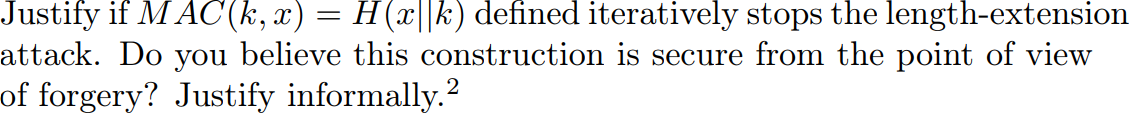
Question: Justify if MAC ( k , x ) = H ( x | | k ) defined iteratively stops the length - extension attack. Do
Justify if MACk x Hxk defined iteratively stops the lengthextension
attack. Do you believe this construction is secure from the point of view
of forgery? Justify informallyJustify if MAC defined iteratively stops the lengthextension
attack. Do you believe this construction is secure from the point of view
of forgery? Justify informally.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


