Question: network q A protocol layer that runs over TCP to provide authentication and encryption of connection. A. Secure Socket Layer B. Encapsulating Security Payloads C.
network q
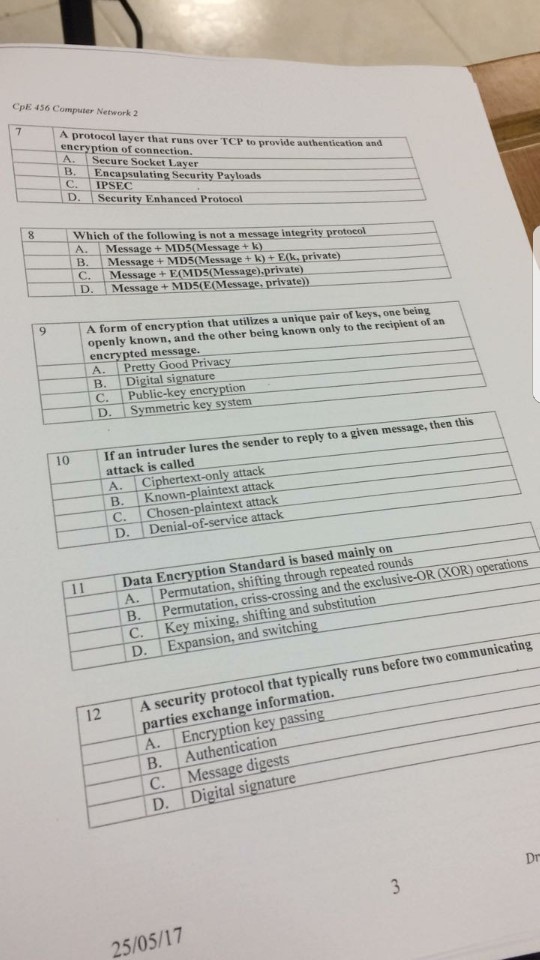
A protocol layer that runs over TCP to provide authentication and encryption of connection. A. Secure Socket Layer B. Encapsulating Security Payloads C. IPSEC D. Security Enhanced Protocol which of the following is not a message integrity protocol A. Message + MD5(Message + k) B. Message + MD5(Message E(k, private) C. Message + E(MD5Message), private) D. Message + E(MD5(E(Message private) A form of encryption that utilizes a unique pair of keys, one being an openly known, and the other being known only to the recipient of encrypted message. A. Pretty Good Privacy B. Digital signature C. Public- encryption. D. symmetric key system If an intruder lures the sender to reply to a given message, then this attack is called A. Ciphertext-only attack B. Known plaintext attack C. Chosen-plaintext attack D. Denial-of-service attack Data Encryption Standard based mainly on operations shifting through repeated rounds B. Permutation, criss-crossing and the exclusive OR(XOR)operations C. Key mixing, shifting and substitution D. Expansion, and switching A security protocol that typically runs before two communicating parties exchange information. A. Encryption key passing B. Authentication C. Message signature Digital signature
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


