Q4 of 14 Which among the following is not a privacy harm? Behavioral profiling An employee's...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
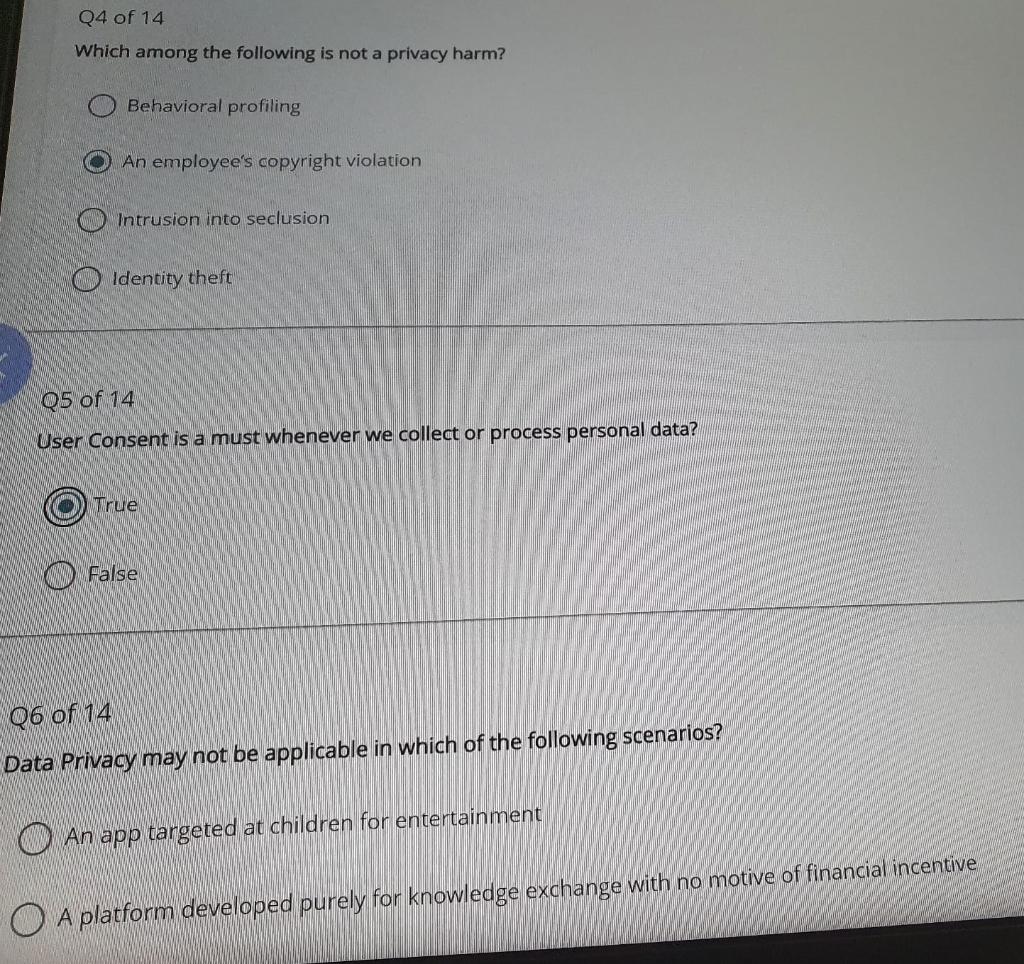
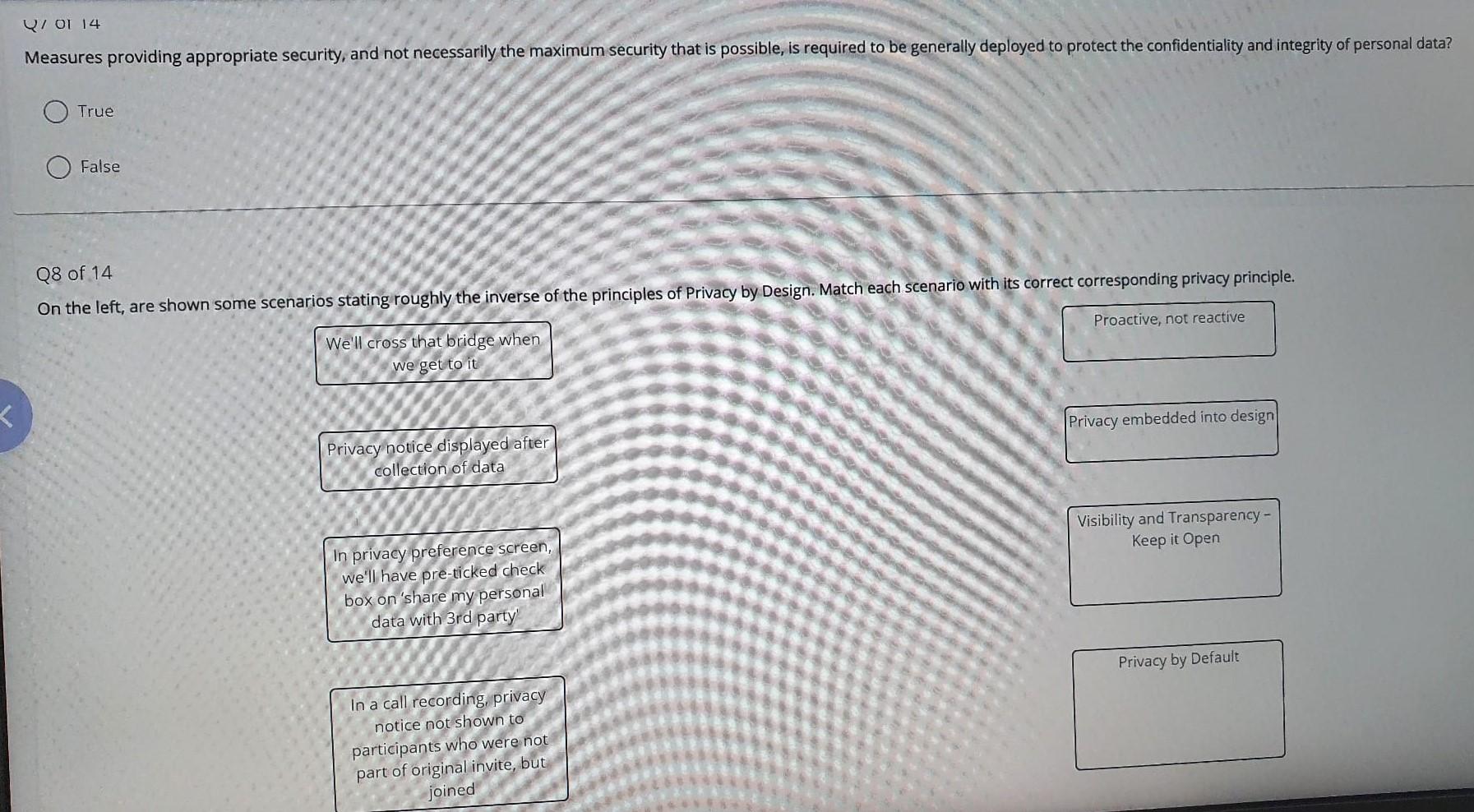
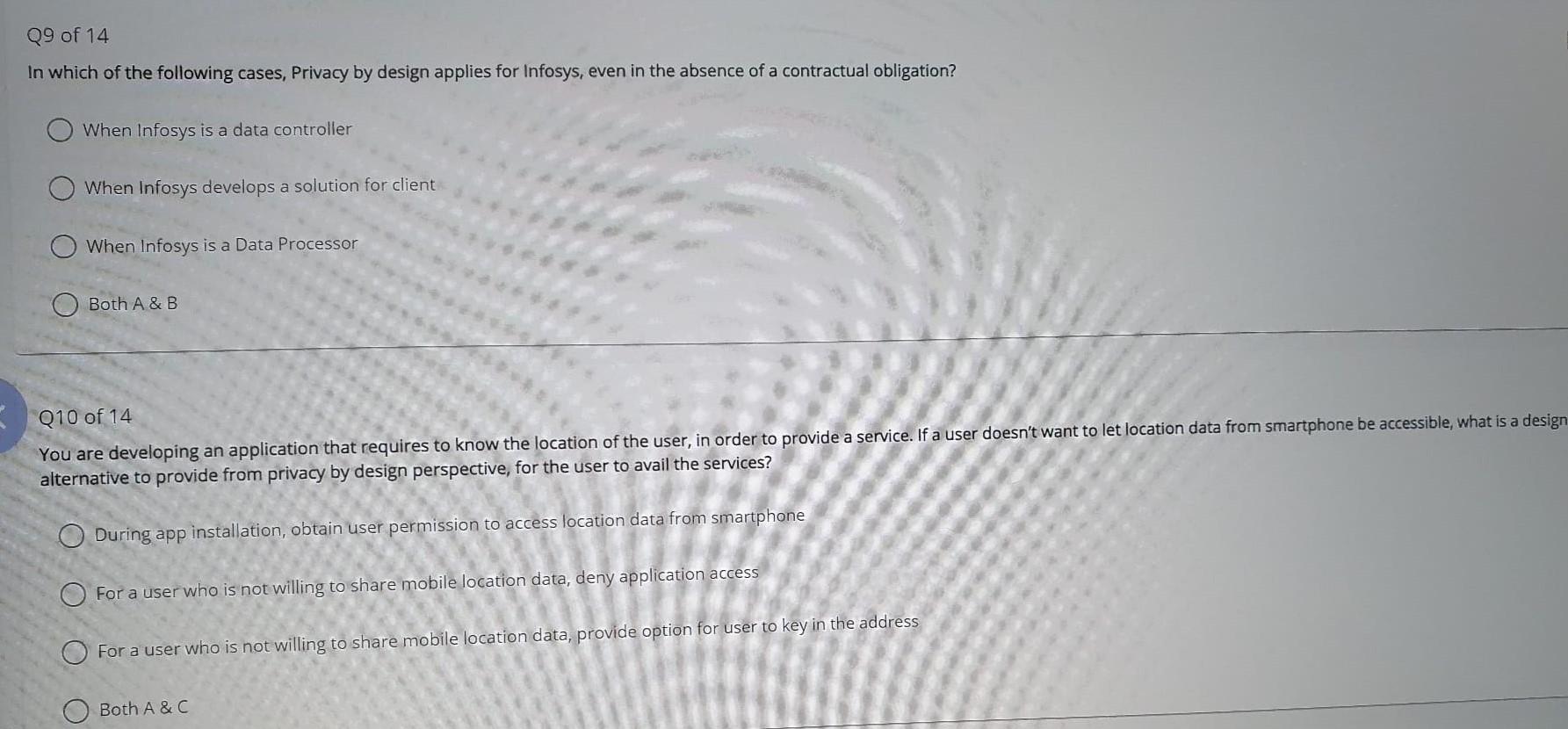
Q4 of 14 Which among the following is not a privacy harm? Behavioral profiling An employee's copyright violation Intrusion into seclusion Identity theft Q5 of 14 User Consent is a must whenever we collect or process personal data? True False Q6 of 14 Data Privacy may not be applicable in which of the following scenarios? An app targeted at children for entertainment A platform developed purely for knowledge exchange with no motive of financial incentive Q701 14 Measures providing appropriate security, and not necessarily the maximum security that is possible, is required to be generally deployed to protect the confidentiality and integrity of personal data? L True False Q8 of 14 On the left, are shown some scenarios stating roughly the inverse of the principles of Privacy by Design. Match each scenario with its correct corresponding privacy principle. Proactive, not reactive We'll cross that bridge when we get to it Privacy notice displayed after collection of data In privacy preference screen, we'll have pre-ticked check box on 'share my personal data with 3rd party' In a call recording, privacy notice not shown to participants who were not part of original invite, but joined Privacy embedded into design Visibility and Transparency - Keep it Open Privacy by Default Q9 of 14 In which of the following cases, Privacy by design applies for Infosys, even in the absence of a contractual obligation? When Infosys is a data controller When Infosys develops a solution for client When Infosys is a Data Processor Both A & B Q10 of 14 You are developing an application that requires to know the location of the user, in order to provide a service. If a user doesn't want to let location data from smartphone be accessible, what is a design alternative to provide from privacy by design perspective, for the user to avail the services? During app installation, obtain user permission to access location data from smartphone For a user who is not willing to share mobile location data, deny application access For a user who is not willing to share mobile location data, provide option for user to key in the address Both A & C Q4 of 14 Which among the following is not a privacy harm? Behavioral profiling An employee's copyright violation Intrusion into seclusion Identity theft Q5 of 14 User Consent is a must whenever we collect or process personal data? True False Q6 of 14 Data Privacy may not be applicable in which of the following scenarios? An app targeted at children for entertainment A platform developed purely for knowledge exchange with no motive of financial incentive Q701 14 Measures providing appropriate security, and not necessarily the maximum security that is possible, is required to be generally deployed to protect the confidentiality and integrity of personal data? L True False Q8 of 14 On the left, are shown some scenarios stating roughly the inverse of the principles of Privacy by Design. Match each scenario with its correct corresponding privacy principle. Proactive, not reactive We'll cross that bridge when we get to it Privacy notice displayed after collection of data In privacy preference screen, we'll have pre-ticked check box on 'share my personal data with 3rd party' In a call recording, privacy notice not shown to participants who were not part of original invite, but joined Privacy embedded into design Visibility and Transparency - Keep it Open Privacy by Default Q9 of 14 In which of the following cases, Privacy by design applies for Infosys, even in the absence of a contractual obligation? When Infosys is a data controller When Infosys develops a solution for client When Infosys is a Data Processor Both A & B Q10 of 14 You are developing an application that requires to know the location of the user, in order to provide a service. If a user doesn't want to let location data from smartphone be accessible, what is a design alternative to provide from privacy by design perspective, for the user to avail the services? During app installation, obtain user permission to access location data from smartphone For a user who is not willing to share mobile location data, deny application access For a user who is not willing to share mobile location data, provide option for user to key in the address Both A & C
Expert Answer:
Answer rating: 100% (QA)
QUESTION 4 ANSWER An employees copyright violation EXPLANATION An employees copyright violation is not a privacy harm because it does not involve any invasion of an individuals right to privacy Copyri... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Which of the following is not a true statement about the American opportunity credit (AOC) and lifetime learning credits (assume the 2016 rules apply for the qualified education expense deduction)?...
-
Which of the following is not a governmental structural policy that supply-side economists believe would promote long-term growth in an economy? a. A redistributive tax system. b. A promotion of...
-
Which of the following is not a strictly rational reason for someone to be interested in a commitment device? a. The device can eliminate the time-inconsistency problem. b. By making the decision to...
-
1. Construct a simple pendulum starting with 20 cm length. 2. Hang the pendulum as pictures in one of the two methods shown above. 3. Using the protractor, displace the pendulum 10 degrees from the...
-
The controller of Heritage Ceramics, Inc. wishes to prepare a cost of goods sold budget for June. The controller assembled the following information for constructing the cost of goods sold budget:...
-
What are local maximum and minimum values of a function?
-
Zeta Safety, Inc., began the year with $15,000 of common stock and $34,000 of retained earnings. On August 5, investors bought $19,000 of additional stock in the business. On October 22, the business...
-
Using T accounts for Cash, Accounts Payable, Purchases, Purchases Returns and Allowances, Purchases Discounts, and Freight-In, enter the following purchase transactions. Identify each transaction...
-
On January 1, 2017, Lincoln Corporation had 80,000 common shares outstanding, recorded on the books at $600,000. Retained Earnings were $1,000,000. During the year, the following transactions...
-
Refer back to the beginning of this chapter to the excerpt from a Los Angeles Times article about Reed Slatkin's fraud. The article insinuates that the FBI and IRS's raiding of Slatkin's office...
-
5. The population of Chicago was 2.7 million in 2010. However, the population is declining at a rate of 7% per year. Approximately how long will it take for the population to decrease to 1 million?
-
Did the Irish play a role in the American Revolution? What role did African Americans play in the American revolution? How did France help the colonies during the American revolution?
-
Howard Company reported a deferred tax liability of $15,000 and pretax financial statement income of $280,000 in its December 31, 2023, financial statements. Taxable income was $400,000 for 2024. At...
-
What innovative strategies can businesses employ to leverage emerging technologies as catalysts for sustainable growth and market expansion?
-
. A capillary tube has a diameter of 1.65 mm and a height of 97.1 mm. What is the volume of the capillary tube in meters?
-
5.What is the worst-case efficiency class of the following algorithm? * line no. 1 ALGORITHM Q5 (A[0..n-1][0..n-1]) 2 begin 3 for i=0 to n-2 do 4 5 for j=i+1 to n-1 do if(A[i][j] A[j] [i]) then...
-
a .) The local grocery store, Food Town, sells 14,000 gallons of milk per year. They are open 325 days per year. Due to needing to be refrigerated, they estimate that the milk has a holding cost of...
-
Show that if A is any m n matrix, then Im A = A and AIn = A.
-
Thomas Huber, the shop steward for the Machinists Union at G&H Products, Inc., was discharged for encouraging employees to engage in insubordination. He had told employees not to fill out a new...
-
What are the dual objectives of Section 8(b)(4) of the NLRA?
-
1. Did the Courts decision make it easier for older workers to sue for age discrimination on the job? 2. Disparate impact claims exist where an employers facially neutral employment practices, such...
-
What is the IQR? What does the IQR represent? The population parameters below describe the full-time equivalent number of students (FTES) each year at Lake Tahoe Community College from 19761977...
-
How many standard deviations away from the mean is the median? The population FTES for 20052006 through 20102011 was given in an updated report. The data are reported here. The population parameters...
-
A class of 20 students has a mean grade of 80 on a test. Nineteen of the students has a mean grade between 79 and 82, inclusive. a. What is the lowest possible grade of the other student? b. What is...

Study smarter with the SolutionInn App