Question: Prove that the grade-school multiplication algorithm (page 23), when applied to binary numbers, always gives the right answer. 1.7. How long does the recursive multiplication
Prove that the grade-school multiplication algorithm (page 23), when applied to binary numbers,
always gives the right answer.
1.7. How long does the recursive multiplication algorithm (page 24) take to multiply an n-bit number
by an m-bit number? Justify your answer.
1.8. Justify the correctness of the recursive division algorithm given in page 25, and show that it
takes time O(n2) on n-bit inputs.
1.9. Starting from the definition of x ≡ y mod N (namely, that N divides x−y), justify the substitution
rule
x ≡ x′ mod N, y ≡ y′ mod N ⇒ x + y ≡ x′ + y′ mod N,
and also the corresponding rule for multiplication.
1.10. Show that if a ≡ b (mod N ) and if M divides N then a ≡ b (mod M ).
1.11. Is 41536 − 94824 divisible by 35?
1.12. What is 222006
(mod 3)?
1.13. Is the difference of 530,000 and 6123,456 a multiple of 31? 1.14. Suppose you want to compute the nth Fibonacci number Fn, modulo an integer p. Can you find an efficient way to do this? (Hint: Recall Exercise 0.4.)
The telephone network of today and the Resource Reservation Protocol (RSVP) and associated services proposed for the future Internet provide open loop control. Briefly explain the functions of signalling, admission control and policing in these types of networks. [3 marks each] (b) Traffic sources are described as elastic or inelastic. Outline how an inelastic traffic source can be characterised and how this relates to the type of network resource guarantees it may need. [5 marks] 2 CST.2006.7.3 3 Security (a) What is meant by Mandatory Access Control? Give an example. [5 marks] (b) How might you use mandatory access control to protect the safety-critical systems in a car (engine control unit, ABS, stability control, etc.) from userprogrammable systems (telephone, entertainment, navigation, etc.)? [5 marks] (c) What problems would you anticipate in keeping the implementation clean as these systems evolve? [5 marks] (d) What architecture might you therefore propose a car maker adopt for its nextgeneration networking? [5 marks] 4 Advanced Graphics (a) Describe, in outline, each of the implicit surface, NURBS surface, and constructive solid geometry methods for defining three-dimensional shapes. [4 marks each] (b) Compare and contrast the three methods. [8 marks] 3 (TURN OVER) CST.2006.7.4 5 Computer Systems Modelling (a) Describe the congruential methods for generating pseudo-random numbers from a Uniform (0, 1) distribution. [3 marks] (b) Let U be a Uniform (0, 1) random variable. Show that for any continuous distribution function, F(x), the random variable, X, defined by X = F ?1 (U) has the probability distribution function F(x). [3 marks] (c) Apply the method of part (b) to generate random variables with the following distributions. In each case, specify the distribution function F(x) that you use. (i) Uniform distribution on the interval (a, b), for a 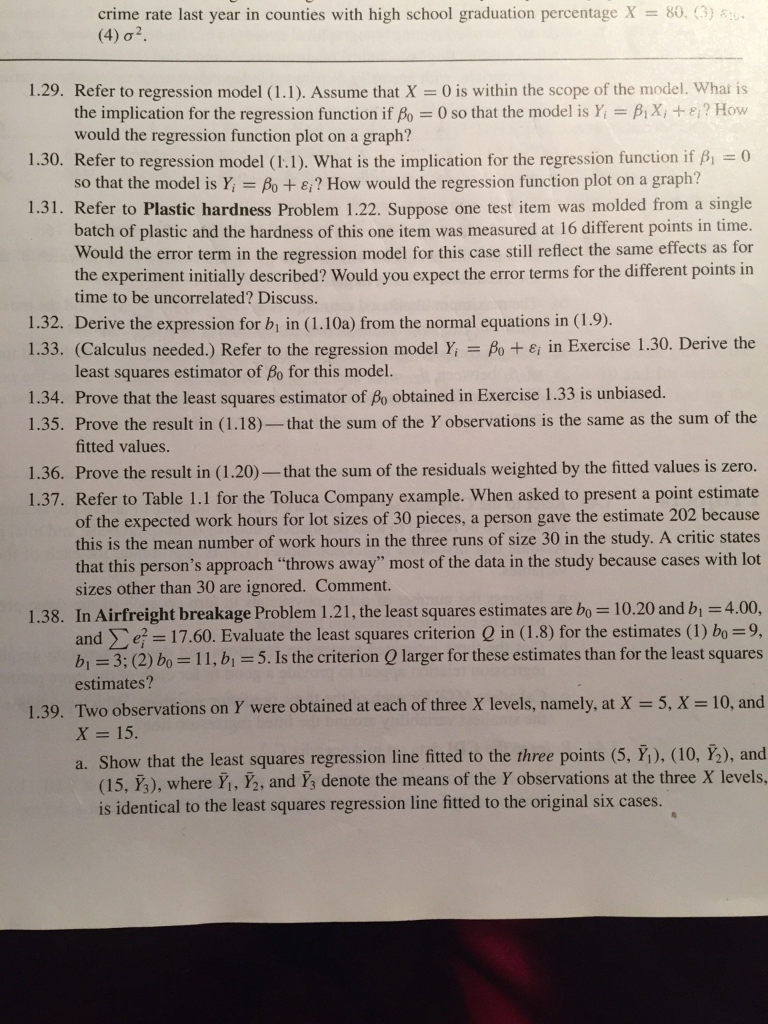
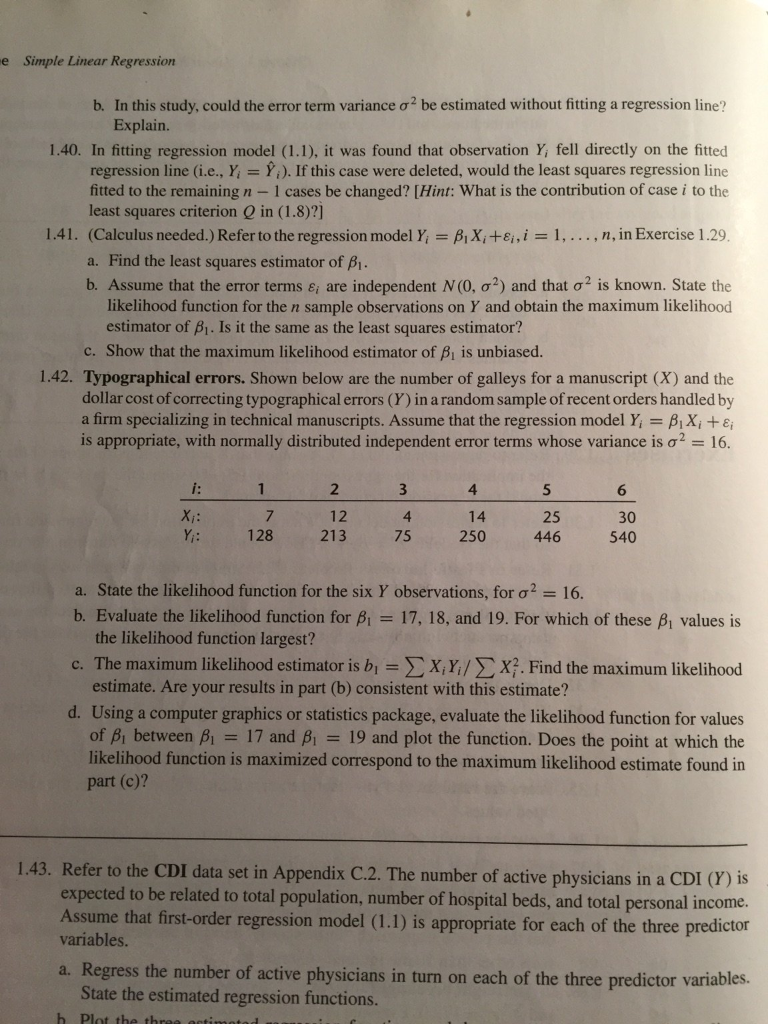
crime rate last year in counties with high school graduation percentage X= 80, (3) 510- (4) 0. 1.29. Refer to regression model (1.1). Assume that X = 0 is within the scope of the model. What is the implication for the regression function if fo = 0 so that the model is Y = BX, + &? How would the regression function plot on a graph? 1.30. Refer to regression model (1.1). What is the implication for the regression function if B = 0 so that the model is Y = Bo + 8? How would the regression function plot on a graph? 1.31. Refer to Plastic hardness Problem 1.22. Suppose one test item was molded from a single batch of plastic and the hardness of this one item was measured at 16 different points in time. Would the error term in the regression model for this case still reflect the same effects as for the experiment initially described? Would you expect the error terms for the different points in time to be uncorrelated? Discuss. 1.32. Derive the expression for b in (1.10a) from the normal equations in (1.9). 1.33. (Calculus needed.) Refer to the regression model Y = Bo + 8 in Exercise 1.30. Derive the least squares estimator of Bo for this model. 1.34. Prove that the least squares estimator of Bo obtained in Exercise 1.33 is unbiased. 1.35. Prove the result in (1.18)-that the sum of the Y observations is the same as the sum of the fitted values. 1.36. Prove the result in (1.20)-that the sum of the residuals weighted by the fitted values is zero. 1.37. Refer to Table 1.1 for the Toluca Company example. When asked to present a point estimate of the expected work hours for lot sizes of 30 pieces, a person gave the estimate 202 because this is the mean number of work hours in the three runs of size 30 in the study. A critic states that this person's approach "throws away" most of the data in the study because cases with lot sizes other than 30 are ignored. Comment. 1.38. In Airfreight breakage Problem 1.21, the least squares estimates are bo = 10.20 and b = 4.00, ande = 17.60. Evaluate the least squares criterion Q in (1.8) for the estimates (1) bo = 9, b = 3; (2) bo = 11, b = 5. Is the criterion Q larger for these estimates than for the least squares estimates? 1.39. Two observations on Y were obtained at each of three X levels, namely, at X = 5, X = 10, and X = 15. a. Show that the least squares regression line fitted to the three points (5, ), (10, ), and (15, Y3), where , 2, and Y3 denote the means of the Y observations at the three X levels, is identical to the least squares regression line fitted to the original six cases.
Step by Step Solution
There are 3 Steps involved in it
Sure Ill help you break down and answer some of the questions you posted Lets start with a few of them 17 Recursive Multiplication Algorithm Time Complexity To determine how long the recursive multipl... View full answer

Get step-by-step solutions from verified subject matter experts


