Question: INSTRUCTIONS: All problems should be written using JustBASIC. The code should be typed into the JustBASIC editor and executed. At the end of each
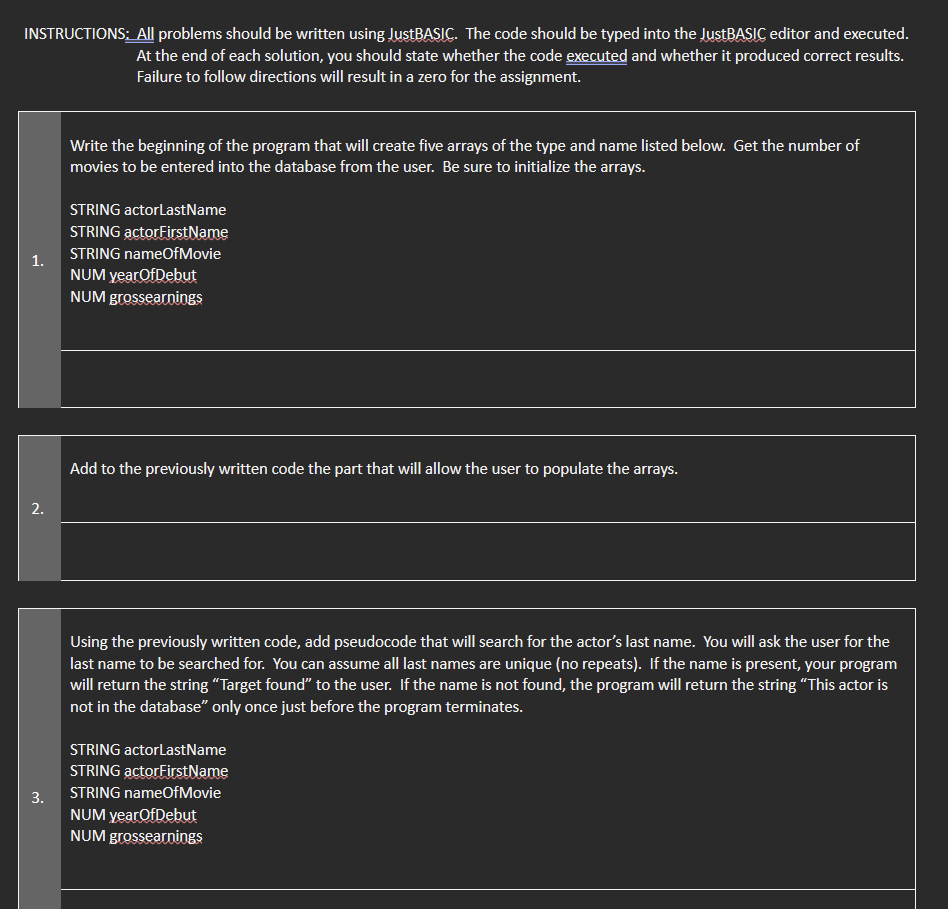
INSTRUCTIONS: All problems should be written using JustBASIC. The code should be typed into the JustBASIC editor and executed. At the end of each solution, you should state whether the code executed and whether it produced correct results. Failure to follow directions will result in a zero for the assignment. 1. 2. 3. Write the beginning of the program that will create five arrays of the type and name listed below. Get the number of movies to be entered into the database from the user. Be sure to initialize the arrays. STRING actorLastName STRING actorFirstName STRING nameOfMovie NUM year OfDebut NUM grossearnings Add to the previously written code the part that will allow the user to populate the arrays. Using the previously written code, add pseudocode that will search for the actor's last name. You will ask the user for the last name to be searched for. You can assume all last names are unique (no repeats). If the name is present, your program will return the string "Target found" to the user. If the name is not found, the program will return the string "This actor is not in the database" only once just before the program terminates. STRING actorLastName STRING actorFirstName STRING nameOfMovie NUM year Of Debut NUM grossearnings
Step by Step Solution
3.35 Rating (155 Votes )
There are 3 Steps involved in it
Step 1 Overview The question has asked to write a program in visual basic related to arrays Step 2 Create five arrays and get the number of movies fro... View full answer

Get step-by-step solutions from verified subject matter experts


