Question: Q.2.1 Q.2.2 Q.2.3 Q.2.4 Using suitable examples, differentiate between the Domain Name System (DNS) (8) and Layer 2 network attacks. Your answer must give
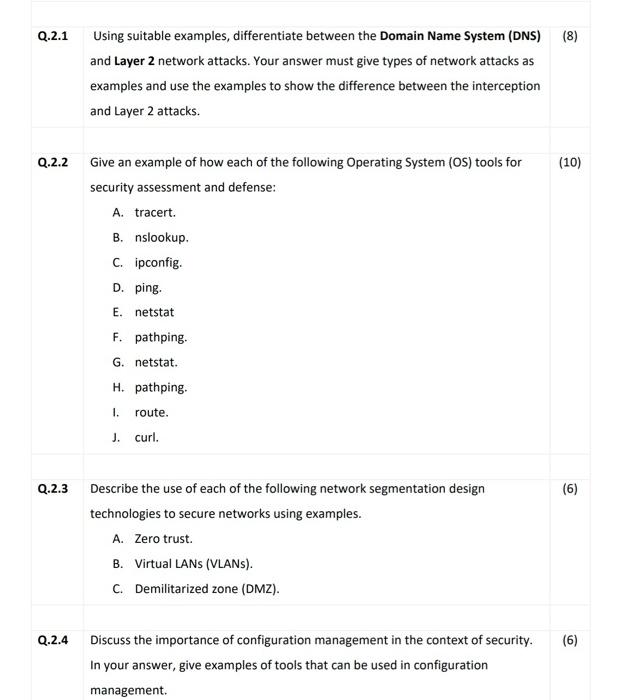
Q.2.1 Q.2.2 Q.2.3 Q.2.4 Using suitable examples, differentiate between the Domain Name System (DNS) (8) and Layer 2 network attacks. Your answer must give types of network attacks as examples and use the examples to show the difference between the interception and Layer 2 attacks. Give an example of how each of the following Operating System (OS) tools for security assessment and defense: A. tracert. B. nslookup. C. ipconfig. D. ping. E. netstat F. pathping. G. netstat. H. pathping. 1. J. curl. route. Describe the use of each of the following network segmentation design technologies to secure networks using examples. A. Zero trust. B. Virtual LANS (VLANS). C. Demilitarized zone (DMZ). (10) (6) Discuss the importance of configuration management in the context of security. (6) In your answer, give examples of tools that can be used in configuration management.
Step by Step Solution
There are 3 Steps involved in it
Q21 Differentiating between DNS and Layer 2 Network Attacks DNS Attacks DNS SpoofingCache Poisoning Example An attacker manipulates DNS responses to redirect users to malicious websites This could inv... View full answer

Get step-by-step solutions from verified subject matter experts


