Question: Question 1 Q.1.1 Using suitable examples, discuss how you would use the three information security (12) layers to secure a student information database for
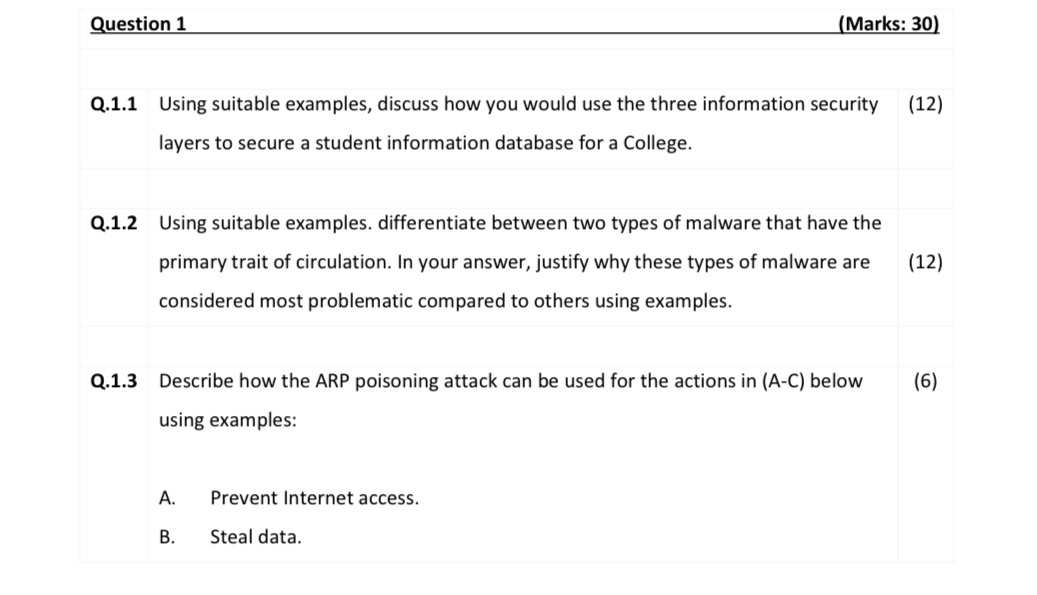
Question 1 Q.1.1 Using suitable examples, discuss how you would use the three information security (12) layers to secure a student information database for a College. Q.1.2 Using suitable examples. differentiate between two types of malware that have the primary trait of circulation. In your answer, justify why these types of malware are considered most problematic compared to others using examples. (Marks: 30) Q.1.3 Describe how the ARP poisoning attack can be used for the actions in (A-C) below using examples: A. B. Prevent Internet access. Steal data. (12) (6)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


