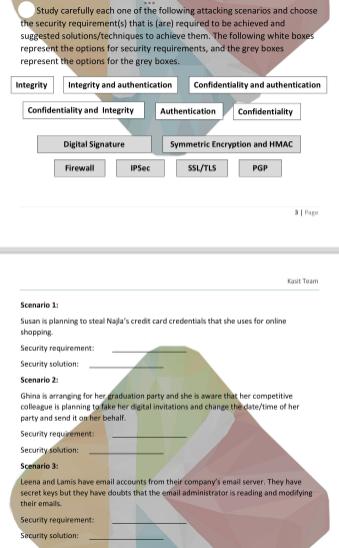
Study carefully each one of the following attacking scenarios and choose the security requirement(s) that is...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Study carefully each one of the following attacking scenarios and choose the security requirement(s) that is (are) required to be achieved and suggested solutions/techniques to achieve them. The following white boxes represent the options for security requirements, and the grey boxes represent the options for the grey boxes. Integrity Integrity and authentication Confidentiality and Integrity Digital Signature Firewall IPSec Confidentiality and authentication Authentication Confidentiality Security requirement: Security solution: Symmetric Encryption and HMAC SSL/TLS PGP Kait Team Scenario 1 Susan is planning to steal Najla's credit card credentials that she uses for online shopping. Security requirement: Security solution: Scenario 2: Ghina is arranging for her graduation party and she is aware that her competitive colleague is planning to take her digital invitations and change the date/time of her party and send it on her behalf. Security requirement Security solution: Scenario 3: Leena and Lamis have email accounts from their company's email server. They have secret keys but they have doubts that the email administrator is reading and modifying their emails Study carefully each one of the following attacking scenarios and choose the security requirement(s) that is (are) required to be achieved and suggested solutions/techniques to achieve them. The following white boxes represent the options for security requirements, and the grey boxes represent the options for the grey boxes. Integrity Integrity and authentication Confidentiality and Integrity Digital Signature Firewall IPSec Confidentiality and authentication Authentication Confidentiality Security requirement: Security solution: Symmetric Encryption and HMAC SSL/TLS PGP Kait Team Scenario 1 Susan is planning to steal Najla's credit card credentials that she uses for online shopping. Security requirement: Security solution: Scenario 2: Ghina is arranging for her graduation party and she is aware that her competitive colleague is planning to take her digital invitations and change the date/time of her party and send it on her behalf. Security requirement Security solution: Scenario 3: Leena and Lamis have email accounts from their company's email server. They have secret keys but they have doubts that the email administrator is reading and modifying their emails
Expert Answer:
Answer rating: 100% (QA)
The image youve provided displays a chart with various security requirements and solutions followed ... View the full answer

Related Book For 

Cornerstones of Financial and Managerial Accounting
ISBN: 978-1111879044
2nd edition
Authors: Rich, Jeff Jones, Dan Heitger, Maryanne Mowen, Don Hansen
Posted Date:
Students also viewed these programming questions
-
ABC Corp. makes products Alpha and Beta. Both products makes use of the same equipment. The following were provided to you with regard to these products in preparation for its budget next year. PESO...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
It is the post-apocalyptic era, and hardship and depression run rampant. You are currently at the bottom of a staircase in the basement of an abandoned building looking at what is pure...
-
The table contains real data. MySpace U.S. Advertising Revenue ($ millions) (a) Determine the maximum and minimum values for each variable in the table. (b) Use your results from part (a) to find an...
-
On January 5, 2014 Rita left the United States for Germany, where she had accepted an appointment as vice president of foreign operations. Her employer, USA Corporation, told her the assignment would...
-
The Food Shack Company's current net operating income is $6,400 and its average operating assets are $350,000. The Food Shack's required rate of return is 15%. A new project being considered would...
-
Equilibrium for extraction of acetic acid from 3-heptanol into water at \(25^{\circ} \mathrm{C}\) is \(\mathrm{y}=1.208 \mathrm{x}\), where \(\mathrm{y}=\) weight fraction acetic acid in water and...
-
Sycamore Plastics (SP) is a manufacturer of polyethylene plastic pellets used as a raw material by manufacturers of plastic goods around the U. S. SP currently operates four manufacturing centers in...
-
Based on your understanding of the tools and techniques used to establish continuous improvement initiative ,describe in detail the set of tools\techniques that you would use to improve the...
-
James Garage Ltd is a high end tire and rim sales company with installation and repair facilities. The following information can be obtained from the company's financial statements. James Garage Ltd...
-
On March 2 2 , purchased 8 0 0 shares of RPI Company stock at $ 1 1 per share. Duke's stock investment results in it having an insignificant influence over RPI. On July 1 , received a $ 2 per share...
-
What is the influence of monetary policies by major economies on emerging markets, especially in the context of financial crises ?
-
The fiscal 2018 financial statements of Walt Disney Co. show net operating profit margin (NOPM) of 5.73 %, net operating asset turnover (NOAT) of 1.28, return on equity of 6.6%, and adjusted return...
-
During 2020, Twitter, Inc. (NYSE:TWTR) will be issuing (approximately) $600 million of unsecured notes that will be due in 2027. Assume that on the day immediately before the note issuance, Twitter...
-
Martina Company is in the first year of building a storage facility that will contain hazardous building materials. The company is required to remove the storage facility and dispose of its contents...
-
Tobin's Frozen Pizza Inc. has determined from its production budget the following estimated production volumes for 12" and 16" frozen pizzas for November: Units 16" Pizza Budgeted production volume...
-
A process whose dynamics is described by a double integrator is controlled by an ideal PD controller with the transfer function C(s) = kas + kp, where the gains are ka = 25wo and kp = wf, and 0 < <...
-
Identify one local business that uses a perpetual inventory system and another that uses a periodic system. Interview an individual in each organization who is familiar with the inventory system and...
-
What are strategic risks?
-
Ein Company began operations in February 2011. Eins accounting records provide the following data for the remainder of 2011 for one of the items the company sells: Ein uses a perpetual inventory...
-
Refer to the information in Cornerstone Exercise 16-24 for data. Now, assume that Hallett has decided to use a plantwide overhead rate based on direct labor hours. At the beginning of the year,...
-
Define committed costs and provide two examples of committed costs?
-
ABC Framing has been hired to frame a light commercial building. The project began on July 2 and was completed on August 9. The following is a list of accounting transactions associated with the...
-
When calculating a ratio with numbers from the balance sheet and income statement, why must you use the balance sheets from the beginning and end of the period covered by the income statement?

Study smarter with the SolutionInn App