Question: Q7: In this problem we will compare the security services that are provided by digital signatures (DS) and message authentication codes (MAC). We assume that
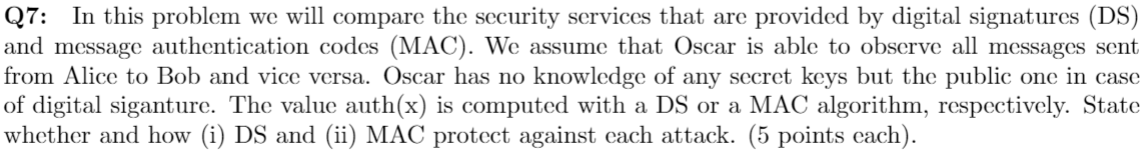
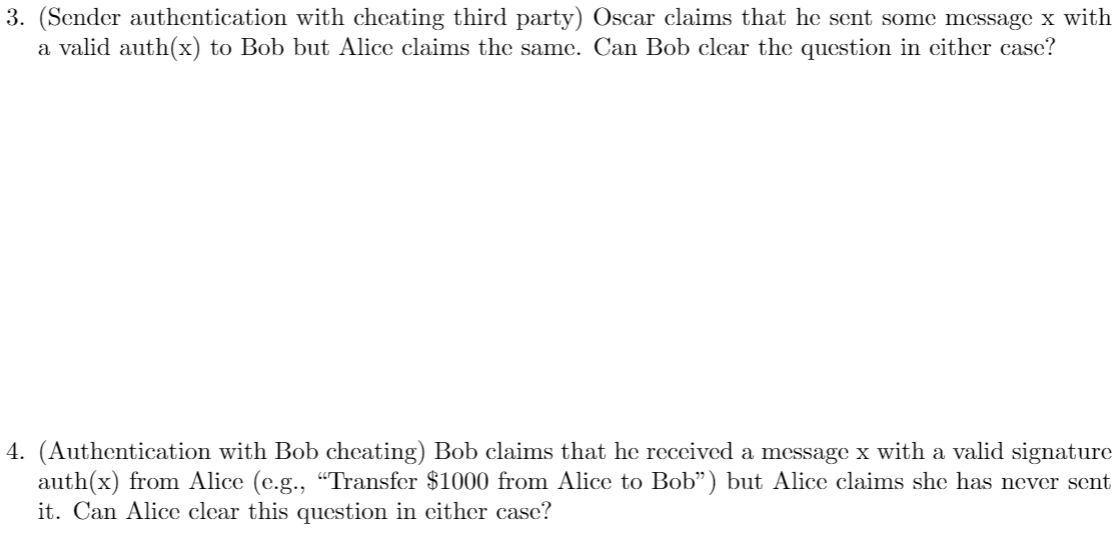
Q7: In this problem we will compare the security services that are provided by digital signatures (DS) and message authentication codes (MAC). We assume that Oscar is able to observe all messages sent from Alice to Bob and vice versa. Oscar has no knowledge of any secret keys but the public one in case of digital siganture. The value auth(x) is computed with a DS or a MAC algorithm, respectively. State whether and how (i) DS and (ii) MAC protect against cach attack. (5 points each). 3. (Sender authentication with cheating third party) Oscar claims that he sent some message x with a valid auth(x) to Bob but Alice claims the same. Can Bob clear the question in either case? 4. (Authentication with Bob cheating) Bob claims that he received a message x with a valid signature auth(x) from Alice (e.g., "Transfer $1000 from Alice to Bob) but Alice claims she has never sent it. Can Alice clear this question in either case
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


