Question: A user receives this error message: CA Not Secure https://w What is the cause? What is the cause? SSL certificate is invalid or self-signed
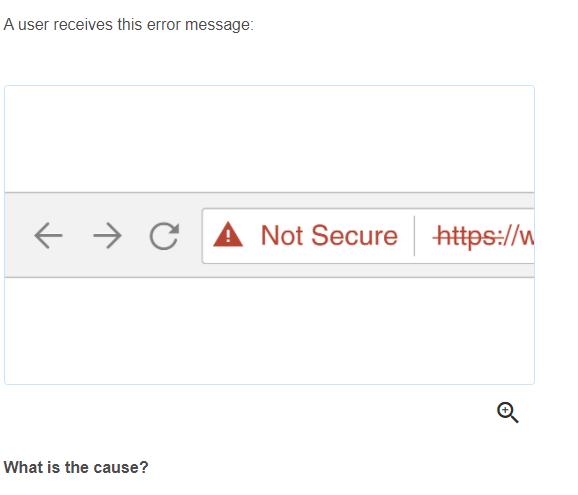
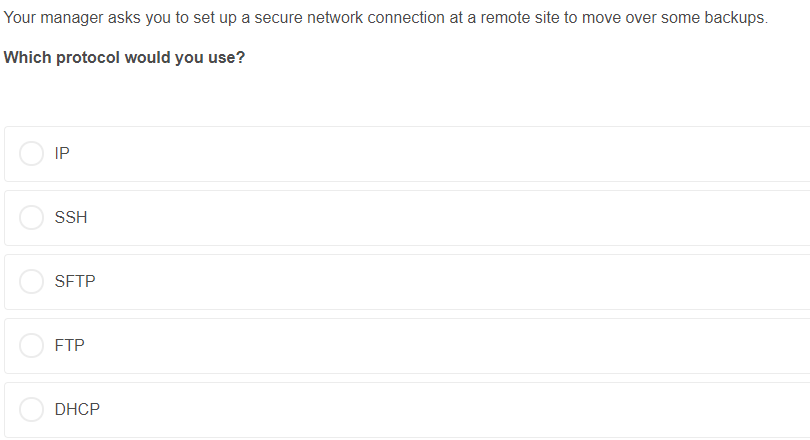
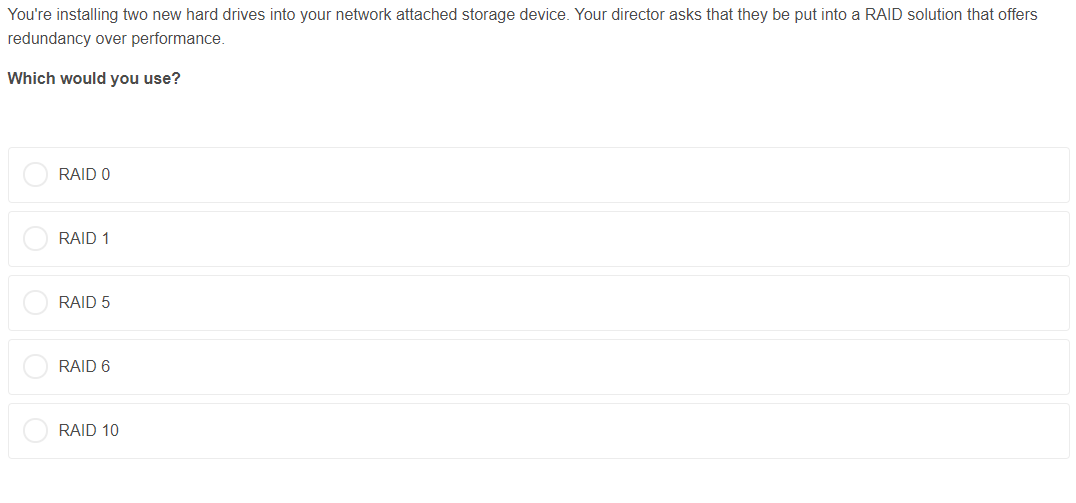
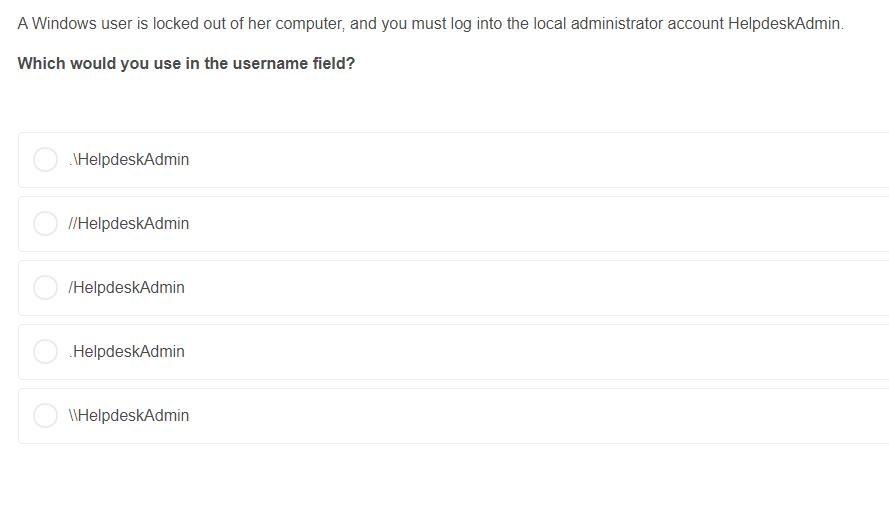
A user receives this error message: CA Not Secure https://w What is the cause? What is the cause? SSL certificate is invalid or self-signed User needs to change the URL to http:// from https:// Web server doesn't support HTTPS sites Domain is improperly configured at the registrar User's browser doesn't support secure websites The web development team is having difficulty connecting by SSH to your local web server, and you notice the proper rule is missing from the firewall. What port number would you open on your webserver? Port 21 Port 22 Port 25 Port 80 Port 443 Your internet is out, and devices connected by WiFi and ethernet will not connect. You check several websites, and all your packets fail. You then ping a website with an IP address, and to your surprise, it's a success. Which would you do next? Open the Network settings on your router and try turning off your firewall Open the DNS settings on your router and try using a different DNS Open the DHCP settings on your router and try using a different pool of private IP addresses Open the Port Forwarding settings on your router and try turning on UPnP Open the Network settings on your router and try adjusting the default gateway Your manager asks you to set up a secure network connection at a remote site to move over some backups. Which protocol would you use? IP SSH SFTP FTP DHCP You're installing two new hard drives into your network attached storage device. Your director asks that they be put into a RAID solution that offers redundancy over performance. Which would you use? RAID 0 RAID 1 RAID 5 RAID 6 RAID 10 A Windows user is locked out of her computer, and you must log into the local administrator account HelpdeskAdmin. Which would you use in the username field? \HelpdeskAdmin //HelpdeskAdmin /HelpdeskAdmin .HelpdeskAdmin \\HelpdeskAdmin
Step by Step Solution
3.41 Rating (160 Votes )
There are 3 Steps involved in it
The detailed answer for the above question is provided below 1 What is the cause Ans A SSL certificate is invalid or selfsigned Explanation The most common cause for a website to show Not Secure is th... View full answer

Get step-by-step solutions from verified subject matter experts


