Question: llustrate operation of common cryptographic protocols (e.g. encryption/decryption/ authentication/ Key Agreement) CLO4. Apply mathematical analysis to various cryptographic algorithms Question: Apply data Encryption Standard
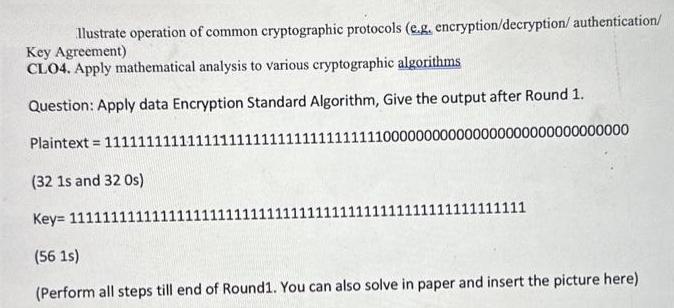
llustrate operation of common cryptographic protocols (e.g. encryption/decryption/ authentication/ Key Agreement) CLO4. Apply mathematical analysis to various cryptographic algorithms Question: Apply data Encryption Standard Algorithm, Give the output after Round 1. Plaintext= 11111111 11111000000000000000000000000000000 (32 1s and 32 Os) Key 1111111 (56 1s) (Perform all steps till end of Round1. You can also solve in paper and insert the picture here) 111111111
Step by Step Solution
3.48 Rating (158 Votes )
There are 3 Steps involved in it
To apply the Data Encryption Standard DES algorithm we need to follow several steps for each round of the process DES assumes a 64bit block of data an... View full answer

Get step-by-step solutions from verified subject matter experts


