Question: Oluo considers being aware of privilege and checking it is important in order to.... Obe happy O maintain that privilege take advantage of those
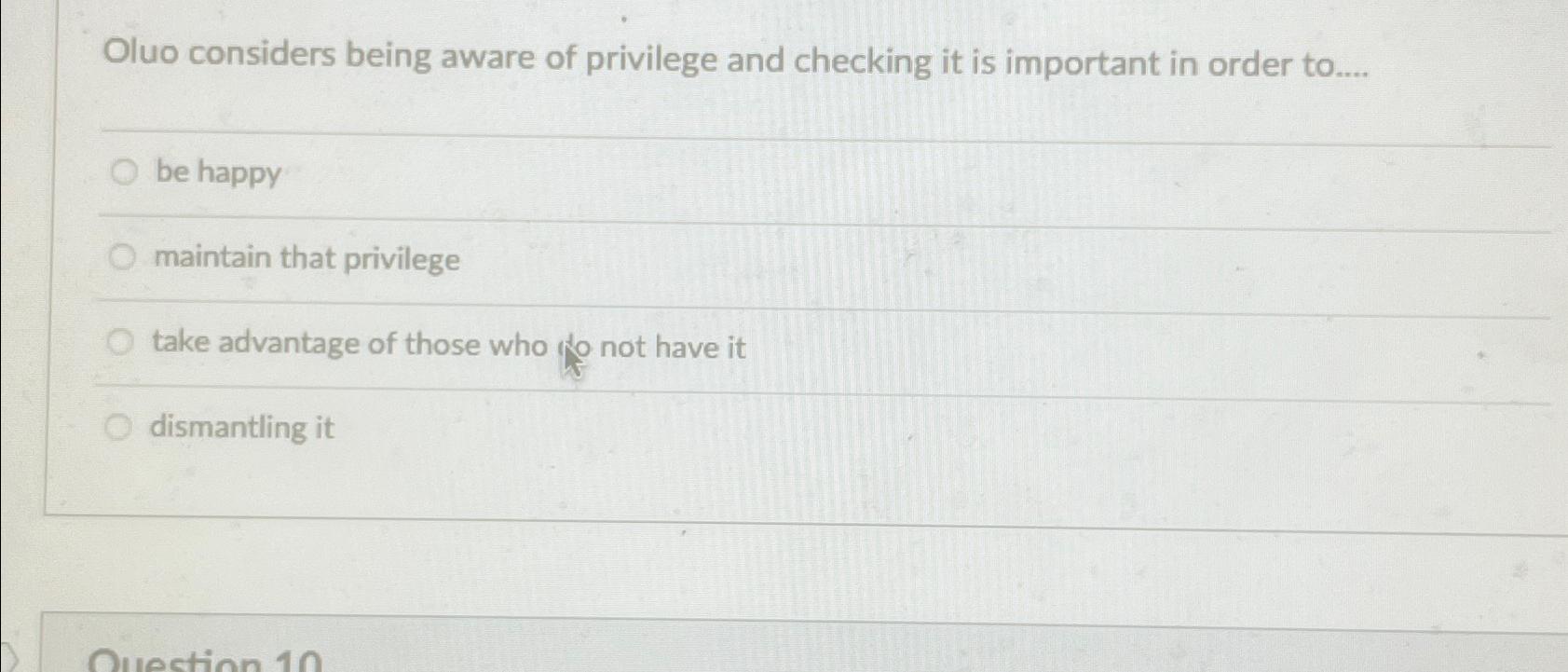
Oluo considers being aware of privilege and checking it is important in order to.... Obe happy O maintain that privilege take advantage of those who not have it O dismantling it Question 10
Step by Step Solution
3.46 Rating (159 Votes )
There are 3 Steps involved in it
The image displays a multiplechoice question which reads Oluo considers ... View full answer

Get step-by-step solutions from verified subject matter experts


