Question: Make the following statements correct by changing one word or number. (Negating the sentence is not sufficient.) (i) A square-summable sequence is also called power
Make the following statements correct by changing one word or number. (Negating the sentence is not sufficient.) (i) A square-summable sequence is also called power signal. [1 mark] (ii) Adding together sine waves of the same frequency always results in another sine wave of the same phase. [1 mark] (iii) The Fourier transform of a Dirac comb is a Dirac impulse. [1 mark] (iv) 60 dBm = 1 W [1 mark] (b) Before resampling a digital image at a quarter of its original resolution, you want to apply an anti-aliasing low-pass filter. (i) If you apply a 1-dimensional filter with impulse response {hn} both horizontally and vertically to image pixels Ix,y, what are the resulting filtered pixel values ?Ix,y? [4 marks] (ii) What would be the discrete impulse response {hn} of an ideal low-pass filter for this application, if its length were of no concern? [4 marks] (iii) You decide to truncate the impulse response {hn} at its second zerocrossing on each side, resulting in a new impulse response {h n}. In the frequency domain, this results in H = H ? T for what function T? [4 marks] (iv) In order to make the frequency-domain response of your filter {h n} smoother, you convolve it in the frequency domain with a rectangular pulse, the width of which is twice the distance between the zero crossings of T. What does the resulting time-domain impulse response {h? n} look like? [4 marks
A synchronous hardware module has separate input and output ports that each convey. Handshaking is required on both ports since it is unpredictable whether the module or its environment are ready to exchange data in either direction at any time. Give diagram or RTL module definition for such a component and precisely describe the handshaking protocol in words. State the maximum throughput of your protocol. [5 marks] (d) Why might it be useful to have a formal specification of your protocol from part (c) during design and testing? What, if anything, might we infer about the number of words stored inside the module from the protocol? [4 marks] 13 Topical Issues (a) Compare and contrast the Internet of Things (IoT) with the conventional internet. (b) Describe how Bluetooth Low Energy (BLE) was designed to address the following IoT-related issues. Your answers should consider both BLE advertising and data channels. (i) Reduce the overall power consumption of peripherals. (ii) Handle radio channel contention from other IoT devices. (iii) Handle radio channel interference from other users of the same 2.4 GHz radio band such as WiFi
Consider the real-time transport of audio across a network. (a) What are the advantages of digitising the audio? [5 marks] (b) What are the disadvantages and how can they be mitigated? [5 marks] (c) What characteristics of the end-to-end channel across the network would be desirable, and how are these different from those which would be desirable for time-insensitive data? [5 marks] (d) Discuss the applicability of asynchronous and synchronous multiplexing in carrying real-time audio traffic. [5 marks]
(a) Distinguish between top-down, bottom-up and spiral (rapid prototype) development methodologies. Illustrate your answer with reference to an example of designing a building. [5 marks] (b) You are in charge of commissioning the design of a new building, such as the new Computer Laboratory building. Draw up a high-level GANTT chart for this task up to the letting of the building contract. [10 marks] (c) Discuss what monitoring and quality control procedures might apply to the design process. How will you get the agreement of the various stakeholders? [5 mark
This question concerns the representation of parse tree nodes for expressions composed of integer constants, identifiers, and integer operators for addition, subtraction, multiplication and division. In a typeless language, such as BCPL, each node can be implemented as a vector whose first element holds an integer identifying the node operator. The size of the vector and the kinds of value held in the other elements then depends on this node operator. (a) Complete the description of how you would represent such integer expressions in a typeless language. [5 marks]
(a) Describe briefly six factors which might influence or constrain the design of a new processor. [6 marks] (b) The performance of a superscalar processor is often enhanced with hardware to support the following: ? branch prediction ? register renaming ? out-of-order execution ? the speculative reordering of load instructions ? strided prefetching (i) Sketch an assembly language program that would benefit from the use of all of these techniques when executed on a superscalar processor. Briefly describe how each of the techniques helps to improve the performance of your program. [10 marks] (ii) Briefly outline two example programs for which the adoption of the techniques listed would not provide a significant performance improvement.
: write function that accepts three arguments: an array, the size of the array, and a number n. Assume that the array contains integers. The function should display all of the numbers in the array that are greater than the numbern Write program that dynamically takes in the name of the file to read.
(a) Give simple definition of the Prolog predicate dfx that can perform symbolic differentiation with respect to the variable x of expressions composed of integers (e.g. 0, 1, . . .), symbolic constants (e.g. a, b, . . .), symbolic variables (e.g. x, y, . . .) and the operators +, - and *, for addition, subtraction and multiplication. The first argument of dfx is the expression to differentiate and the second argument is the result. Your definition need not perform any simplification of the result. (b) Trace the execution of the call: dfx(x*x-2, R). [2 marks] (c) Now modify your definition so that it simplifies the result by the applications of rules such as: 1*x?x and x-0?x. [8 marks] (d) Discuss to what extent, if any, either of your predicates could be used to integrate an expression. [4 marks] 8 Databases (a) Describe the relational model of data. (b) Explain the following concepts in relational databases: (i) entity integrity constraint; (ii) foreign key and how it can specify a referential integrity constraint between two relations; [4 marks] (iii) semantic integrity constraint. [1 mark] (c) (i) What is a functional dependency? [1 mark] (ii) Define Boyce-Codd Normal Form (BCNF). [3 marks] (iii) Define Third Normal Form (3NF)
(a) The propositional formula ? contains four propositional letters: P, Q, R and S. This formula evaluates to true in every case except when Q and R are false while S is true. (i) What is the BDD for ?? [2 marks] (ii) What is the BDD for P ? ?? [3 marks] (iii) What is the BDD for the formula P ? S ? R? [2 marks] (iv) What is the BDD for the formula (P ? S ? R) ? ?? [4 marks] Use alphabetic ordering for all BDDs. (b) Use the DPLL procedure to determine whether or not the following set of clauses is satisfiable. {P, Q, R} {P, Q, R} {P, Q, R} {P, Q, R} {Q, R} {P, Q, R} [5 marks] (c) Prove the formula ?x[P(x) ? Q(x)]??x Q(x) ? ?x P(x) using the tableau calculus (with Skolemization). [4 marks] 7 [TURN OVER CST.2005.6.8 10 Foundations of Functional Programming (a) Give reduction rules associated with the standard combinators S, K and I. [4 marks] (b) Explain as simple a procedure as possible that converts lambda expressions into terms that use only these combinators. At this stage you are not expected to be concerned with efficiency, but you should make it clear why your combinator forms relate to the lambda expressions that you start with. [5 marks] (c) Illustrate the scheme you have given above by applying it to the lambda expression ?x.?y.((y x) y) and explain why in practical reduction to combinators at least additional symbols B and C are normally introduced. [5 marks] (d) Suppose that you have primitive functions available that can represent integers, booleans, arithmetic and an "if . . . then" operation (and so on, as necessary). Show how to convert the following ML-like code first into raw lambda calculus and then into combinator form: fun f n = if (iszero n) 1 (double (f (subtract1from n))); Note that the code has been presented in a way intended to show the functions used to perform arithmetic. You may assume the availability of a Y operator if that helps
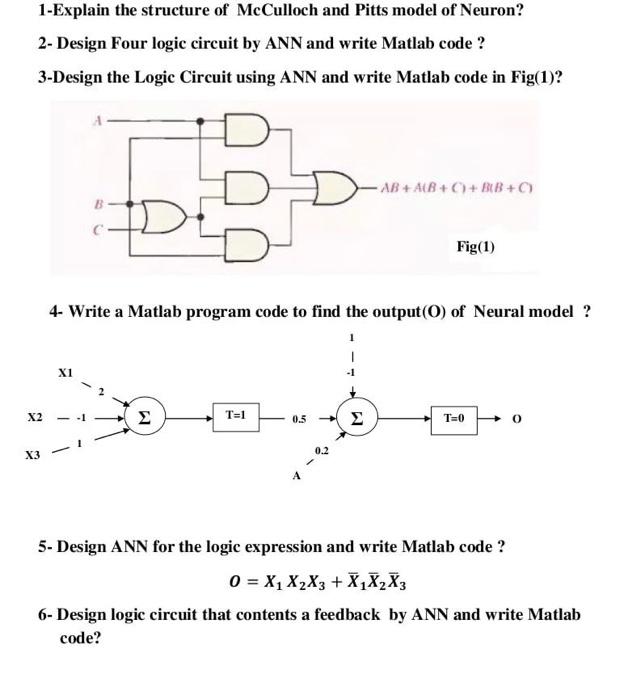
1-Explain the structure of McCulloch and Pitts model of Neuron? 2- Design Four logic circuit by ANN and write Matlab code ? 3-Design the Logic Circuit using ANN and write Matlab code in Fig(1)? X2 X1 IDE X3- 4- Write a Matlab program code to find the output (0) of Neural model ? T=1 0.5 -AB+A(B+C)+ BB+C) 0.2 Fig(1) T=0 0 5- Design ANN for the logic expression and write Matlab code ? 0 = X XX3 + XX X3 6- Design logic circuit that contents a feedback by ANN and write Matlab code?
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


