Part 1 (25 points): Unencrypted File Transfer In Part 1, you will use network sockets to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
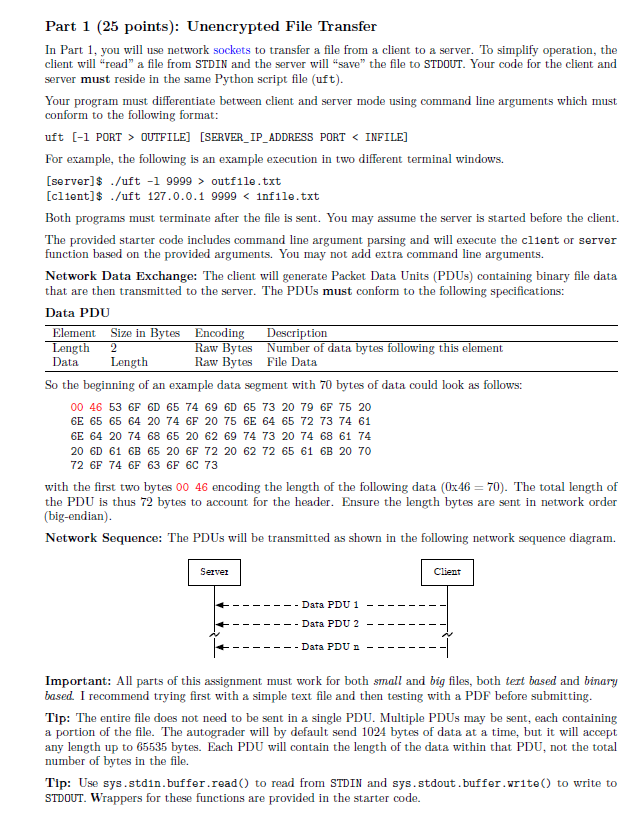
Part 1 (25 points): Unencrypted File Transfer In Part 1, you will use network sockets to transfer a file from a client to a server. To simplify operation, the client will "read" a file from STDIN and the server will "save" the file to STDOUT. Your code for the client and server must reside in the same Python script file (uft). Your program must differentiate between client and server mode using command line arguments which must conform to the following format: uft [-1 PORT > OUTFILE] [SERVER_IP_ADDRESS PORT < INFILE] For example, the following is an example execution in two different terminal windows. [server]$ ./uft -1 9999> outfile.txt [client]$ /uft 127.0.0.1 9999 < infile.txt Both programs must terminate after the file is sent. You may assume the server is started before the client. The provided starter code includes command line argument parsing and will execute the client or server function based on the provided arguments. You may not add extra command line arguments. Network Data Exchange: The client will generate Packet Data Units (PDUs) containing binary file data that are then transmitted to the server. The PDUs must conform to the following specifications: Data PDU Element Size in Bytes Encoding Length 2 Data Length Raw Bytes Raw Bytes Description Number of data bytes following this element File Data So the beginning of an example data segment with 70 bytes of data could look as follows: 00 46 53 6F 6D 65 74 69 6D 65 73 20 79 6F 75 20 6E 65 65 64 20 74 6F 20 75 6E 64 65 72 73 74 61 6E 64 20 74 68 65 20 62 69 74 73 20 74 68 61 74 20 6D 61 6B 65 20 6F 72 20 62 72 65 61 6B 20 70 72 6F 74 6F 63 6F 6C 73 with the first two bytes 00 46 encoding the length of the following data (0x46=70). The total length of the PDU is thus 72 bytes to account for the header. Ensure the length bytes are sent in network order (big-endian). Network Sequence: The PDUs will be transmitted as shown in the following network sequence diagram. Server Data PDU 1 Data PDU 2 Client - Data PDU n -1 Important: All parts of this assignment must work for both small and big files, both text based and binary based. I recommend trying first with a simple text file and then testing with a PDF before submitting. Tip: The entire file does not need to be sent in a single PDU. Multiple PDUs may be sent, each containing a portion of the file. The autograder will by default send 1024 bytes of data at a time, but it will accept any length up to 65535 bytes. Each PDU will contain the length of the data within that PDU, not the total number of bytes in the file. Tip: Use sys.stdn.buffer.read() to read from STDIN and sys.stdout. buffer.write() to write to STDOUT. Wrappers for these functions are provided in the starter code. Part 1 (25 points): Unencrypted File Transfer In Part 1, you will use network sockets to transfer a file from a client to a server. To simplify operation, the client will "read" a file from STDIN and the server will "save" the file to STDOUT. Your code for the client and server must reside in the same Python script file (uft). Your program must differentiate between client and server mode using command line arguments which must conform to the following format: uft [-1 PORT > OUTFILE] [SERVER_IP_ADDRESS PORT < INFILE] For example, the following is an example execution in two different terminal windows. [server]$ ./uft -1 9999> outfile.txt [client]$ /uft 127.0.0.1 9999 < infile.txt Both programs must terminate after the file is sent. You may assume the server is started before the client. The provided starter code includes command line argument parsing and will execute the client or server function based on the provided arguments. You may not add extra command line arguments. Network Data Exchange: The client will generate Packet Data Units (PDUs) containing binary file data that are then transmitted to the server. The PDUs must conform to the following specifications: Data PDU Element Size in Bytes Encoding Length 2 Data Length Raw Bytes Raw Bytes Description Number of data bytes following this element File Data So the beginning of an example data segment with 70 bytes of data could look as follows: 00 46 53 6F 6D 65 74 69 6D 65 73 20 79 6F 75 20 6E 65 65 64 20 74 6F 20 75 6E 64 65 72 73 74 61 6E 64 20 74 68 65 20 62 69 74 73 20 74 68 61 74 20 6D 61 6B 65 20 6F 72 20 62 72 65 61 6B 20 70 72 6F 74 6F 63 6F 6C 73 with the first two bytes 00 46 encoding the length of the following data (0x46=70). The total length of the PDU is thus 72 bytes to account for the header. Ensure the length bytes are sent in network order (big-endian). Network Sequence: The PDUs will be transmitted as shown in the following network sequence diagram. Server Data PDU 1 Data PDU 2 Client - Data PDU n -1 Important: All parts of this assignment must work for both small and big files, both text based and binary based. I recommend trying first with a simple text file and then testing with a PDF before submitting. Tip: The entire file does not need to be sent in a single PDU. Multiple PDUs may be sent, each containing a portion of the file. The autograder will by default send 1024 bytes of data at a time, but it will accept any length up to 65535 bytes. Each PDU will contain the length of the data within that PDU, not the total number of bytes in the file. Tip: Use sys.stdn.buffer.read() to read from STDIN and sys.stdout. buffer.write() to write to STDOUT. Wrappers for these functions are provided in the starter code.
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these algorithms questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
Describe how you plan to allocate your budget to each promotional activity. Provide a brief rationale. First, when developing a marketing budget plan, you want to start with the total budget...
-
How can industries identify the societal issues that are valued by millenials, support such needs and create awareness of such endeavours?
-
In a certain solar house, energy from the Sun is stored in barrels filled with water. In a particular winter stretch of five cloudy days, 1.00 x 106 kcal is needed to maintain the inside of the house...
-
Second law of thermodynamics defines: (a) Enthalpy (c) Heat (b) Entropy (d) Work
-
The income statement of Kneale Transport Inc. for the year ended December 31, 2014, reported the following condensed information: Kneale's statement of financial position contained the following...
-
What are the legal consequences of using corporate assets for personal use? Back it with primary sources like the internal revenue code, internal revenue manual, treasury regulations.
-
(a) Graph each of the following functions: 2 y = x y=x y=(x+9) y=(x-9) (b) Discuss the relationship between the graphs of part (a). (a) Use the graphing tool to graph the three equations on one...
-
1)Consider the crowding out model. Assume there are men and women in the labor force and three occupations: preschool, elementary and secondary teachers. Suppose only women can work as elementary and...
-
What type of cost does not change with changes in production volume?
-
An aluminum-alloy rod has a length of 9.2293 cm at 20.00C and a length of 9.2767 cm at the boiling point of water. (a) What is the length of the rod at the freezing point of water? (b) What is the...
-
1. Why have neo-classical economists generally argued that international economic relations are not zero-sum in character? What theoretical frameworks have they used to support this argument? It's...
-
In some labor markets, the supply of labor is as follows (where W represents wages and L represents the number of employees): W = 113 + 0.21L However, the demand for labor is: W = 958 -0.28L a) At...
-
Which g(x) gives the best approximation? Explain why? f (x) = x* + 2x2 x 3 1 x + 3 a G1 (x) = (: 1 x + 3 2 92 () ( 2 + 2 3x4 + 2x? + 3 93 (x) 4x3 + 4x 1 -
-
1. Advertising for eyeglasses _________ (increases/decreases) the price of eyeglasses because advertising promotes _________. 2. An advertisement that succeeds in getting consumers to try the product...
-
An image is 1600 1200 pixels with 3 bytes/pixel. Assume the image is uncompressed. How long does it take to transmit it over a 56-kbps modem channel? Over a 1-Mbps cable modem? Over a 10-Mbps...
-
A wireless LAN with one AP has 10 client stations. Four stations have data rates of 6 Mbps, four stations have data rates of 18 Mbps, and the last two stations have data rates of 54 Mbps. What is the...
-
Consider the extended LAN connected using bridges B1 and B2 in Fig. 4-41(b). Suppose the hash tables in the two bridges are empty. List all ports on which a packet will be forwarded for the following...
-
1. Describe the bases of power held by Dr. Jamie Thompson. Describe the bases of power held by Dr. Elizabeth Clarke. 2. What activities and people have contributed to Jaime Thompsons power? What...
-
What is the current in the wire in Figure Q22.1? 1.0 VR + 1.0-1.0V + FIGURE Q22.1
-
Electroconvulsive therapy is a last-line treatment for certain mental disorders. In this treatment, an electric current is passed directly through the brain, inducing seizures. The total charge that...

Study smarter with the SolutionInn App


