Question: One of the first steps in attacking a computer is to see which network ports are open. It is also an important step in network
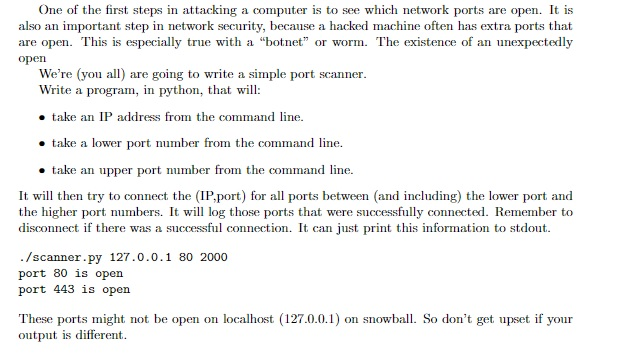
One of the first steps in attacking a computer is to see which network ports are open. It is also an important step in network security, because a hacked machine often has extra ports that are open. This is especially true with a "botnet or worm. The existence of an unexpectedly open We're (you) are going to write a simple port scanner Write a program, in python, that will: take an IP address from the command line e take a lower port number from the command line take an upper port number from the command line It will then try to connect the (IP,port) for all ports between (and including) the lower port and the higher port numbers. It will log those ports that were successfully connected. Remember to disconnect if there was a successful connection. It can just print this information to stdout ./scanner.py 127.0.0.1 80 2000 port 80 is open port 443 is open output is different One of the first steps in attacking a computer is to see which network ports are open. It is also an important step in network security, because a hacked machine often has extra ports that are open. This is especially true with a "botnet or worm. The existence of an unexpectedly open We're (you) are going to write a simple port scanner Write a program, in python, that will: take an IP address from the command line e take a lower port number from the command line take an upper port number from the command line It will then try to connect the (IP,port) for all ports between (and including) the lower port and the higher port numbers. It will log those ports that were successfully connected. Remember to disconnect if there was a successful connection. It can just print this information to stdout ./scanner.py 127.0.0.1 80 2000 port 80 is open port 443 is open output is different
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


