Question: Q1. List five major terms (basic Security terminology) of EC security Q2. Describe the vulnerable design of the Internet. Q3. Define Hacker, cracker, and social
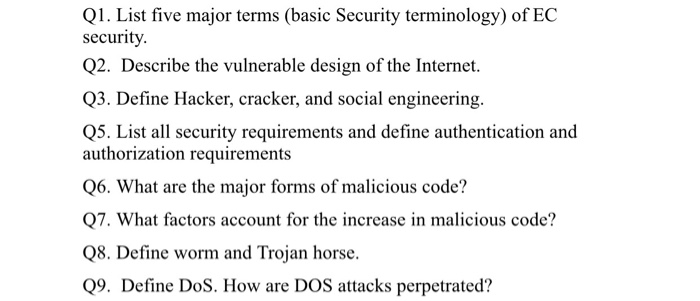
Q1. List five major terms (basic Security terminology) of EC security Q2. Describe the vulnerable design of the Internet. Q3. Define Hacker, cracker, and social engineering Q5. List all security requirements and define authentication and authorization requirements Q6. What are the major forms of malicious code? Q7. What factors account for the increase in malicious code? Q8. Define worm and Trojan horse. Q9. Define DoS. How are DOS attacks perpetrated
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


