Question: Question 1 Students should read each question carefully and choose the ONE best answer from the table to fill in the blank. Each question carries
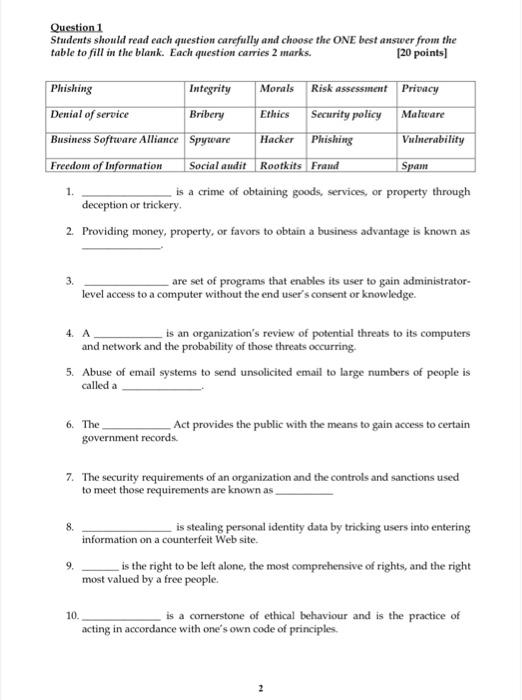
Question 1 Students should read each question carefully and choose the ONE best answer from the table to fill in the blank. Each question carries 2 marks. [20 points) Phishing Integrity Morals Risk assessment Privacy Denial of service Bribery Ethics Security policy Malware Business Software Alliance Spyware Hacker Phishing Vulnerability Freedom of Information Social audit Rootkits Fraud Spam is a crime of obtaining goods, services, or property through deception or trickery. 2. Providing money, property, or favors to obtain a business advantage is known as 1. 3 are set of programs that enables its user to gain administrator- level access to a computer without the end user's consent or knowledge. 4. A is an organization's review of potential threats to its computers and network and the probability of those threats occurring 5. Abuse of email systems to send unsolicited email to large numbers of people is called a 6. The Act provides the public with the means to gain access to certain government records 7. The security requirements of an organization and the controls and sanctions used to meet those requirements are known as 8. is stealing personal identity data by tricking users into entering information on a counterfeit Web site. is the right to be left alone, the most comprehensive of rights, and the right most valued by a free people. 9. 10. is a cornerstone of ethical behaviour and is the practice of acting in accordance with one's own code of principles
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


