Question: Let (M.C, e, d, Ke, Ka) denote the RSA cryptosystem with public key (s, n) = (5, 26051) and private key t = 5141.
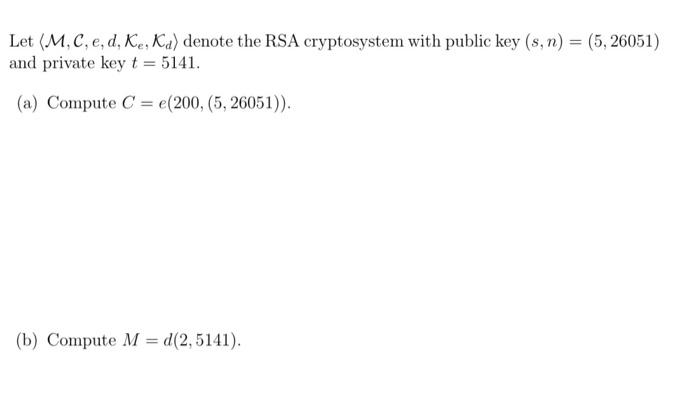
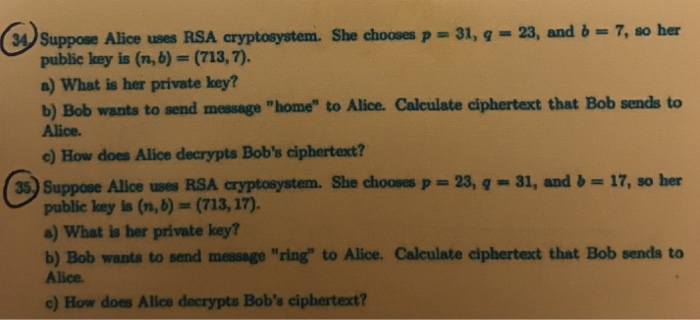
Let (M.C, e, d, Ke, Ka) denote the RSA cryptosystem with public key (s, n) = (5, 26051) and private key t = 5141. (a) Compute C = e(200, (5, 26051)). (b) Compute M = d(2,5141). 34 Suppose Alice uses RSA cryptosystem. She chooses p = 31, g = 23, and b = 7, so her public key is (n,b) = (713, 7). a) What is her private key? b) Bob wants to send message "home" to Alice. Calculate ciphertext that Bob sends to Alice. c) How does Alice decrypts Bob's ciphertext? 35.) Suppose Alice uses RSA cryptosystem. She chooses p=23, q= 31, and b=17, so her public key is (n, b) = (713, 17). a) What is her private key? b) Bob wants to send message "ring" to Alice. Calculate ciphertext that Bob sends to Alice. c) How does Alice decrypts Bob's ciphertext?
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


