Question: Let E {0, 1} {0,1} {0,1} be a secure blockcipher. Consider the following deterministic MAC scheme ({0, 1), T, V) with the message space
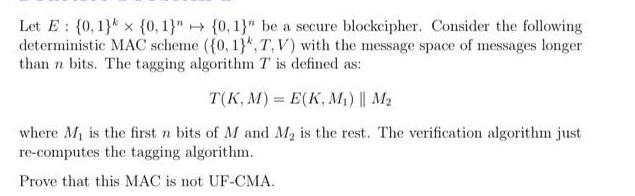
Let E {0, 1} {0,1}" {0,1}" be a secure blockcipher. Consider the following deterministic MAC scheme ({0, 1), T, V) with the message space of messages longer than n bits. The tagging algorithm T is defined as: T(K, M) = E(K, M) || M where M is the first n bits of M and M is the rest. The verification algorithm just re-computes the tagging algorithm. Prove that this MAC is not UF-CMA.
Step by Step Solution
3.42 Rating (155 Votes )
There are 3 Steps involved in it
In order to prove that the given MAC scheme is not UFCMA Unforgeable under ChosenMessage Attack we n... View full answer

Get step-by-step solutions from verified subject matter experts


