Question: Name the security principle(s) being applied in each scenario below and justify your answer. A web server is often run in a non-privileged account so
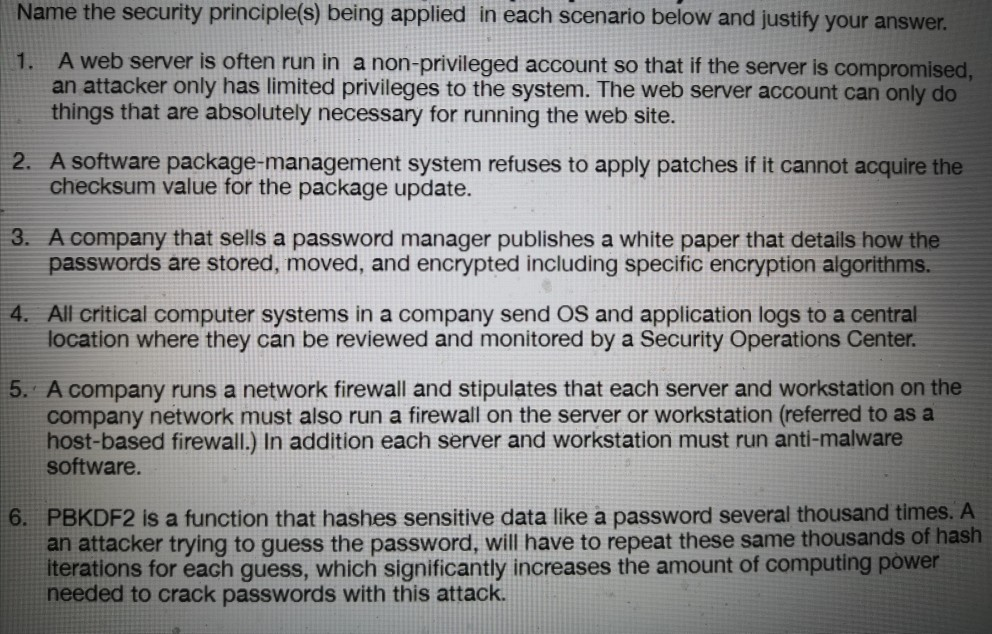
Name the security principle(s) being applied in each scenario below and justify your answer. A web server is often run in a non-privileged account so that if the server is compromised. an attacker only has limited privileges to the system. The web server account can only do things that are absolutely necessary for running the web site. 2. A software package-management system refuses to apply patches if it cannot acquire the checksum value for the package update. 3. A company that sells a password manager publishes a white paper that details how the passwords are stored, moved, and encrypted including specific encryption algorithms. 4. All critical computer systems in a company send OS and application logs to a central location where they can be reviewed and monitored by a Security Operations Center. 5. A company runs a network firewall and stipulates that each server and workstation on the company network must also run a firewall on the server or workstation (referred to as a host-based firewall.) In addition each server and workstation must run anti-malware software. 6. PBKDF2 is a function that hashes sensitive data like a password several thousand times. A an attacker trying to guess the password, will have to repeat these same thousands of hash iterations for each guess, which significantly increases the amount of computing power needed to crack passwords with this attack. Name the security principle(s) being applied in each scenario below and justify your answer. A web server is often run in a non-privileged account so that if the server is compromised. an attacker only has limited privileges to the system. The web server account can only do things that are absolutely necessary for running the web site. 2. A software package-management system refuses to apply patches if it cannot acquire the checksum value for the package update. 3. A company that sells a password manager publishes a white paper that details how the passwords are stored, moved, and encrypted including specific encryption algorithms. 4. All critical computer systems in a company send OS and application logs to a central location where they can be reviewed and monitored by a Security Operations Center. 5. A company runs a network firewall and stipulates that each server and workstation on the company network must also run a firewall on the server or workstation (referred to as a host-based firewall.) In addition each server and workstation must run anti-malware software. 6. PBKDF2 is a function that hashes sensitive data like a password several thousand times. A an attacker trying to guess the password, will have to repeat these same thousands of hash iterations for each guess, which significantly increases the amount of computing power needed to crack passwords with this attack
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


