Question: Only need answer plz solve within 5 mints Suppose Alice needs to send an email to Bob. Seeing the email protocol used by Alice (mentioned
Only need answer plz solve within 5 mints
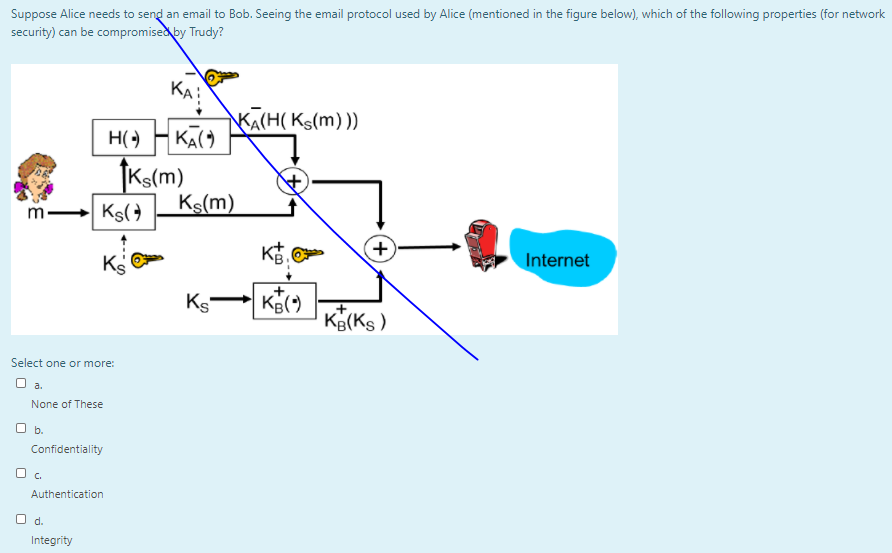
Suppose Alice needs to send an email to Bob. Seeing the email protocol used by Alice (mentioned in the figure below), which of the following properties (for network security) can be compromised by Trudy? KAI 4 m- KA(H(Ks(m))) H() HK- tks(m) Ks Ks(m) KB. Ks-KICM Kg(ks) + Ks Internet + Select one or more: a. None of these O b. Confidentiality Authentication O d. Integrity
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


