Question: Let ff be a function from {1,3,7}{1,3,7) to (2, 4, 6, 8}(2, 4, pairs f = {(7,4), (1, 2), (3,8)}. 2. Let f: Z
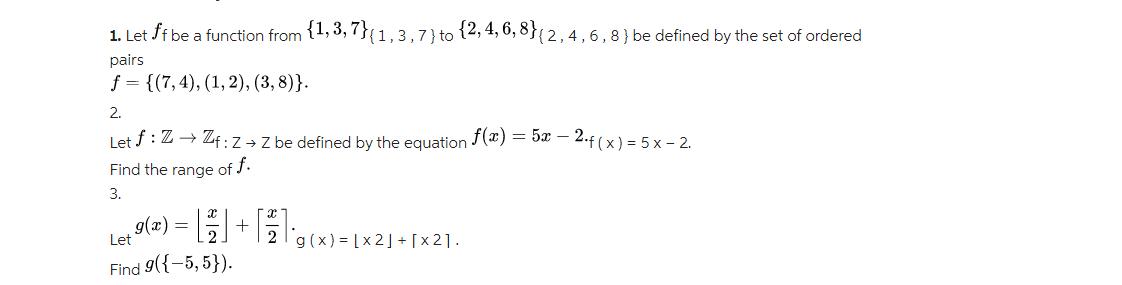
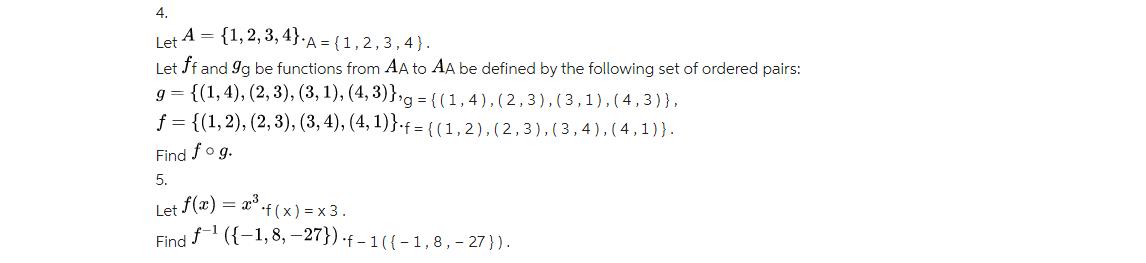
Let ff be a function from {1,3,7}{1,3,7) to (2, 4, 6, 8}(2, 4, pairs f = {(7,4), (1, 2), (3,8)}. 2. Let f: Z Zf: Z Z be defined by the equation f(x) = 5x - 2.f(x) = 5x - 2. Find the range of f. 3. [g(x)=1X2J+1x21. g(x) = Let Find 9({-5,5}). (2,4,6,8) be defined by the set of ordered + 4. Let A = {1,2,3,4}-A = *A= {1, 2, 3, 4). Let ff and gg be functions from AA to AA be defined by the following set of ordered pairs: g= {(1,4), (2,3), (3, 1), (4,3)},g = { g={(1,4), (2, 3), (3,1),(4,3)}, f = {(1, 2), (2, 3), (3, 4), (4,1)} = {(1, 2), (2,3), (3,4),(4,1)). Find fog. 5. Let f(x) = x.f(x) = x3. Find f({-1,8,-27}) -f-1((-1,8,-27 }).
Step by Step Solution
3.45 Rating (158 Votes )
There are 3 Steps involved in it
The detailed ... View full answer

Get step-by-step solutions from verified subject matter experts


