Question: Please use computer typing And Do 3,4 Q3. Identify four defense approaches that are used as Worm Countermeasures? Q4. Briefly explain based on your understanding
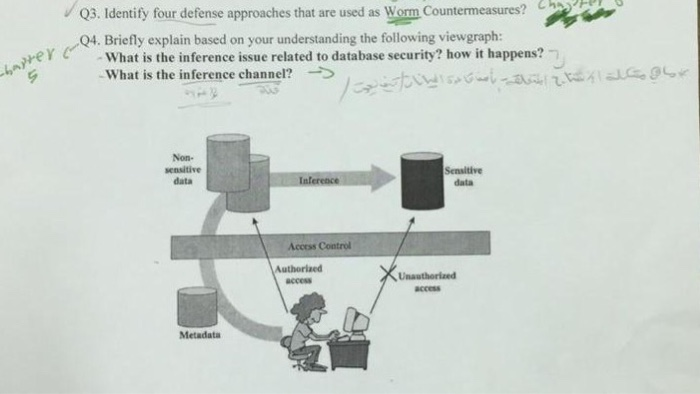
Q3. Identify four defense approaches that are used as Worm Countermeasures? Q4. Briefly explain based on your understanding the following viewgraph: ey cWhat is the inference issue related to database security? how it happens? What is the inference channel? Non- sensitive data Sensitive data Access Control access access Metadata
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


