Question: Question 14 Which statement about the security (harming) model is actually false? Not yet answered Select one: Marked out of 1 a. Risks can be
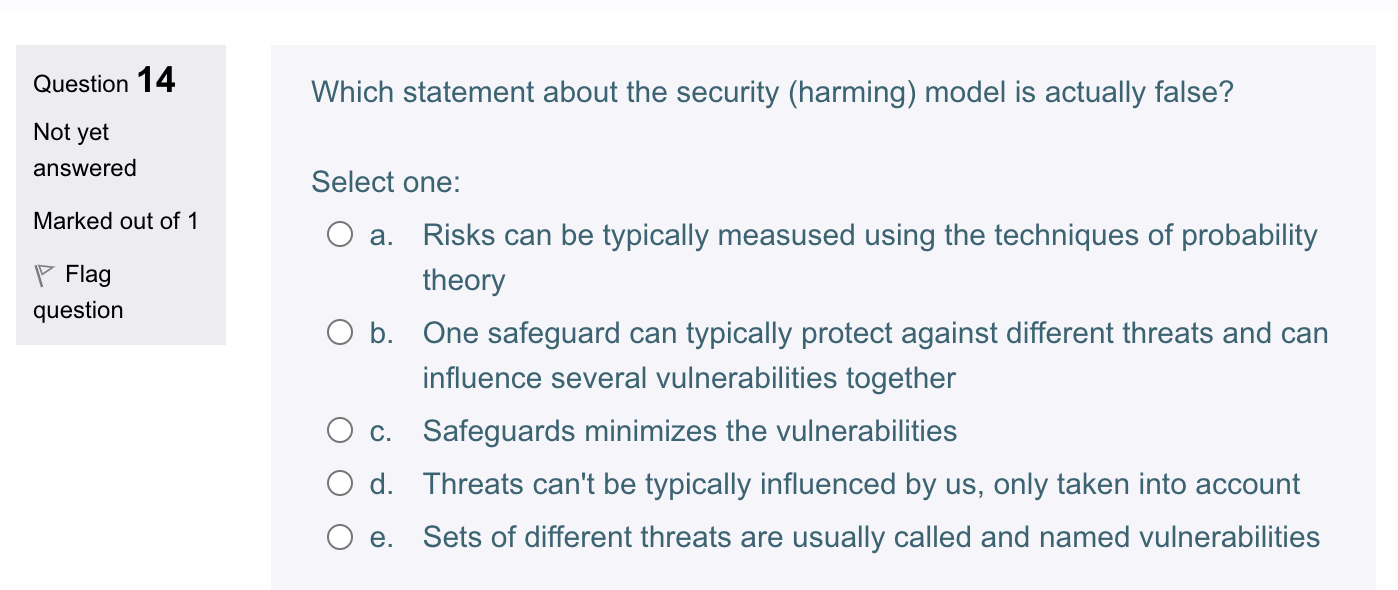
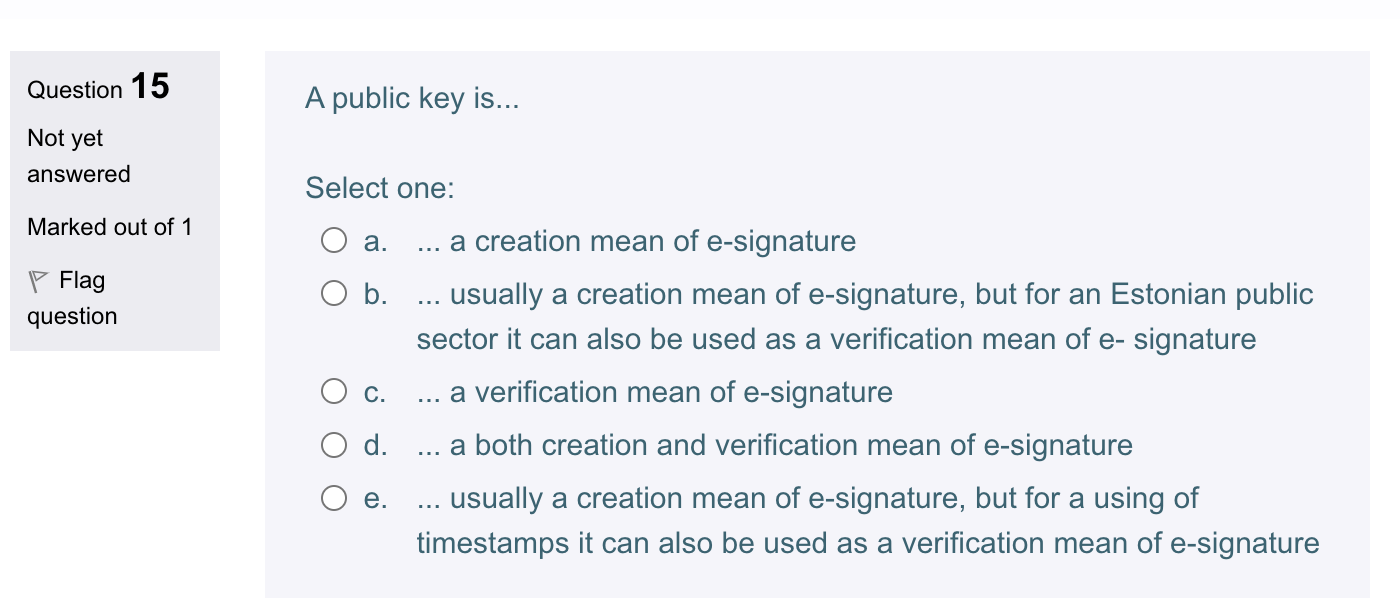
Question 14 Which statement about the security (harming) model is actually false? Not yet answered Select one: Marked out of 1 a. Risks can be typically measused using the techniques of probability theory b. One safeguard can typically protect against different threats and can influence several vulnerabilities together c. Safeguards minimizes the vulnerabilities d. Threats can't be typically influenced by us, only taken into account e. Sets of different threats are usually called and named vulnerabilities Question 15 A public key is... Not yet answered Select one: Marked out of 1 a. ... a creation mean of e-signature b. ... usually a creation mean of e-signature, but for an Estonian public sector it can also be used as a verification mean of e- signature c. ... a verification mean of e-signature d. ... a both creation and verification mean of e-signature e. ... usually a creation mean of e-signature, but for a using of timestamps it can also be used as a verification mean of e-signature
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


