Question: Please help me with this question! 6. Certificates and PKI. (10 points) In this question, we assume that all public keys are known to everyone.
Please help me with this question!
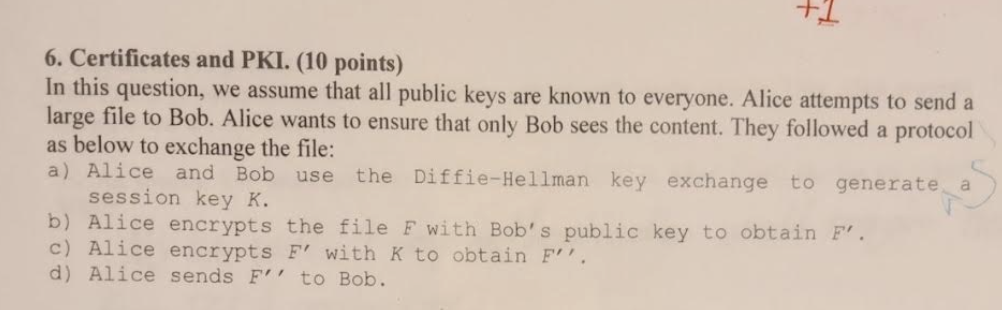
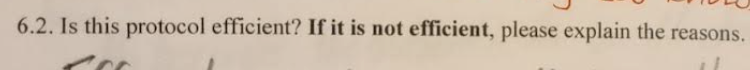
6. Certificates and PKI. (10 points) In this question, we assume that all public keys are known to everyone. Alice attempts to send a large file to Bob. Alice wants to ensure that only Bob sees the content. They followed a protocol as below to exchange the file: a) Alice and Bob use the Diffie-Hellman key exchange to generate a session key K. b) Alice encrypts the file F with Bob's public key to obtain F. c) Alice encrypts F with K to obtain F. d) Alice sends F to Bob. 6.2. Is this protocol efficient? If it is not efficient, please explain the reasons
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


