Question: Q 5 ( a ) What are the 3 ' V ' s of Big Data? ( b ) Give one example use case of
Q
a What are the Vs of Big Data?
b Give one example use case of Big Data.
c What are the differences between MapReduce and Hadoop?
d Briefly explain the following three best practices for data security:
i Principle of least privilege
ii Firewall
iiiDisable the use of LOCAL INFILE
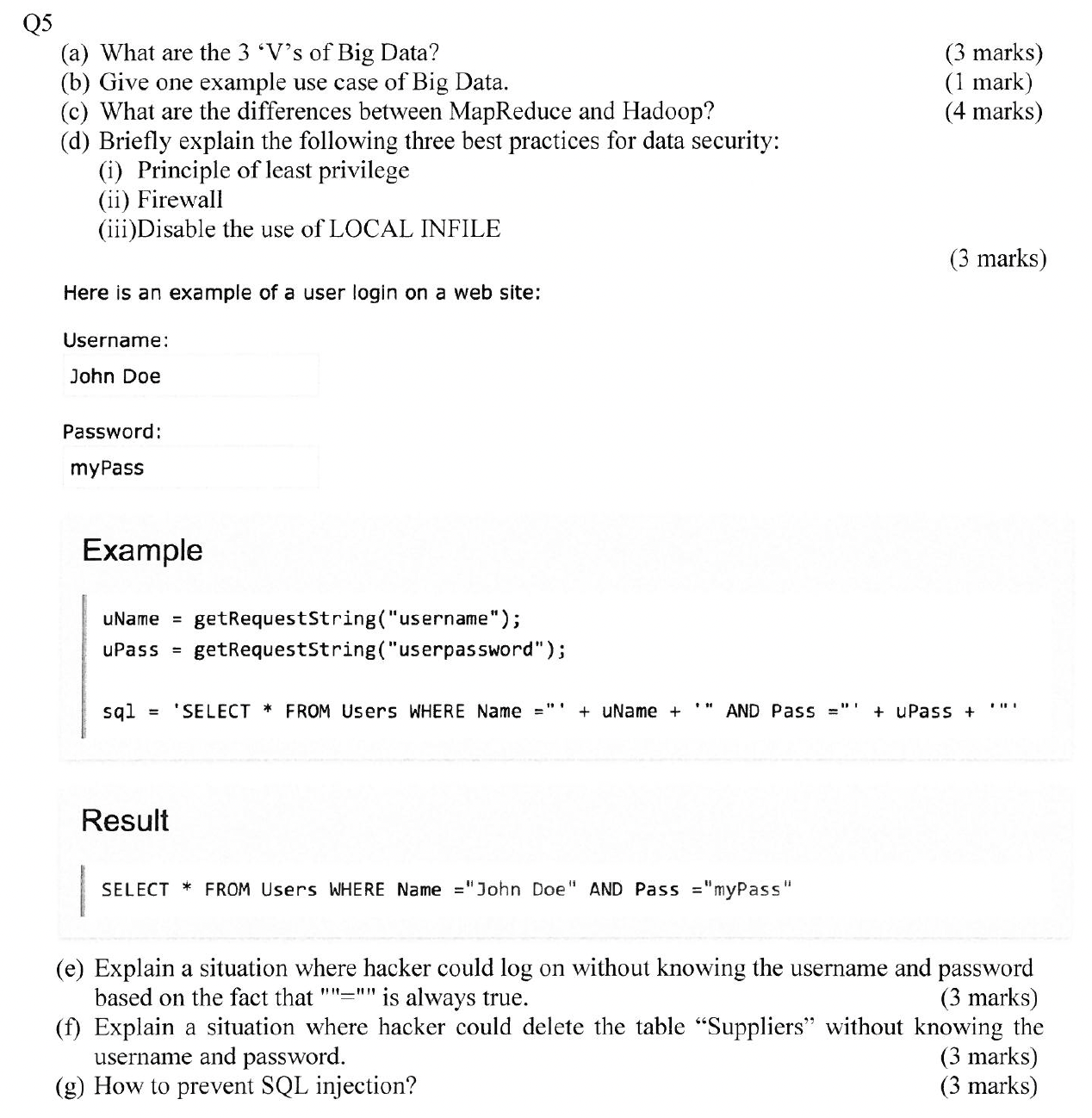
Here is an example of a user login on a web site:
Username:
Password:
Example
Result
SELECT FROM Users WHERE Name "John Doe" AND Pass "myPass"
e Explain a situation where hacker could log on without knowing the username and password
based on the fact that is always true.
f Explain a situation where hacker could delete the table "Suppliers" without knowing the
username and password.
marks
g How to prevent SQL injection?
marks
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


