Question: People: Authentication and Authorization-Part 2 Once an organization has protected its intellectual capital by arming its people with a detailed information security plan, it can
People: Authentication and Authorization-Part 2 Once an organization has protected its intellectual capital by arming its people with a detailed information security plan, it can begin to focus on deploying technology to help combat attackers. There are three areas where technology aids in information security: authentication and authorization, prevention and resistance, and detection and response. The goal of this activity is for you to identify elements of the authentication and authorization area of information security. Instructions: Match each element to its correct description. 1 5 Sock Puppet Marketing HIPAA Security Rule 2 Astroturfing 6 Nonsensitive Pll 3 Sensitive PII Personally Identifiable Information (PII)
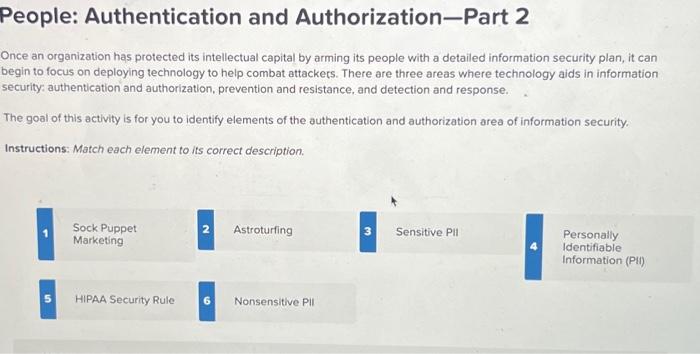
Once an organization has protected its intellectual capital by arming its people with a detailed information security plan, it can begin to focus on deploying technology to help combat attackers. There are three areas where technology aids in information security: authentication and authorization, prevention and resistance, and detection and response. The goal of this activity is for you to identify elements of the authentication and authorization area of information security. Instructions: Match each element to its correct description
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


