John keeps a list on his cell phone of all the passwords he uses to access...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
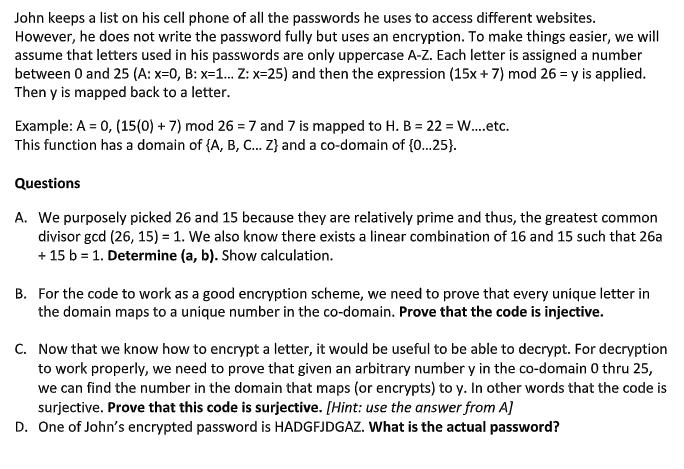
John keeps a list on his cell phone of all the passwords he uses to access different websites. However, he does not write the password fully but uses an encryption. To make things easier, we will assume that letters used in his passwords are only uppercase A-Z. Each letter is assigned a number between 0 and 25 (A: x=0, B: x=1... Z: x=25) and then the expression (15x+7) mod 26 = y is applied. Then y is mapped back to a letter. Example: A = 0, (15(0) + 7) mod 267 and 7 is mapped to H. B = 22 = W....etc. This function has a domain of {A, B, C... Z} and a co-domain of {0...25}. Questions A. We purposely picked 26 and 15 because they are relatively prime and thus, the greatest common divisor gcd (26, 15) = 1. We also know there exists a linear combination of 16 and 15 such that 26a + 15 b = 1. Determine (a, b). Show calculation. B. For the code to work as a good encryption scheme, we need to prove that every unique letter in the domain maps to a unique number in the co-domain. Prove that the code is injective. C. Now that we know how to encrypt a letter, it would be useful to be able to decrypt. For decryption to work properly, we need to prove that given an arbitrary number y in the co-domain 0 thru 25, we can find the number in the domain that maps (or encrypts) to y. In other words that the code is surjective. Prove that this code is surjective. [Hint: use the answer from A] D. One of John's encrypted password is HADGFJDGAZ. What is the actual password? John keeps a list on his cell phone of all the passwords he uses to access different websites. However, he does not write the password fully but uses an encryption. To make things easier, we will assume that letters used in his passwords are only uppercase A-Z. Each letter is assigned a number between 0 and 25 (A: x=0, B: x=1... Z: x=25) and then the expression (15x+7) mod 26 = y is applied. Then y is mapped back to a letter. Example: A = 0, (15(0) + 7) mod 267 and 7 is mapped to H. B = 22 = W....etc. This function has a domain of {A, B, C... Z} and a co-domain of {0...25}. Questions A. We purposely picked 26 and 15 because they are relatively prime and thus, the greatest common divisor gcd (26, 15) = 1. We also know there exists a linear combination of 16 and 15 such that 26a + 15 b = 1. Determine (a, b). Show calculation. B. For the code to work as a good encryption scheme, we need to prove that every unique letter in the domain maps to a unique number in the co-domain. Prove that the code is injective. C. Now that we know how to encrypt a letter, it would be useful to be able to decrypt. For decryption to work properly, we need to prove that given an arbitrary number y in the co-domain 0 thru 25, we can find the number in the domain that maps (or encrypts) to y. In other words that the code is surjective. Prove that this code is surjective. [Hint: use the answer from A] D. One of John's encrypted password is HADGFJDGAZ. What is the actual password?
Expert Answer:

Related Book For 

Quantitative Analysis for Management
ISBN: 978-0132149112
11th Edition
Authors: Barry render, Ralph m. stair, Michael e. Hanna
Posted Date:
Students also viewed these programming questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
List three specific parts of the Case Guide, Objectives and Strategy Section (See below) that you had the most difficulty understanding. Describe your current understanding of these parts. Provide...
-
Suppose that there is parity between the Australian dollar and the United States dollar. Let x be a positive number and assume that the United States dollar increases by 100x % in Australian dollars....
-
In terms of parameter a , random variable X has CDF (a) Show that E[X] = a by showing that E[X - (a-2)] = 2. (b) Generate m = 100 traces of sample mean Mn(X) of length n = 1000. Do you oobserve...
-
The debt ratio for Deutsche Auto for each of the last three years follows. Over this three year period, did the companys risk from financial leverage increase or decrease? Current Year 1 Year Ago 2...
-
Is there a single standard command-line processor to parse and process argv?
-
You are evaluating the results of a nonstatistical sample of 85 accounts receivable confirmations for the Bohrer Company. Information on the sample and population are included below. An overstatement...
-
On a private flight with capacity for 150 people, $800,000 per person is charged, plus $25,000 for each unsold seat on the plane. How many people must travel on the plane and what will be the price...
-
. With the information generated from the following table derivate from the Bureau of Economic Analysis (https://apps.bea.gov/iTable/index_nipa.cfm), please do the regression analysis, with the...
-
You will be researching three organizations in the same industry. Choose carefully--based on your analysis, one of these organizations will be the company you create a business plan for. Examples may...
-
Immediately following World War II, the quality of products produced by Japanese companies was not good enough to compete in the international marketplace. The only advantage Japanese companies had...
-
Compute the present value of a $100 investment to be made 6 months, 5 years, and 10 years from now at 4 percent interest. Explain why the present value is lower the further into the future the...
-
A professional baseball team set its sights on winning the World Series. The team owner wanted to win big and win fast. Consequently, the team sank all of its resources into trading for the best...
-
Suppose you identify 10 possible investments whose payoffs are completely independent of one another. All the investments have the same expected value and standard deviation. You have $1,000 to...
-
We have too much conflict in this organization, said Larry Parette. Nobody agrees on anything. Its beginning to get to me. Nonsense, Larry, said Mack Porter. We need conflict. Our best ideas come...
-
There is a term called "thermal pollution." Basically, industries have outlet streams at high temperatures they cannot use, so they dump it back into a stream or similar. Let's say you have a river...
-
Is times interest earned meaningful for utilities? Why or why not?
-
Ray Bond, from Problem 1-15, is trying to find a new supplier that will reduce his variable cost of production to $15 per unit. If he was able to succeed in reducing this cost, what would the...
-
A company has decided to order 360 units whenever the on-hand inventory falls to 90 units. There appears to be no seasonal fluctuation to the demand, but it does fluctuate daily and is approximately...
-
What are the major differences between PERT and CPM?
-
Show that, in Theorem 19.17, the quadratic variation \(\langle Mangle_{t}\) is a \(\mathscr{G}_{t}\) stopping time.Direct calculation, use Lemma 19.16.c) and A. 15 Data From Theorem 19.17 19.17...
-
The proof of Theorem 19.29 uses, implicitly, the following beautiful result due to Skorokhod [239] which is to be proved: Lemma. Let \(b:[0, \infty) ightarrow \mathbb{R}\) be a continuous function...
-
We have seen in Lemma 19.27.a) that \(\operatorname{supp}\left[d L_{t}^{0}(\omega) ight] \subset\left\{t \geqslant 0: B_{t}(\omega)=0 ight\}\) for almost all \(\omega\). Show that...

Study smarter with the SolutionInn App