Question: QUESTION 1 The asymmetric key cryptography, it also called public key cryptography where is private saved in Sender O Receiver sender and receiver All the
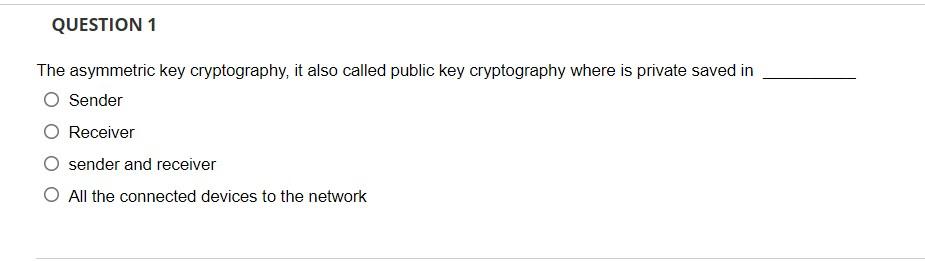
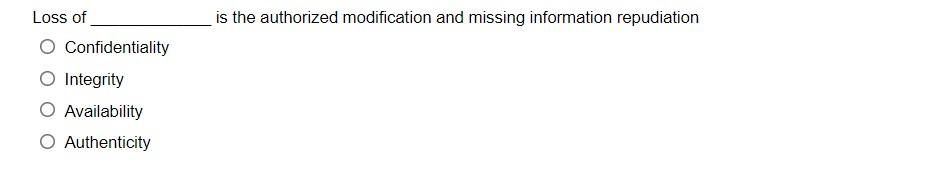
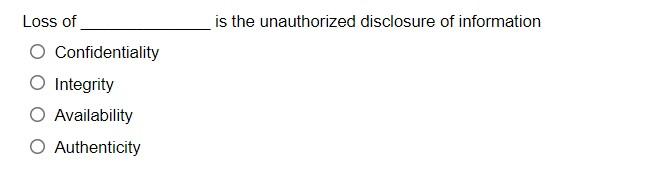
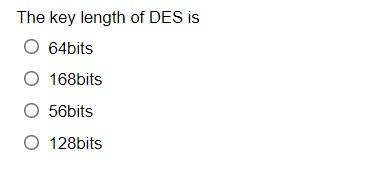
QUESTION 1 The asymmetric key cryptography, it also called public key cryptography where is private saved in Sender O Receiver sender and receiver All the connected devices to the network Loss of is the authorized modification and missing information repudiation Confidentiality Integrity Availability O Authenticity Loss of is the unauthorized disclosure of information O Confidentiality Integrity Availability Authenticity The key length of DES is O 64bits O 168bits O 56bits 0128bits possible attack approach to RSA security is O brute force search mathematic attacks timing attacks O All of above
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


