Question: Please answer all the 5 situations Attacks Instructions: Attacks may only be used once, and will disappear from drop down list if selected When you
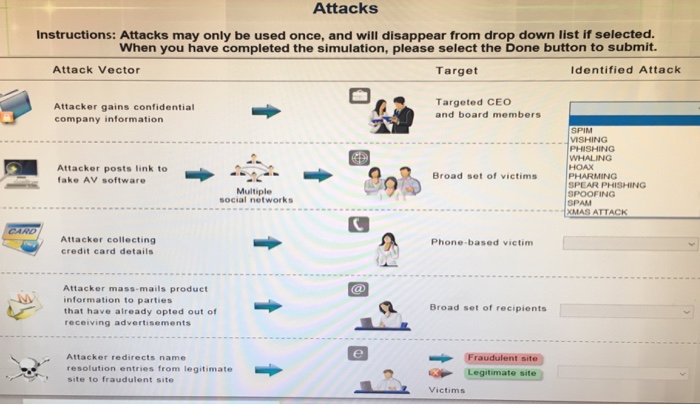
Attacks Instructions: Attacks may only be used once, and will disappear from drop down list if selected When you have completed the simulation, please select the Done button to submit. Attack Vector Target Identified Attack Attacker gains confidential company information Targeted CEO and board members MSHING PHISHING WHALING HOAX Attacker posts link to fake AV software fate AV sottwar 0 Broad set of victims Multiple social networks SPEAR PHISHING SPOOFING SPAM XMAS ATTACK Attacker collecting credit card details Phone-based victim Attacker mass-mails product Minformation to parties that have already opted out of receiving advertisements Broad set of recipients Fraudulent site -Legitimate site Attacker redirects name resolution entries from legitimate site to fraudulent site Victims
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


