Question: Question 3 7 ( 2 points ) Listen A step commonly used for Internet vulnerability assessment includes which occurs when the penetration test engine is
Question points
Listen
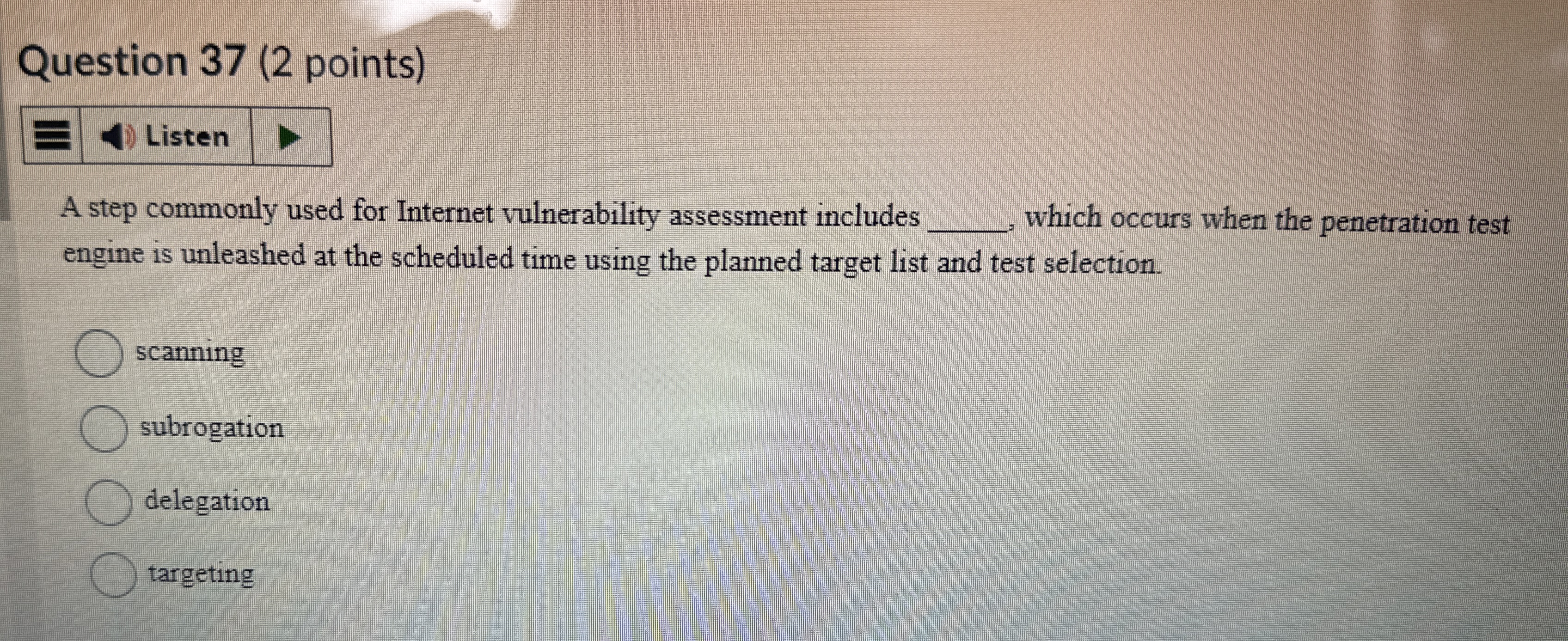
A step commonly used for Internet vulnerability assessment includes which occurs when the penetration test engine is unleashed at the scheduled time using the planned target list and test selection.
scanning
subrogation
delegation
targeting
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


