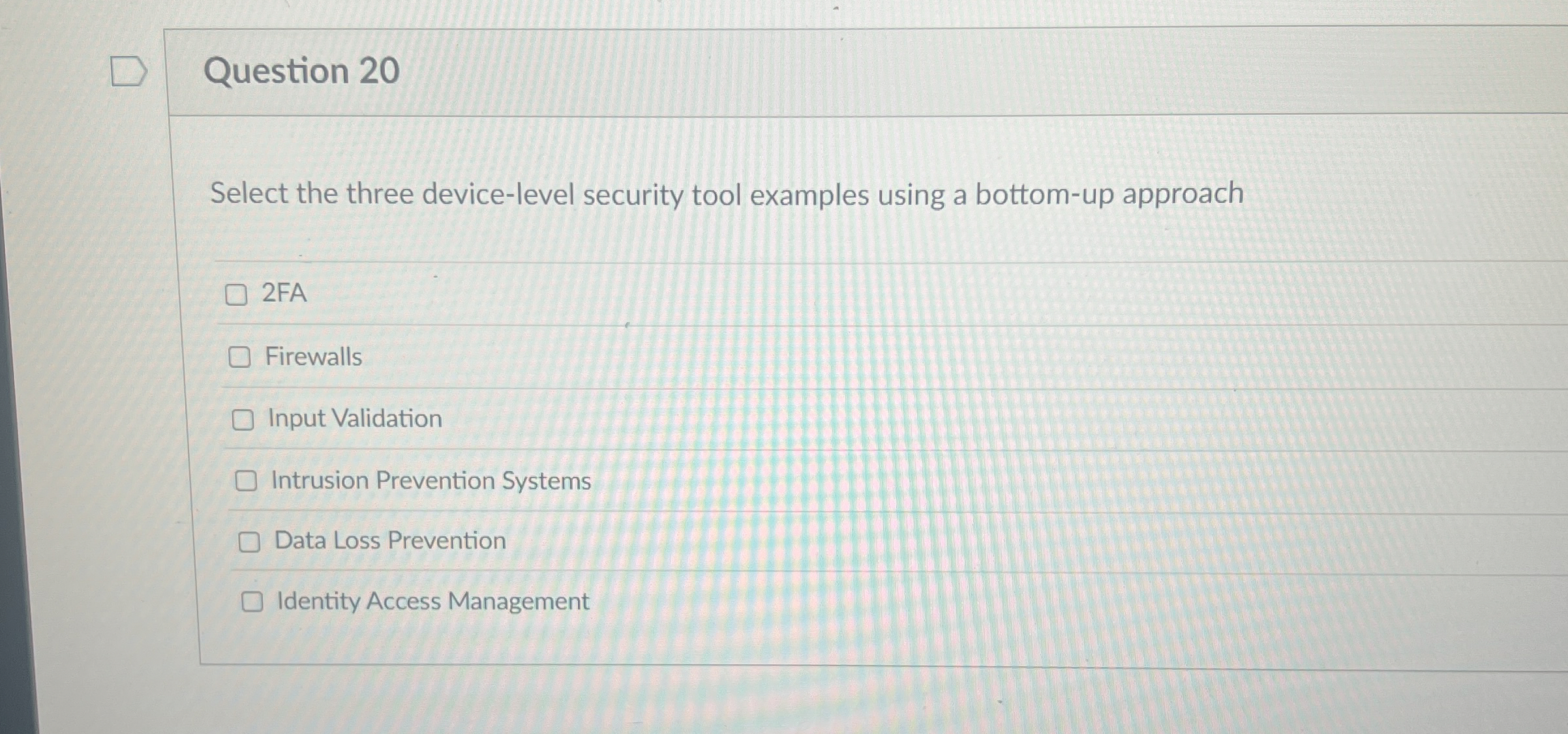
Question: Question 2 0 Select the three device - level security tool examples using a bottom - up approach 2 FA Firewalls Input Validation Intrusion Prevention
Question
Select the three devicelevel security tool examples using a bottomup approach
FA
Firewalls
Input Validation
Intrusion Prevention Systems
Data Loss Prevention
Identity Access Management
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


