Question: Networking Homework Virtual Private Network (VPN) A VPN is a private network established using a public network infrastructure, such as the Internet. Since the Internet
Networking Homework
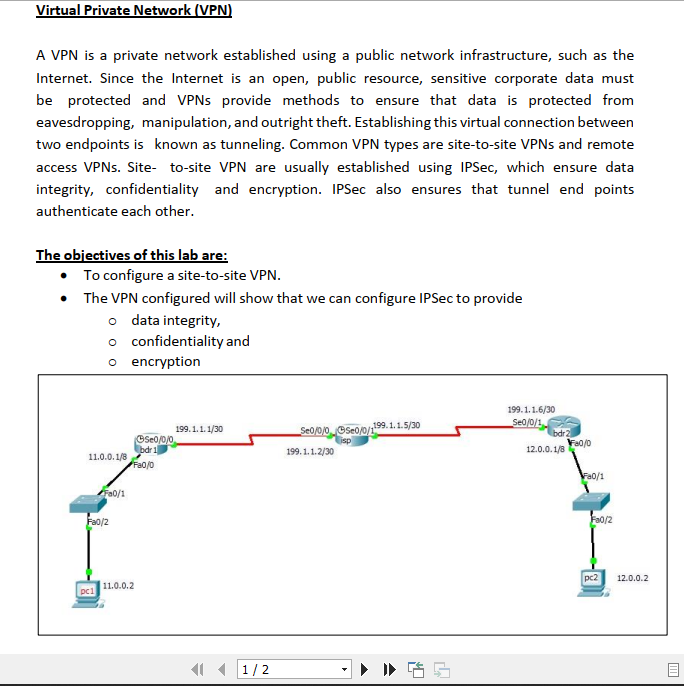
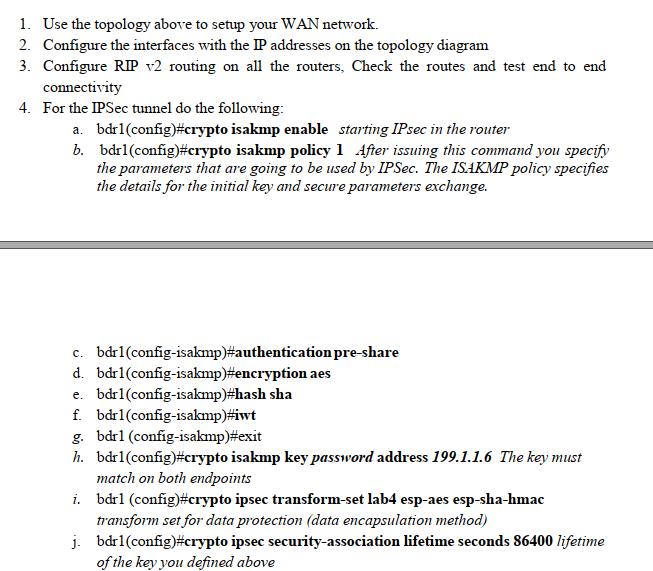
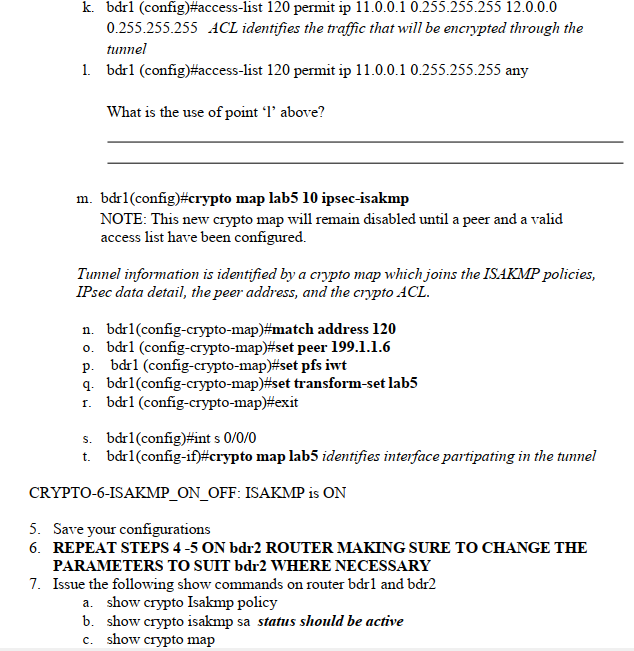
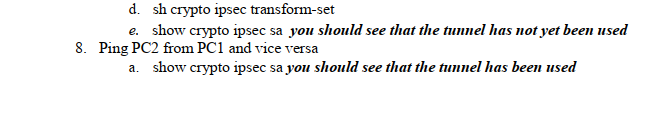
Virtual Private Network (VPN) A VPN is a private network established using a public network infrastructure, such as the Internet. Since the Internet is an open, public resource, sensitive corporate data must be protected and VPNs provide methods to ensure that data is protected from eavesdropping, manipulation, and outright theft. Establishing this virtual connection between two endpoints is known as tunneling. Common VPN types are site-to-site VPNs and remote access VPNs. Site- to-site VPN are usually established using IPSec, which ensure data integrity, confidentiality and encryption. IPSec also ensures that tunnel end points authenticate each other. The objectives of this lab are: To configure a site-to-site VPN. The VPN configured will show that we can configure IPSec to provide o data integrity, o confidentiality and o encryption 11.0.0.1/8 pc1 Fa0/1 Fa0/2 Se0/0/0 bdr 1 Fa0/0 11.0.0.2 199.1.1.1/30 1/2 199.1.1.5/30 Se0/0/0 Se0/0/1 199.1.1.2/30 4 199.1.1.6/30 Seo/0/1 bdr2 12.0.0.1/8 60/0 Fa0/1 Fa0/2 pc2 12.0.0.2 m
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


