Question: Let F2 = {0, 1} with the usual arithmetic modulo 2. The set F2 = {0,1} consisting of all n-bit vectors (vectors of length
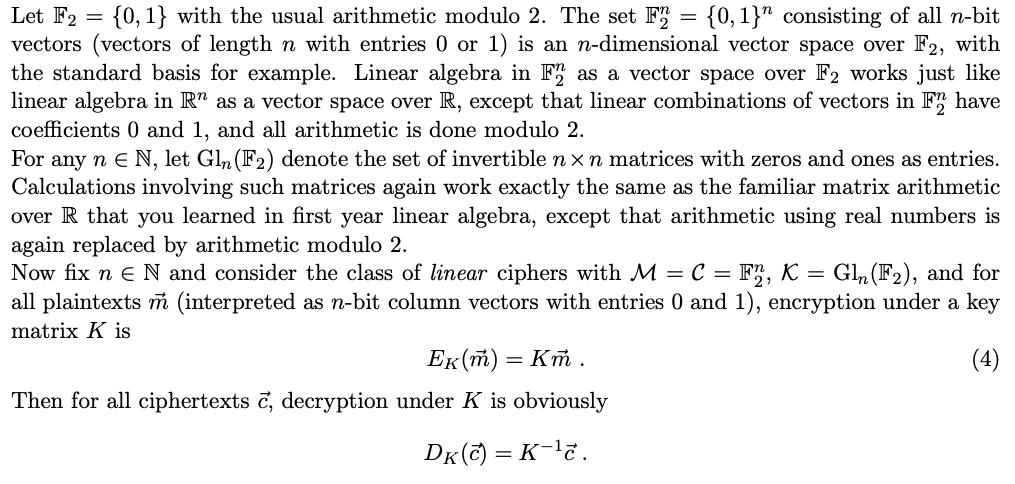

Let F2 = {0, 1} with the usual arithmetic modulo 2. The set F2 = {0,1}" consisting of all n-bit vectors (vectors of length n with entries 0 or 1) is an n-dimensional vector space over F2, with the standard basis for example. Linear algebra in F2 as a vector space over F2 works just like linear algebra in R" as a vector space over R, except that linear combinations of vectors in F2 have coefficients 0 and 1, and all arithmetic is done modulo 2. For any n E N, let Gln (F2) denote the set of invertible nxn matrices with zeros and ones as entries. Calculations involving such matrices again work exactly the same as the familiar matrix arithmetic over R that you learned in first year linear algebra, except that arithmetic using real numbers is again replaced by arithmetic modulo 2. Now fix n E N and consider the class of linear ciphers with M = C = F2, K = Gln (F), and for all plaintexts m (interpreted as n-bit column vectors with entries 0 and 1), encryption under a key matrix K is (4) Ek(m) = Km. Then for all ciphertexts c, decryption under K is obviously DK(C) = K-c.
Step by Step Solution
3.44 Rating (163 Votes )
There are 3 Steps involved in it
In the given context we are considering the class of linear ciphers using the matrix multiplication operation modulo 2 for encryption and decryption L... View full answer

Get step-by-step solutions from verified subject matter experts


