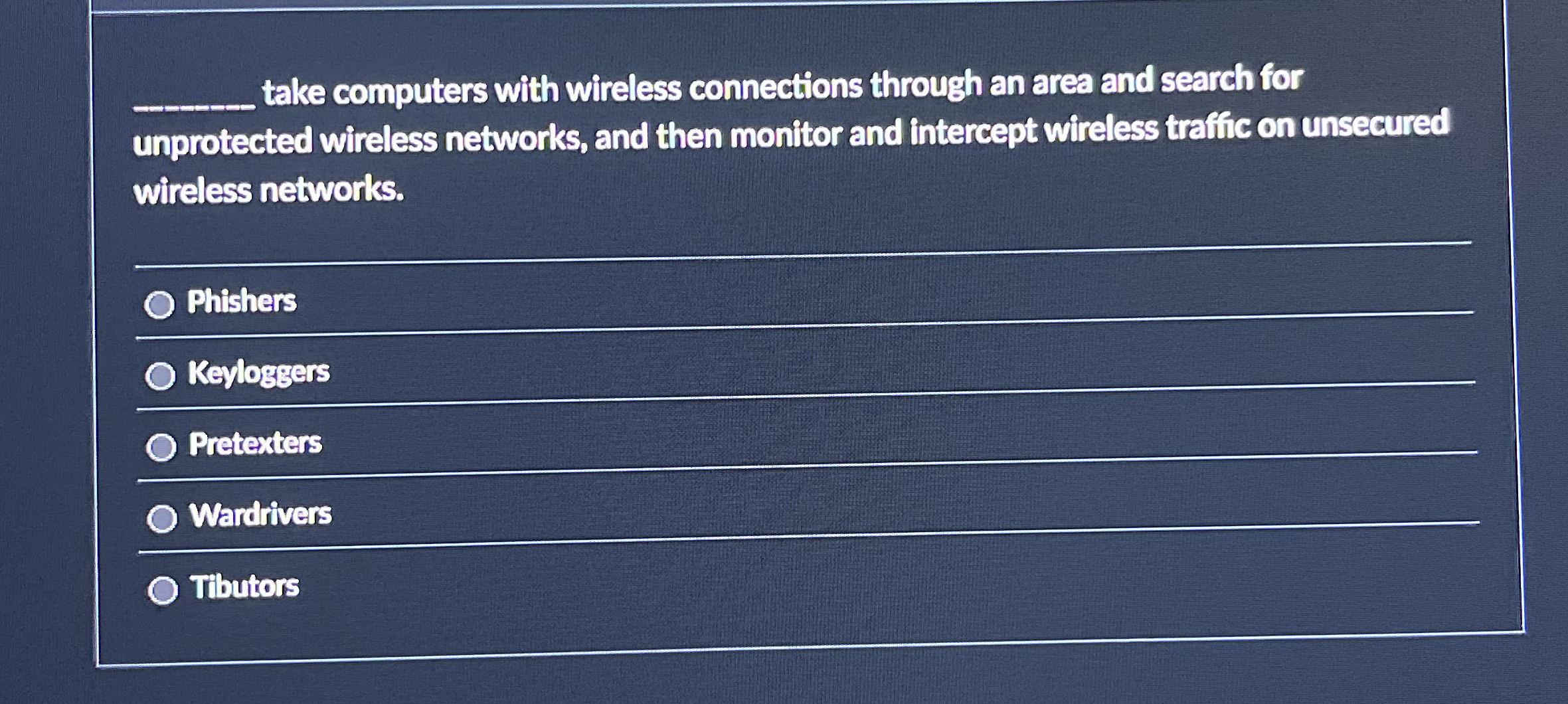
Question: q , take computers with wireless connections through an area and search for unprotected wireless networks, and then monitor and intercept wireless traffic on unsecured
take computers with wireless connections through an area and search for unprotected wireless networks, and then monitor and intercept wireless traffic on unsecured wireless networks.
Phishers
Keyloggers
Pretexters
Wardrivers
Tibutors
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


