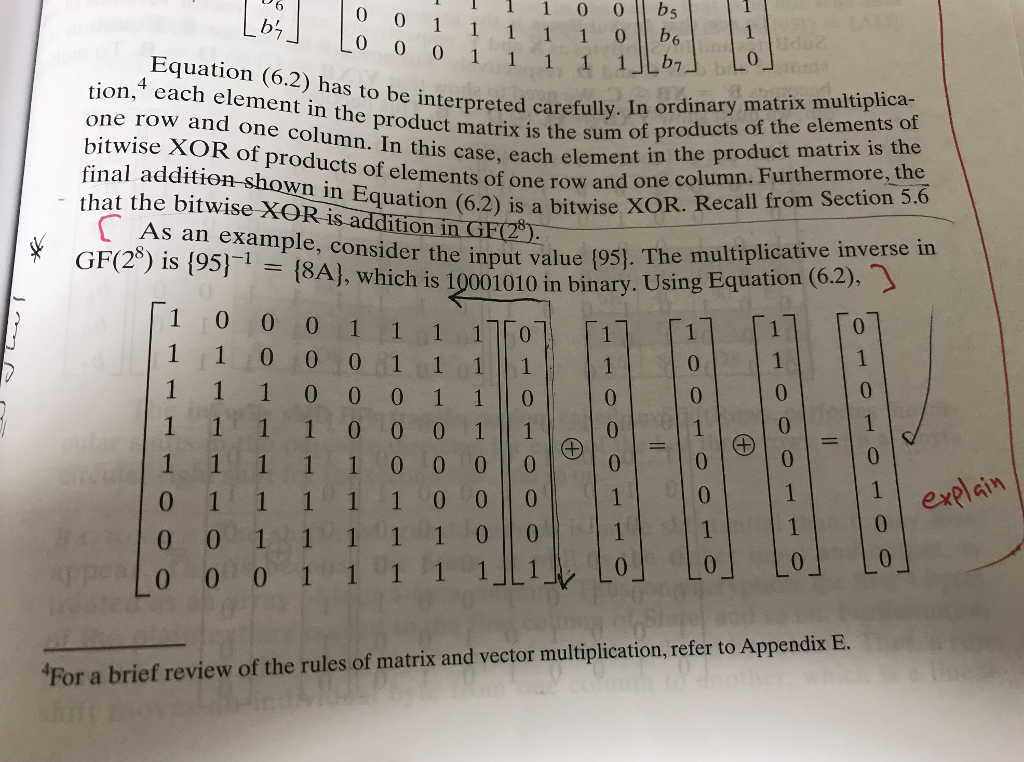
1 1 0 0 bs 1 1 1 1 Lb tion,4 cach element in the product the sufoduct one row and one column. In this case, each element in to be interpreted carefully. In ordinary matrix multiplica- that the bitwise () in Equation 6 of one row and one column. Furthermore, the that the bitwise XOR is additioni bitwise XOR of ercolumn. In this cnstrix is the sum of products of the elements of bitwise XOR of products of elements row an final additio shown in Equation (62) is a bitwise XOR. Recall from Section 5.6 As an example, consider the value GF(2) is {951-(8A], which is 10001010 in binary n.GE( put value (95). The multiplicative inverse in 1 0 0 0 1 1 1 10 1 0 0 0 0 0 0 0 0 0 exel For a brief review of the rules of matrix and vector multiplication, refer to Appendix E
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


