Question: Please help me ASAP INSTRUCTIONS In this assignment, students are required to create PHP programs that will allow an authorized user enter mentor information into
Please help me ASAP
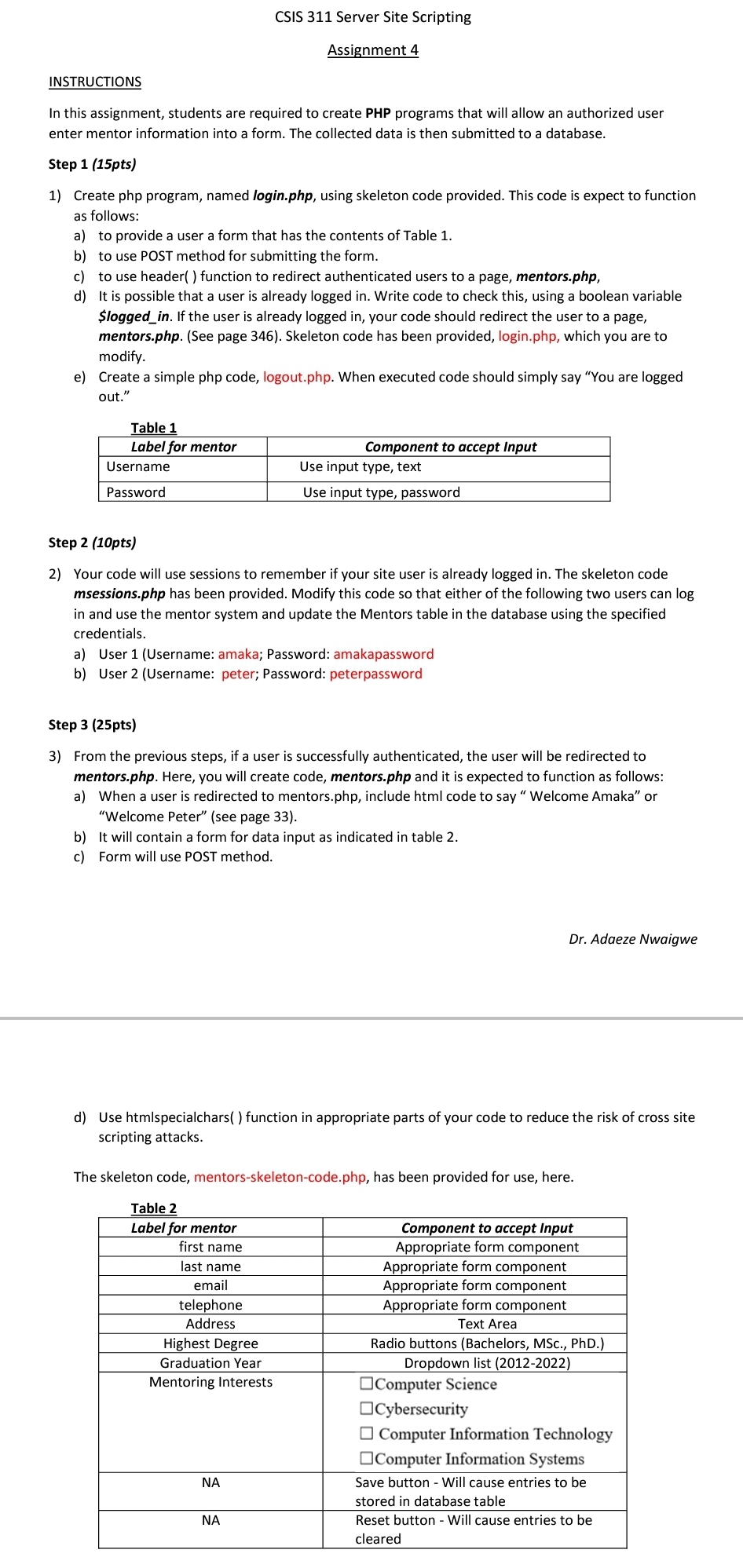
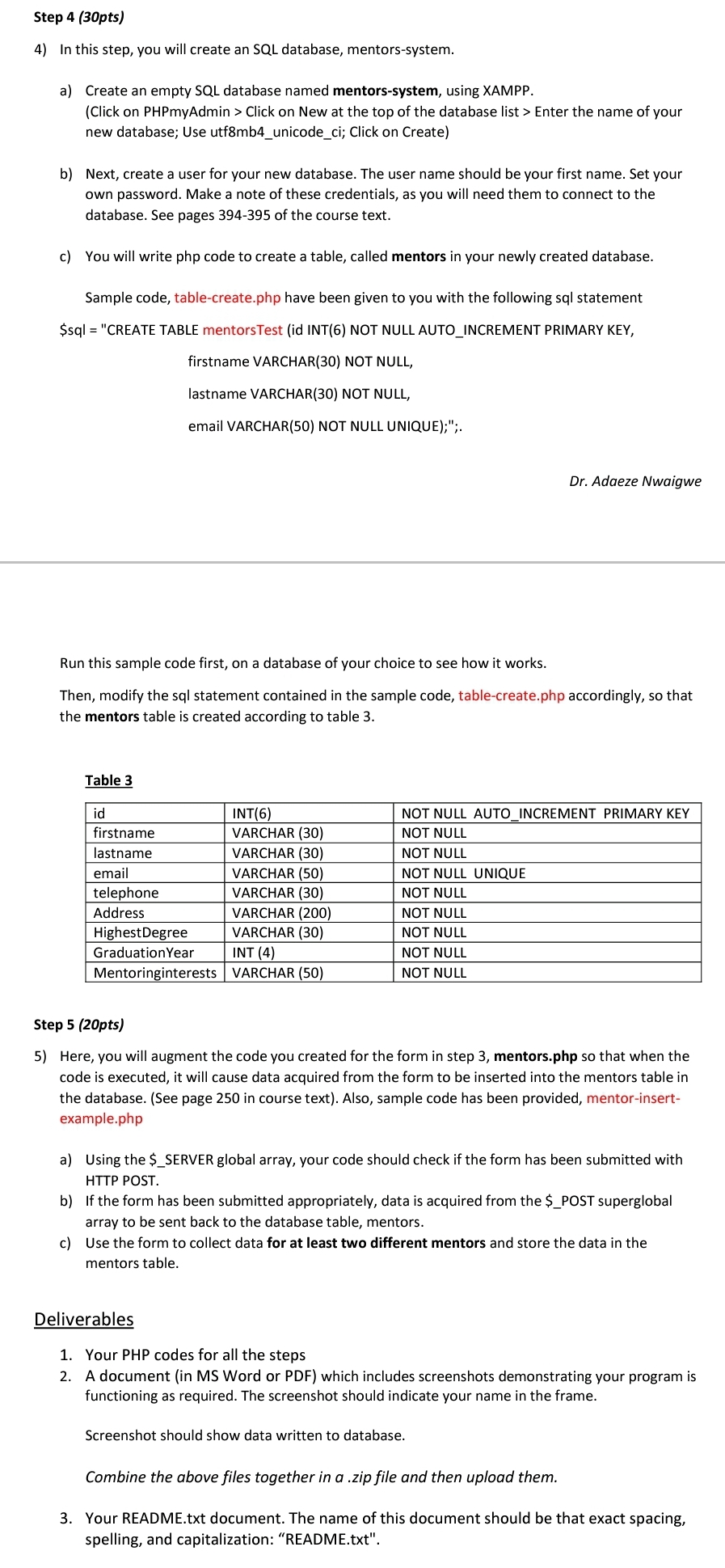
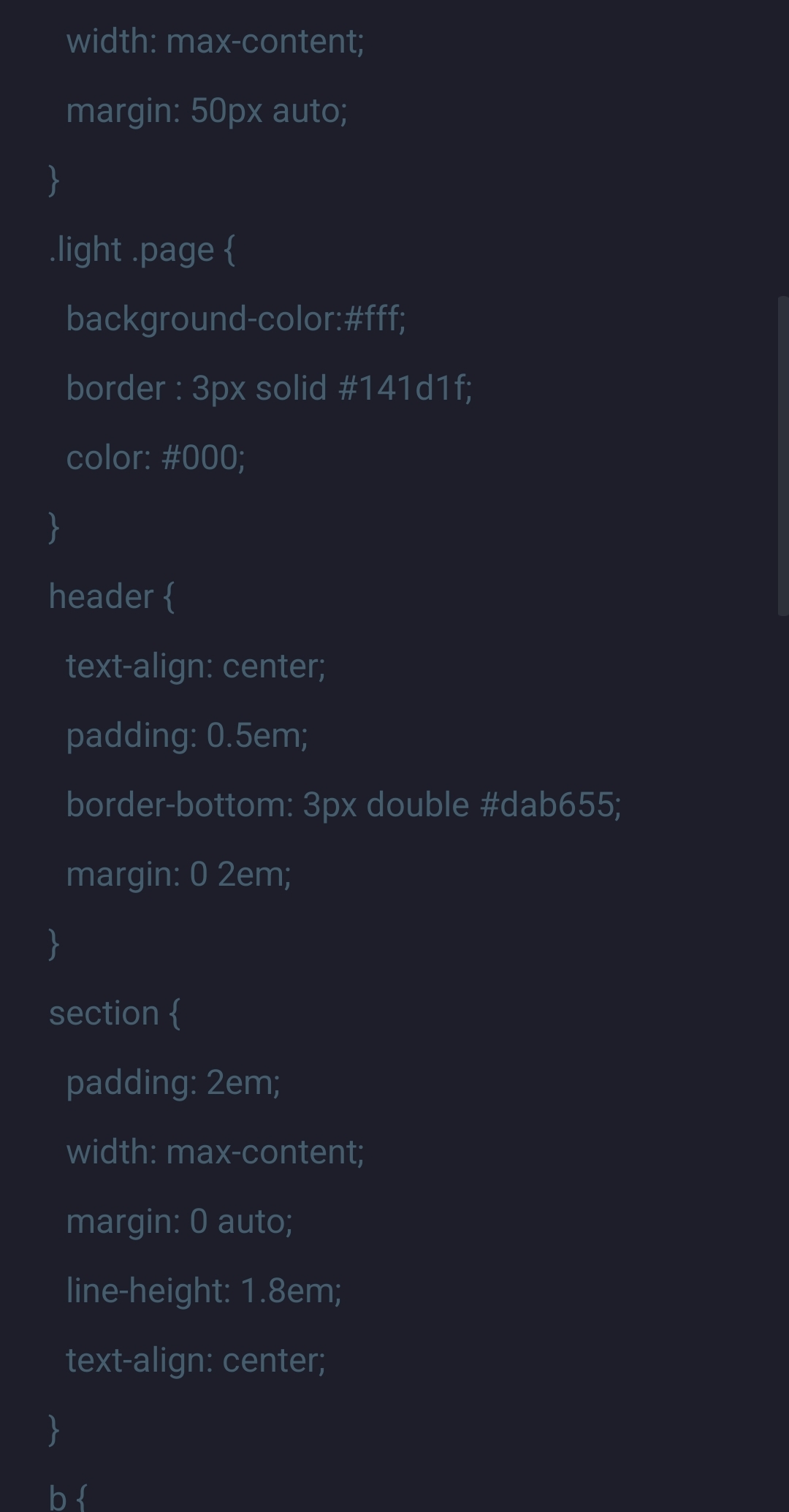
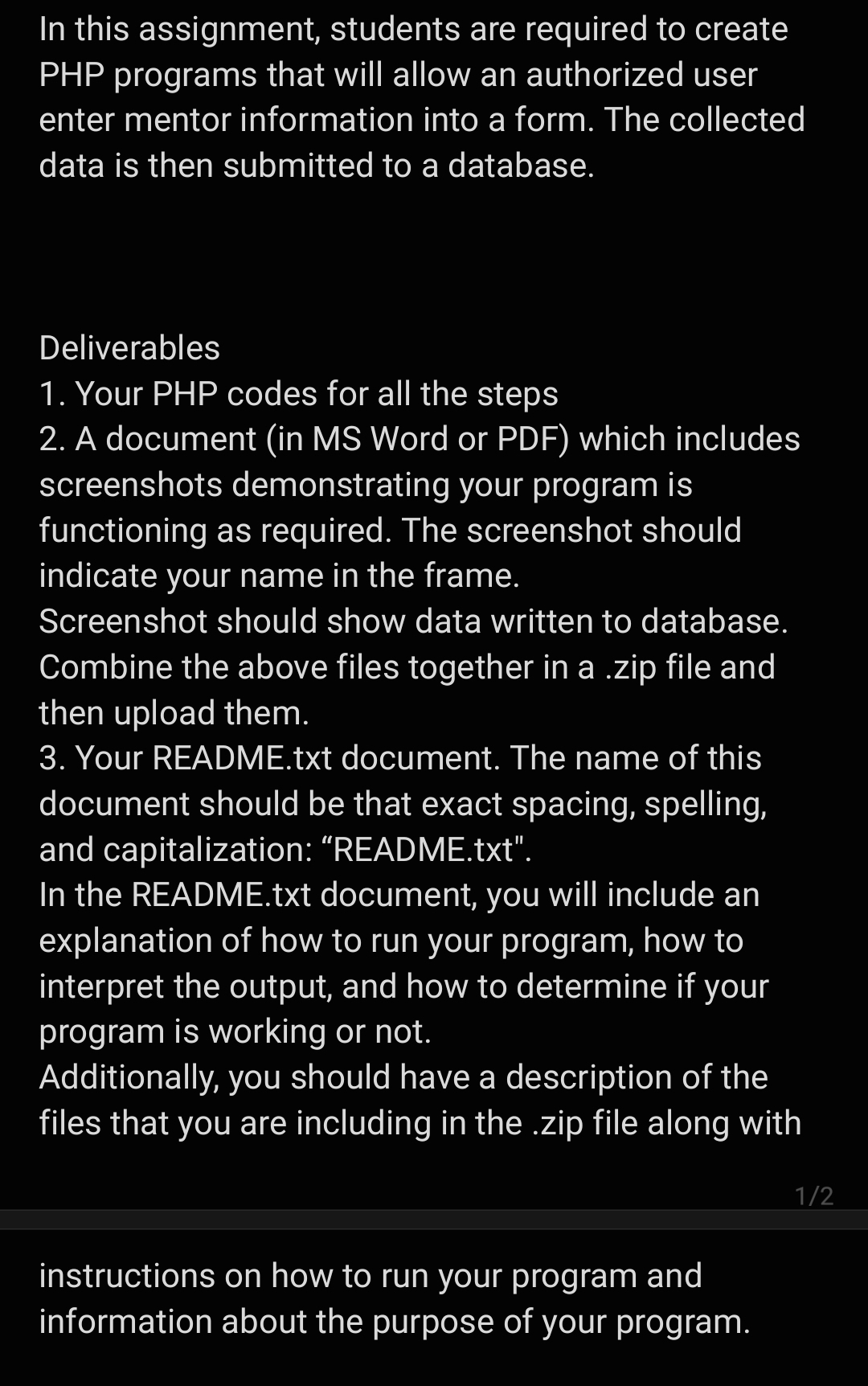
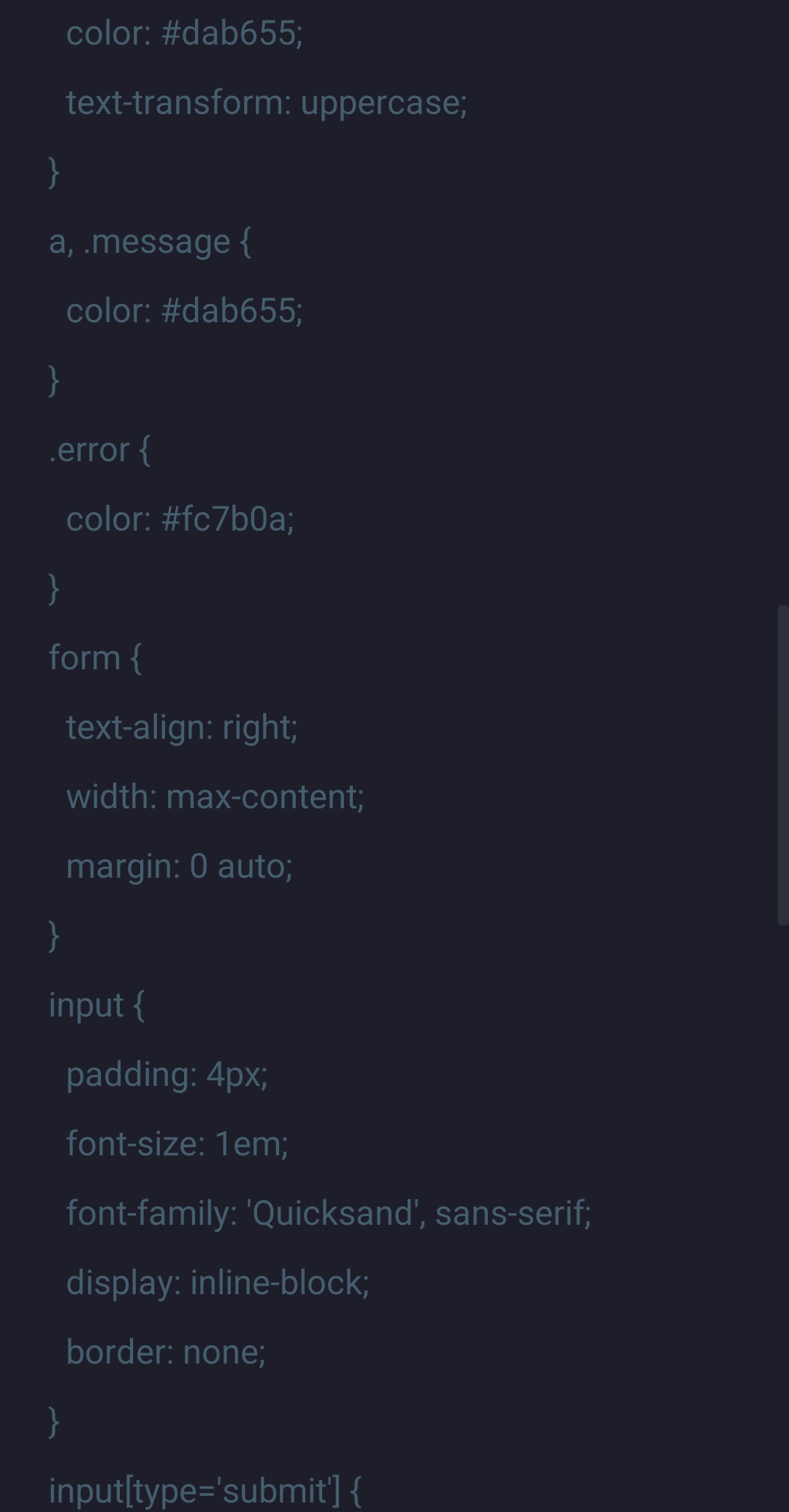
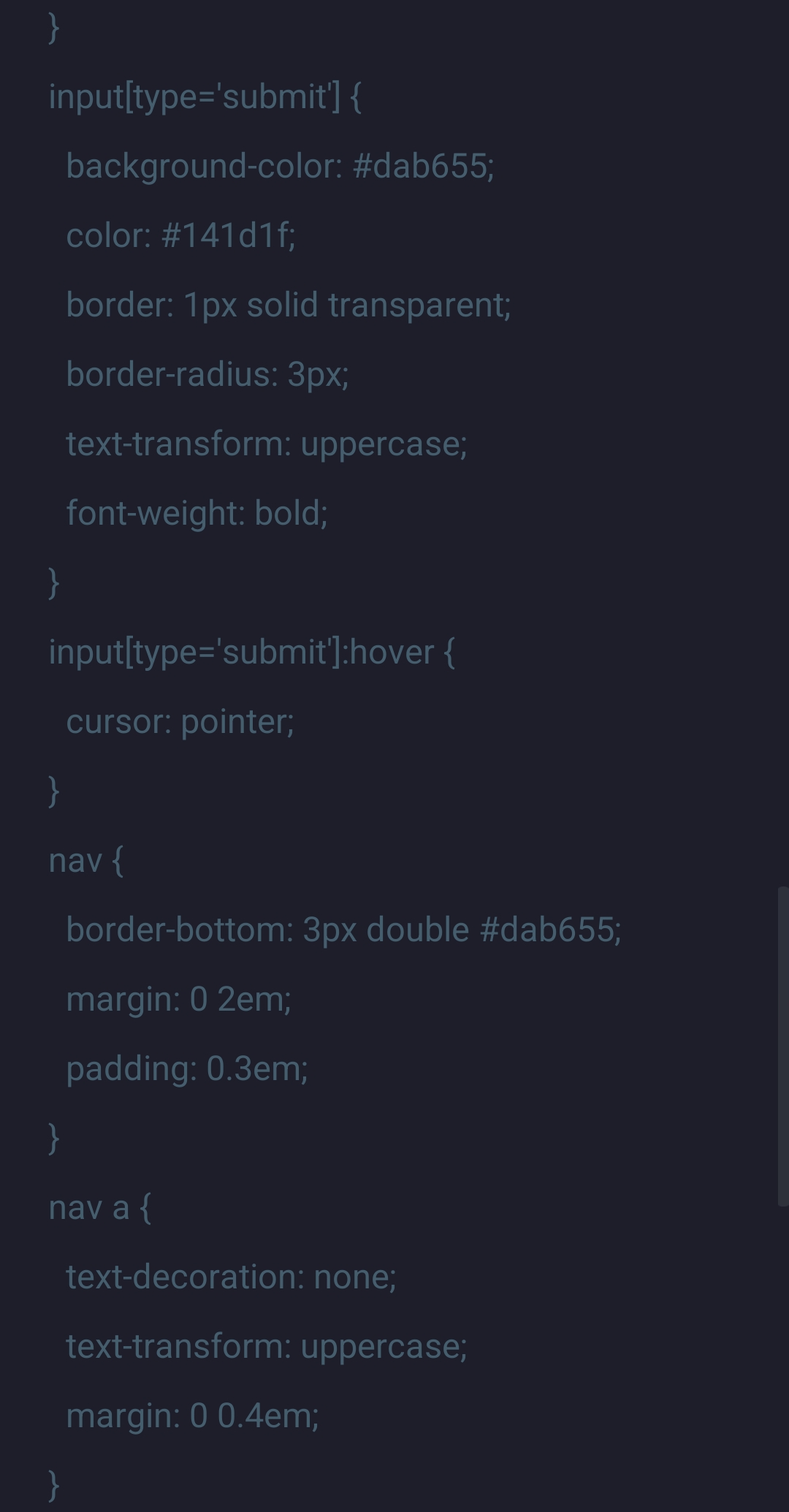
INSTRUCTIONS In this assignment, students are required to create PHP programs that will allow an authorized user enter mentor information into a form. The collected data is then submitted to a database. Step 1 (15pts) 1) Create php program, named login.php, using skeleton code provided. This code is expect to function as follows: a) to provide a user a form that has the contents of Table 1. b) to use POST method for submitting the form. c) to use header() function to redirect authenticated users to a page, mentors.php, d) It is possible that a user is already logged in. Write code to check this, using a boolean variable $logged_in. If the user is already logged in, your code should redirect the user to a page, mentors.php. (See page 346). Skeleton code has been provided, login.php, which you are to modify. e) Create a simple php code, logout.php. When executed code should simply say "You are logged out." Table 1 Label for mentor Username Password CSIS 311 Server Site Scripting Assignment 4 Step 2 (10pts) 2) Your code will use sessions to remember if your site user is already logged in. The skeleton code msessions.php has been provided. Modify this code so that either of the following two users can log in and use the mentor system and update the Mentors table in the database using the specified credentials. a) User 1 (Username: amaka; Password: amakapassword b) User 2 (Username: peter; Password: peterpassword Component to accept Input Step 3 (25pts) 3) From the previous steps, if a user is successfully authenticated, the user will be redirected to mentors.php. Here, you will create code, mentors.php and it is expected to function as follows: a) When a user is redirected to mentors.php, include html code to say "Welcome Amaka" or "Welcome Peter" (see page 33). Use input type, text Use input type, password b) It will contain a form for data input as indicated in table 2. c) Form will use POST method. email telephone Address Highest Degree Graduation Year Mentoring Interests d) Use htmlspecialchars() function in appropriate parts of your code to reduce the risk of cross site scripting attacks. The skeleton code, mentors-skeleton-code.php, has been provided for use, here. Table 2 Label for mentor first name last name Dr. Adaeze Nwaigwe Component to accept Input Appropriate form component Appropriate form component Appropriate form component Appropriate form component Text Area Radio buttons (Bachelors, MSc., PhD.) Dropdown list (2012-2022) Computer Science Cybersecurity Computer Information Technology Computer Information Systems Save button - Will cause entries to be stored in database table Reset button - Will cause entries to be cleared
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


