Problem: You are an administrator of a computer system and are always required to create usernames...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
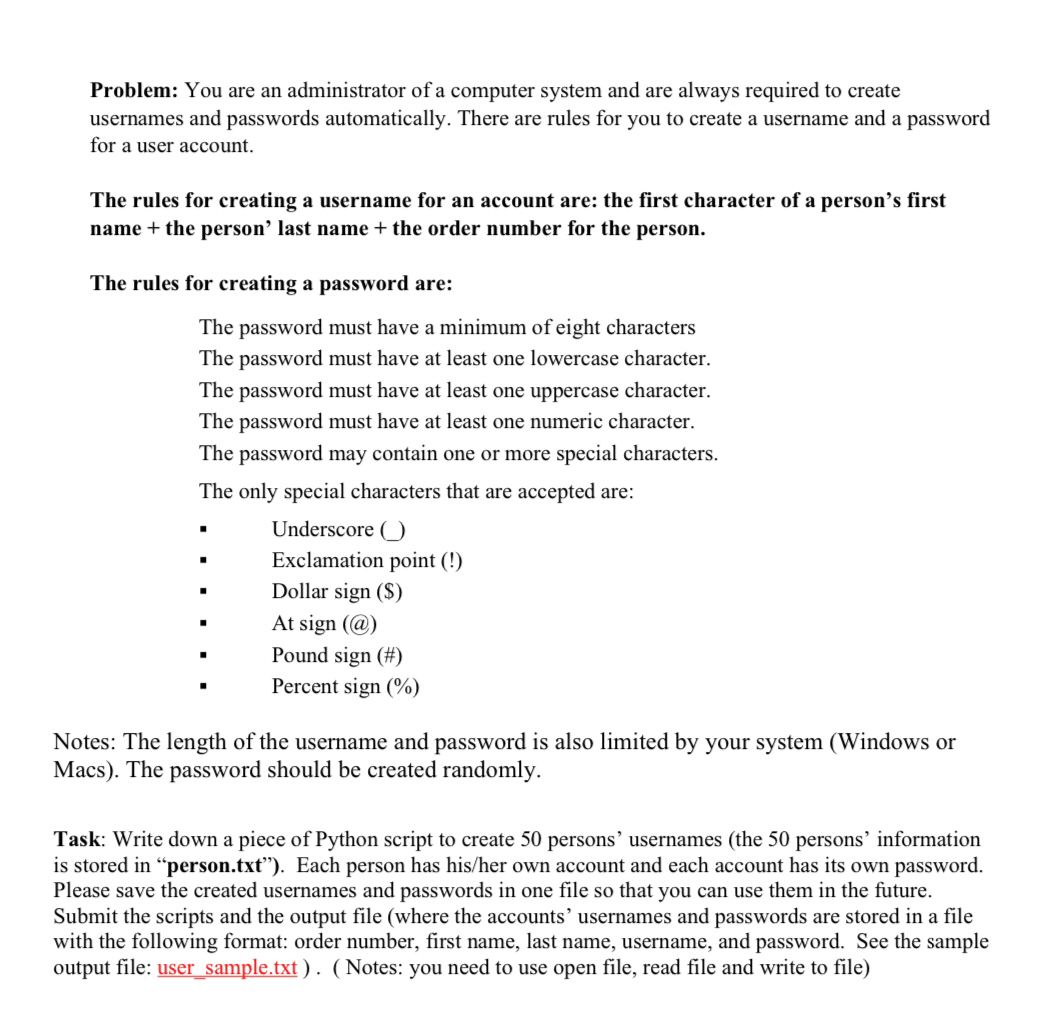
Problem: You are an administrator of a computer system and are always required to create usernames and passwords automatically. There are rules for you to create a username and a password for a user account. The rules for creating a username for an account are: the first character of a person's first name + the person' last name + the order number for the person. The rules for creating a password are: The password must have a minimum of eight characters The password must have at least one lowercase character. The password must have at least one uppercase character. The password must have at least one numeric character. The password may contain one or more special characters. The only special characters that are accepted are: " Underscore () Exclamation point (!) Dollar sign ($) At sign (@) Pound sign (#) Percent sign (%) Notes: The length of the username and password is also limited by your system (Windows or Macs). The password should be created randomly. Task: Write down a piece of Python script to create 50 persons' usernames (the 50 persons' information is stored in "person.txt"). Each person has his/her own account and each account has its own password. Please save the created usernames and passwords in one file so that you can use them in the future. Submit the scripts and the output file (where the accounts' usernames and passwords are stored in a file with the following format: order number, first name, last name, username, and password. See the sample output file: user_sample.txt). (Notes: you need to use open file, read file and write to file) Problem: You are an administrator of a computer system and are always required to create usernames and passwords automatically. There are rules for you to create a username and a password for a user account. The rules for creating a username for an account are: the first character of a person's first name + the person' last name + the order number for the person. The rules for creating a password are: The password must have a minimum of eight characters The password must have at least one lowercase character. The password must have at least one uppercase character. The password must have at least one numeric character. The password may contain one or more special characters. The only special characters that are accepted are: " Underscore () Exclamation point (!) Dollar sign ($) At sign (@) Pound sign (#) Percent sign (%) Notes: The length of the username and password is also limited by your system (Windows or Macs). The password should be created randomly. Task: Write down a piece of Python script to create 50 persons' usernames (the 50 persons' information is stored in "person.txt"). Each person has his/her own account and each account has its own password. Please save the created usernames and passwords in one file so that you can use them in the future. Submit the scripts and the output file (where the accounts' usernames and passwords are stored in a file with the following format: order number, first name, last name, username, and password. See the sample output file: user_sample.txt). (Notes: you need to use open file, read file and write to file)
Expert Answer:
Answer rating: 100% (QA)
To create 50 persons usernames and passwords in Python and save them to a file we can use the following steps Open the persontxt file and read the contents into a list Create a new list to store the g... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
The figure shows four current-carrying wires that are perpendicular to the page, where I = 1.8 A, I = 2.2 A, 13 = 3.6 A, and 14 = 4.2 A. Four Amprian loops are also shown. Find the current through...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Suppose \(x\) is a linked-list Node. What is the effect of the following code fragment? \[x \cdot \text { next }=x \cdot \text { next } . \text { next; }\]
-
A child on a sled come flying over the crest of a small hill, as shown in Fig. 5-31. His sled does not leave the ground (he does not achieve air), but he feels the normal force between his chest and...
-
Production period, if Jennifer has 2 5 pounds of ripened bananas to work with, what quantities of each product should she make in order to maximize her profitability?
-
Use the implicit finite difference method to solve the heat conduction problem on the unit square: \[\begin{aligned}& \frac{\partial^{2} u}{\partial x^{2}}=\frac{\partial u}{\partial t} \\& u(x, 0)=x...
-
Consider a rod of diameter D, thermal conductivity k, and length 2L that is perfectly insulated over one portion of its length, - L
-
Find the x- and y-intercepts for the function. Enter your answers as points, (a, b). The z-intercept is +2 f(x) = 2+4 The y-intercept is B B. Show your work and explain, in your own words, how you...
-
Shown on the following page are responsibility income statements for Butterfield, Inc., for the month of March. Instructions a. The company plans to initiate an advertising campaign for one of the...
-
An analog signal is bandlimited to 4 kHz and sampled at Nyquist rate. The samples are quantised into 4 levels. Find the information rate of the source, if (a) the probability of occurrence of the...
-
Identify the kinds of objections to discovery requests that can be raised.
-
Describe the nature and purpose of financial statements/affidavits.
-
Identify at least five methods of enforcing child support obligations.
-
Identify a minimum of five ways of concealing assets and how they might be detected.
-
Explain how depreciation generates actual cash flows for a firm.
-
Match the following accomplishments to the correctemperor. Terracotta Warriors. Unified China. Created unifiedweights and measures. Prevented a rebellionby Lao Ai. Ordered the burning ofConfucian...
-
Name some of the various types of financial intermediaries described in the chapter and indicate the primary reason(s) each was created.
-
Discuss the relationship between the balance in the accounts payable general ledger control account and what is found in the account payable subsidiary ledger.
-
Examine the context and intermediate (Level 1) data flow diagrams in the diagram for Problem 3 and indicate what is incorrect aboutthem. DATA FLOW DIAGRAMS Context-Level Diagram Customer Order...
-
Is a data flow diagram an effective documentation technique for identifying who or what performs a particular Explain?
-
Differentiate between tax compliance and tax planning.
-
Differentiate between an open transaction and a closed transaction.
-
What form(s) is (are) used to file an individuals income tax return?

Study smarter with the SolutionInn App


