Question: Jaime wants to set up a tool that will allow him to capture and analyze attacker behavior, including command - line activity and uploaded toolkits
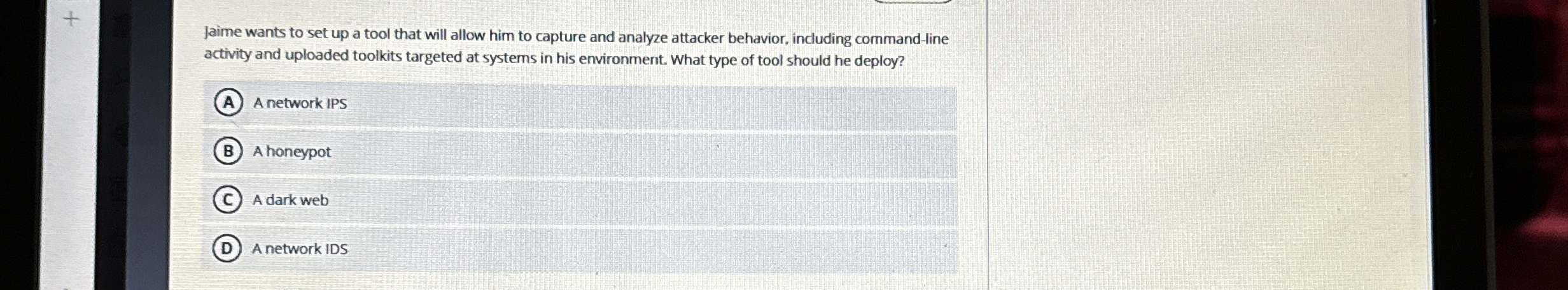
Jaime wants to set up a tool that will allow him to capture and analyze attacker behavior, including commandline activity and uploaded toolkits targeted at systems in his environment. What type of tool should he deploy?
A network IPS
A honeypot
A dark web
A network IDS
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


