Question: is when data or information has not been altered or destroyed in unauthorized manner O a. Confidentiality b. Authenticity Oc Acountability Od. Integrity Oe. Availability
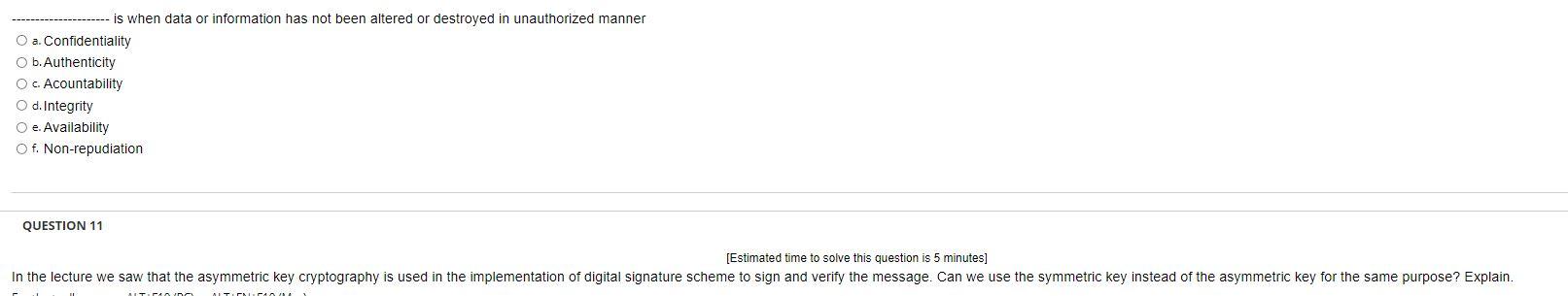
is when data or information has not been altered or destroyed in unauthorized manner O a. Confidentiality b. Authenticity Oc Acountability Od. Integrity Oe. Availability Of. Non-repudiation QUESTION 11 [Estimated time to solve this question is 5 minutes] In the lecture we saw that the asymmetric key cryptography is used in the implementation of digital signature scheme to sign and verify the message. Can we use the symmetric key instead of the asymmetric key for the same purpose? Explain. ITP ATENA is when data or information has not been altered or destroyed in unauthorized manner O a. Confidentiality b. Authenticity Oc Acountability Od. Integrity Oe. Availability Of. Non-repudiation QUESTION 11 [Estimated time to solve this question is 5 minutes] In the lecture we saw that the asymmetric key cryptography is used in the implementation of digital signature scheme to sign and verify the message. Can we use the symmetric key instead of the asymmetric key for the same purpose? Explain. ITP ATENA
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


