Match the Services and TCP/UDP ports to their definition. This is used for managing various networked...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
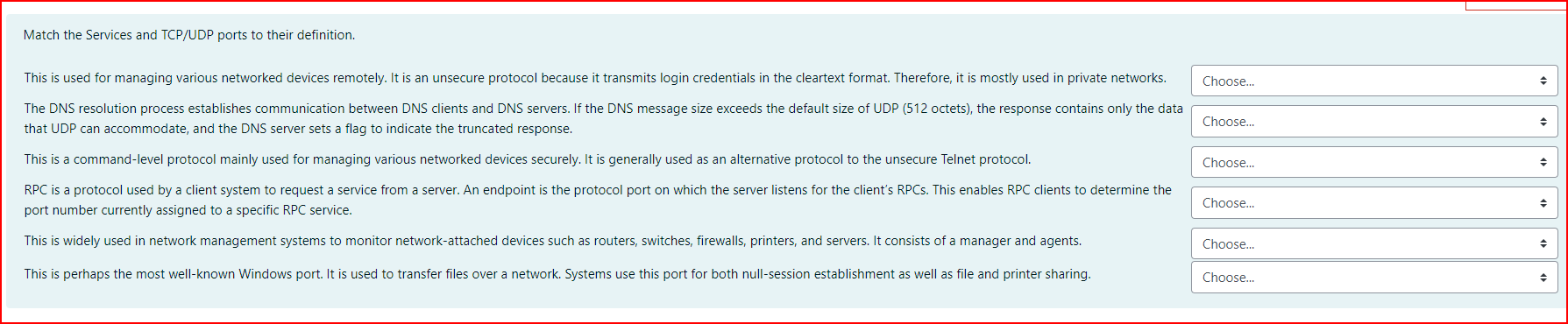
Match the Services and TCP/UDP ports to their definition. This is used for managing various networked devices remotely. It is an unsecure protocol because it transmits login credentials in the cleartext format. Therefore, it is mostly used in private networks. The DNS resolution process establishes communication between DNS clients and DNS servers. If the DNS message size exceeds the default size of UDP (512 octets), the response contains only the data that UDP can accommodate, and the DNS server sets a flag to indicate the truncated response. This is a command-level protocol mainly used for managing various networked devices securely. It is generally used as an alternative protocol to the unsecure Telnet protocol. RPC is a protocol used by a client system to request a service from a server. An endpoint is the protocol port on which the server listens for the client's RPCs. This enables RPC clients to determine the port number currently assigned to a specific RPC service. This is widely used in network management systems to monitor network-attached devices such as routers, switches, firewalls, printers, and servers. It consists of a manager and agents. This is perhaps the most well-known Windows port. It is used to transfer files over a network. Systems use this port for both null-session establishment as well as file and printer sharing. Choose... Choose... Choose... Choose... Choose... Choose... + Match the Services and TCP/UDP ports to their definition. This is used for managing various networked devices remotely. It is an unsecure protocol because it transmits login credentials in the cleartext format. Therefore, it is mostly used in private networks. The DNS resolution process establishes communication between DNS clients and DNS servers. If the DNS message size exceeds the default size of UDP (512 octets), the response contains only the data that UDP can accommodate, and the DNS server sets a flag to indicate the truncated response. This is a command-level protocol mainly used for managing various networked devices securely. It is generally used as an alternative protocol to the unsecure Telnet protocol. RPC is a protocol used by a client system to request a service from a server. An endpoint is the protocol port on which the server listens for the client's RPCs. This enables RPC clients to determine the port number currently assigned to a specific RPC service. This is widely used in network management systems to monitor network-attached devices such as routers, switches, firewalls, printers, and servers. It consists of a manager and agents. This is perhaps the most well-known Windows port. It is used to transfer files over a network. Systems use this port for both null-session establishment as well as file and printer sharing. Choose... Choose... Choose... Choose... Choose... Choose... + Match the Services and TCP/UDP ports to their definition. This is used for managing various networked devices remotely. It is an unsecure protocol because it transmits login credentials in the cleartext format. Therefore, it is mostly used in private networks. The DNS resolution process establishes communication between DNS clients and DNS servers. If the DNS message size exceeds the default size of UDP (512 octets), the response contains only the data that UDP can accommodate, and the DNS server sets a flag to indicate the truncated response. This is a command-level protocol mainly used for managing various networked devices securely. It is generally used as an alternative protocol to the unsecure Telnet protocol. RPC is a protocol used by a client system to request a service from a server. An endpoint is the protocol port on which the server listens for the client's RPCs. This enables RPC clients to determine the port number currently assigned to a specific RPC service. This is widely used in network management systems to monitor network-attached devices such as routers, switches, firewalls, printers, and servers. It consists of a manager and agents. This is perhaps the most well-known Windows port. It is used to transfer files over a network. Systems use this port for both null-session establishment as well as file and printer sharing. Choose... Choose... Choose... Choose... Choose... Choose... + Match the Services and TCP/UDP ports to their definition. This is used for managing various networked devices remotely. It is an unsecure protocol because it transmits login credentials in the cleartext format. Therefore, it is mostly used in private networks. The DNS resolution process establishes communication between DNS clients and DNS servers. If the DNS message size exceeds the default size of UDP (512 octets), the response contains only the data that UDP can accommodate, and the DNS server sets a flag to indicate the truncated response. This is a command-level protocol mainly used for managing various networked devices securely. It is generally used as an alternative protocol to the unsecure Telnet protocol. RPC is a protocol used by a client system to request a service from a server. An endpoint is the protocol port on which the server listens for the client's RPCs. This enables RPC clients to determine the port number currently assigned to a specific RPC service. This is widely used in network management systems to monitor network-attached devices such as routers, switches, firewalls, printers, and servers. It consists of a manager and agents. This is perhaps the most well-known Windows port. It is used to transfer files over a network. Systems use this port for both null-session establishment as well as file and printer sharing. Choose... Choose... Choose... Choose... Choose... Choose... +
Expert Answer:

Related Book For 

Accounting Information Systems
ISBN: 978-0133428537
13th edition
Authors: Marshall B. Romney, Paul J. Steinbart
Posted Date:
Students also viewed these computer network questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
A puck on a horizontal, frictionless surface is attached to a string that passes through a hole in the surface, as shown in FIGURE 11-52. As the puck rotates about the hole, the string is pulled...
-
The Lamp Company (TLC) currently makes and sells approximately 5,000 lamps per year. TLC recently received an offer from a new customer to purchase 500 lamps. TLC has the capacity to make the...
-
Write short notes on surging, choking, and stalling.
-
A square loop of wire has a perimeter of \(4.00 \mathrm{~m}\) and is oriented such that two of its parallel sides form a \(25.0^{\circ}\) angle with the horizontal. A uniform horizontal magnetic...
-
The Green Giraffe Restaurant Group has 21 restaurants scattered across the midwestern portion of the United States. Green Giraffe is not publicly held, but is owned by a small group of investors. For...
-
29. If A 21+j+k and B=1+2j+2k, find the magnitude of component of (A+B) along B: (1) 4 unit (2) 5 unit (3) 6 unit (4) 7 unit 30. Which of the following group of forces cannot produce the resultant of...
-
Suppose that a metal pin has a diameter that has a uniform distribution between 4.182 mm and 4.185 mm. (a)What is the probability that a pin will lit into a hole that has a diameter of 4.184 mm'.'...
-
In the beginning of 2018, the marketing director and the finance director of Gul Ahmed Holdings met to prepare a joint pricing recommendation for Item 007. Once the approval for their recommendation...
-
Discuss the value of a grievance procedure from each of the employer and employee union perspective
-
( ( i ) ) State and explain the various HTML elements in detail.? ( ( ii ) ) Explain the way in which data can be presented in tabular form using HTML?
-
Let's assume the inductor of the buck converter has an equivalent series inductance of R1, the diode forward voltage drop is Vf, and the load resistance is R with other devices being ideal. 1. Derive...
-
The drink booth at the school fair had these 4 types of drinks: orange juice, apple cider, ice tea, and lemonade. The students from Mr . Johnson's class were asked which drink they ordered. Here are...
-
Attached are the answers too. Explain what formulas were used? This process tells us where the change in value is going, but it sheds little light on where the change is coming from. Let's divide the...
-
Harvey Spectre started Pearson & Co. , a company law firm on April 1, 2021. The following information regarding the company is available: i. On 1 April, Harvey Spectre invested $80,000 cash to...
-
Should U.S. antidumping laws be stated in terms of average total costs or average variable costs?
-
Discuss several ways that ERM processes can be continuously monitored and modified so that deficiencies are reported to management.
-
The Family Support Center is a small charitable organization. It has only four full-time employees: two staff, an accountant, and an office manager. The majority of its funding comes from two...
-
For each of the following, discuss which data-gathering method(s) are most appropriate and why: a. Examining the adequacy of internal controls in the purchase requisition procedure. b. Identifying...
-
Browne Cleaning and Gardening Services commenced on 1 June 2026 when Lorne Browne contributed \($120\) 000 into a business bank account. Perhaps more thought could have been given to the business...
-
What orientation of an electric dipole in a uniform electric field has the greatest electric potential energy? What orientation has the least? (Let the system comprise both the electric dipole and...
-
A proton, a deuteron (a hydrogen nucleus containing one proton and one neutron), and an alpha particle (a helium nucleus consisting of two protons and two neutrons) initially at rest are all...

Study smarter with the SolutionInn App


