Question: Question 1 Q.1.1 Using an example for each of the different types of social engineering approaches, explain what is and how each can be
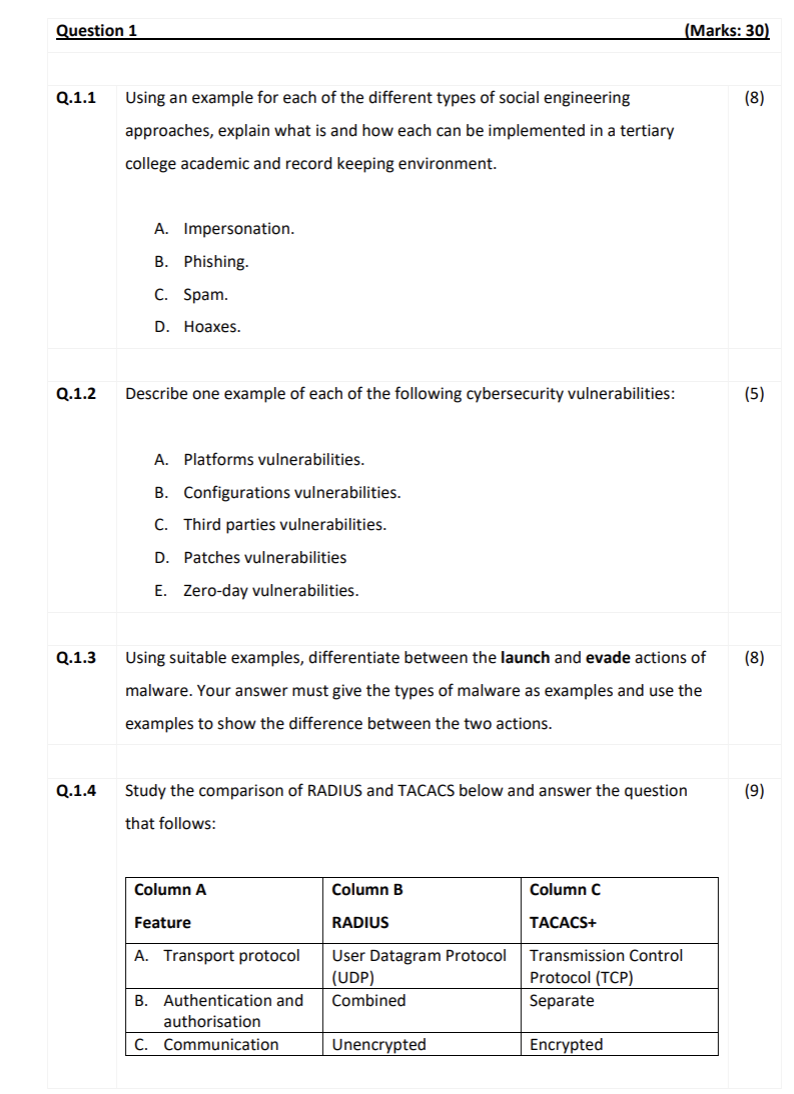
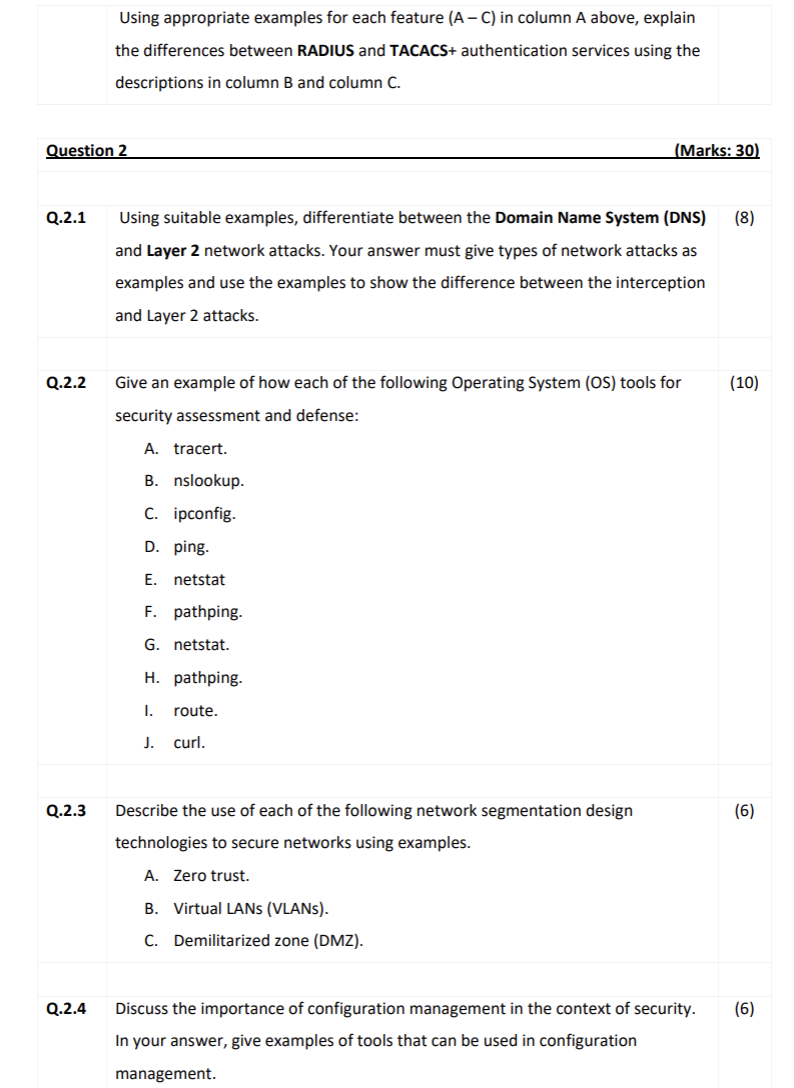
Question 1 Q.1.1 Using an example for each of the different types of social engineering approaches, explain what is and how each can be implemented in a tertiary college academic and record keeping environment. Q.1.2 Q.1.3 Q.1.4 A. Impersonation. B. Phishing. C. Spam. D. Hoaxes. Describe one example of each of the following cybersecurity vulnerabilities: A. Platforms vulnerabilities. B. Configurations vulnerabilities. C. Third parties vulnerabilities. D. Patches vulnerabilities E. Zero-day vulnerabilities. Using suitable examples, differentiate between the launch and evade actions of malware. Your answer must give the types of malware as examples and use the examples to show the difference between the two actions. Study the comparison of RADIUS and TACACS below and answer the question that follows: Column A Feature A. Transport protocol B. Authentication and authorisation C. Communication Column B RADIUS User Datagram Protocol (UDP) Combined Unencrypted (Marks: 30) Column C TACACS+ Transmission Control Protocol (TCP) Separate Encrypted (8) (5) (8) (9) Question 2 Q.2.1 Q.2.2 Q.2.3 Using appropriate examples for each feature (A-C) in column A above, explain the differences between RADIUS and TACACS+ authentication services using the descriptions in column B and column C. Q.2.4 (Marks: 30) Using suitable examples, differentiate between the Domain Name System (DNS) (8) and Layer 2 network attacks. Your answer must give types of network attacks as examples and use the examples to show the difference between the interception and Layer 2 attacks. Give an example of how each of the following Operating System (OS) tools for security assessment and defense: A. tracert. B. nslookup. C. ipconfig. D. ping. E. netstat F. pathping. G. netstat. H. pathping. I. route. J. curl. Describe the use of each of the following network segmentation design technologies to secure networks using examples. A. Zero trust. B. Virtual LANs (VLANs). C. Demilitarized zone (DMZ). Discuss the importance of configuration management in the context of security. In your answer, give examples of tools that can be used in configuration management. (10) (6) (6)
Step by Step Solution
3.34 Rating (151 Votes )
There are 3 Steps involved in it
Based on the image provided here are the answers to the questions Q11 Social Engineering in an Academic Environment A Impersonation An attacker could pretend to be a member of the IT staff claiming th... View full answer

Get step-by-step solutions from verified subject matter experts


