Question: Part 1 ( Setup your own secured webserver ) ( 5 points ) Objective 1 - Setup a Controlled Environment: Use a controlled lab with
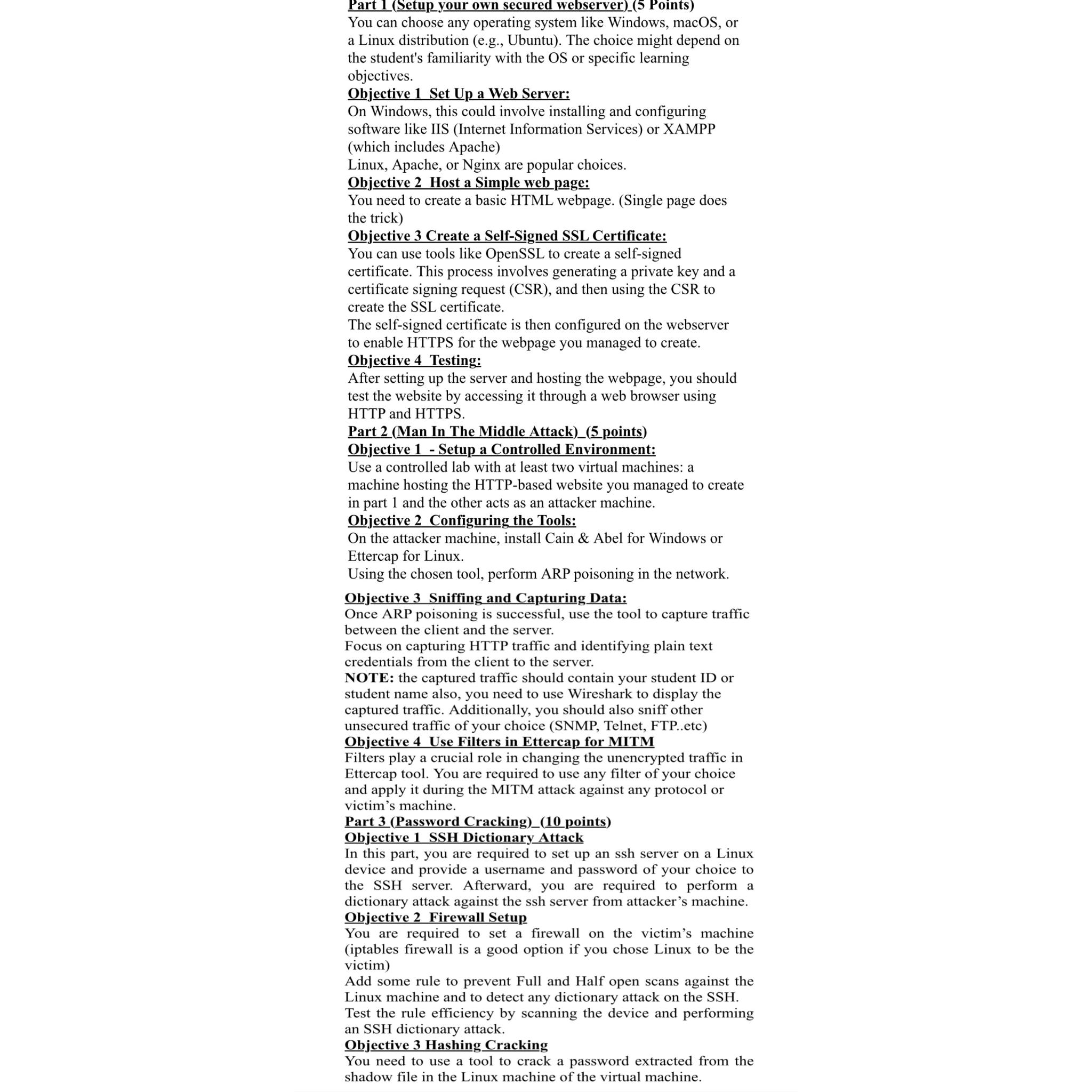
Part Setup your own secured webserver points
Objective Setup a Controlled Environment:
Use a controlled lab with at least two virtual machines: a machine hosting the HTTPbased website you managed to create in part and the other acts as an attacker machine.
Objective Configuring the Tools:
On the attacker machine, install Cain & Abel for Windows or Ettercap for Linux.
Using the chosen tool, perform ARP poisoning in the network.
Objective Sniffing and Capturing Data:
Once ARP poisoning is successful, use the tool to capture traffic between the client and the server.
Focus on capturing HTTP traffic and identifying plain text credentials from the client to the server.
NOTE: the captured traffic should contain your student ID or student name also, you need to use Wireshark to display the captured traffic. Additionally, you should also sniff other unsecured traffic of your choice SNMP Telnet, FTPetc
Objective Use Filters in Ettercap for MITM
Filters play a crucial role in changing the unencrypted traffic in Ettercap tool. You are required to use any filter of your choice and apply it during the MITM attack against any protocol or victim's machine.
Part Password Cracking points
Objective SSH Dictionary Attack
In this part, you are required to set up an ssh server on a Linux device and provide a username and password of your choice to the SSH server. Afterward, you are required to perform a dictionary attack against the ssh server from attacker's machine.
Objective Firewall Setup
You are required to set a firewall on the victim's machine iptables firewall is a good option if you chose Linux to be the victim
Add some rule to prevent Full and Half open scans against the Linux machine and to detect any dictionary attack on the SSH
Test the rule efficiency by scanning the device and performing an SSH dictionary attack.
Objective Hashing Cracking
You need to use a tool to crack a password extracted from the shadow file in the Linux machine of the virtual machine.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


