Question: Please help answer this operating system question 1. Research the practice of key logging. Describe what it is, and explain why some people defend the
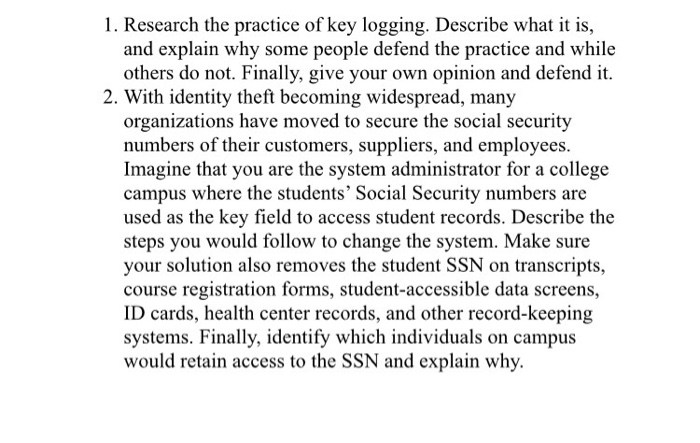
1. Research the practice of key logging. Describe what it is, and explain why some people defend the practice and while others do not. Finally, give your own opinion and defend it 2. With identity theft becoming widespread, many organizations have moved to secure the social security numbers of their customers, suppliers, and employees Imagine that you are the system administrator for a college campus where the students' Social Security numbers are used as the key field to access student records. Describe the steps you would follow to change the system. Make sure your solution also removes the student SSN on transcripts, course registration forms, student-accessible data screens, ID cards, health center records, and other record-keeping systems. Finally, identify which individuals on campus would retain access to the SSN and explain why
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


