Question: Question 2 Using a Phishing email to breach a target network and install malware on a computer is example of what stag of the cyber
Question
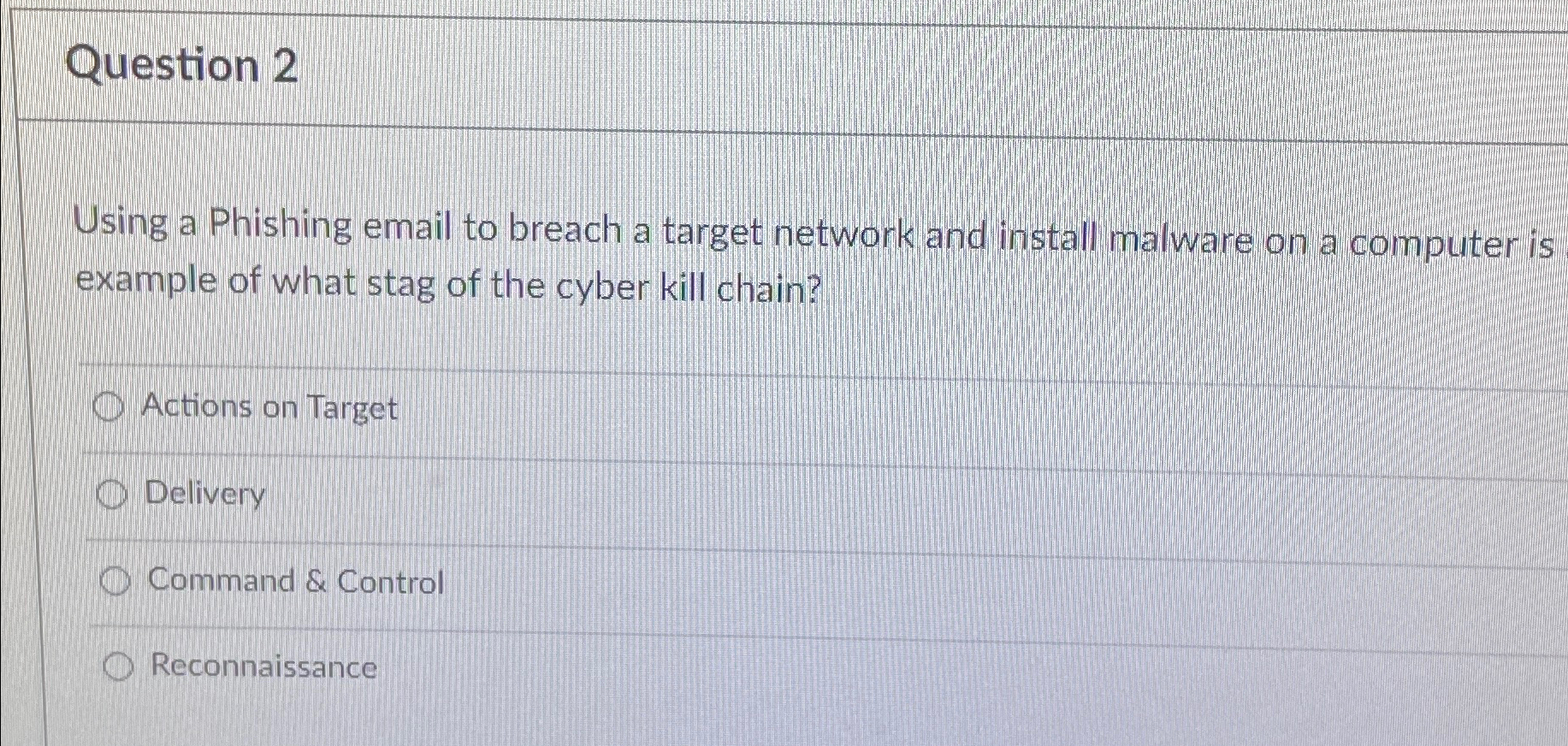
Using a Phishing email to breach a target network and install malware on a computer is example of what stag of the cyber kill chain?
Actions on Target
Delivery
Command & Control
Reconnaissance
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


