Question: Please if you are not sure from your answer 100% do not answer the question. Thanks in advance. During a security assessment, activities were divided
Please if you are not sure from your answer 100% do not answer the question. Thanks in advance.
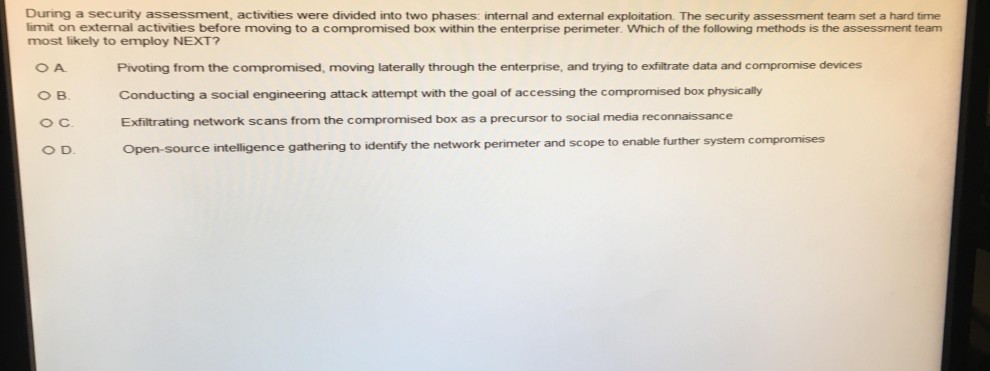
During a security assessment, activities were divided into two phases: internal and external exploitation. The security assessment team set a hard time limit on external activities before moving to a compromised box within the enterprise perimeter. Which of the following methods is the assessment team most likely to employ NEXT? B. o C. O D. Pivoting from the compromised, moving laterally through the enterprise, and trying to exfiltrate data and compromise devices Conducting a social engineering attack attempt with the goal of accessing the compromised box physically Exfiltrating network scans from the compromised box as a precursor to social media reconnaissance Open-source intelligence gathering to identify the network perimeter and scope t o enable further system compromises
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


